A large-scale coordinated campaign has been detected targeting Microsoft Remote Desktop Protocol (RDP) services, where attackers deployed more than 30,000 unique IP addresses to probe for weaknesses in RD Web Access and RDP Web Client authentication portals.
Security analysts warn that this represents one of the largest RDP reconnaissance operations in recent years, suggesting that cybercriminals may be preparing for credential-focused attacks such as password spraying, credential stuffing, or ransomware deployment.
Key Highlights
- Over 30,000 IPs participated, marking the largest observed Microsoft RDP scanning operation.
- US schools were targeted during the back-to-school season, with username enumeration attempts.
- Intelligence analysis suggests an 80% likelihood of major exploits emerging soon.
Escalation of the Attack
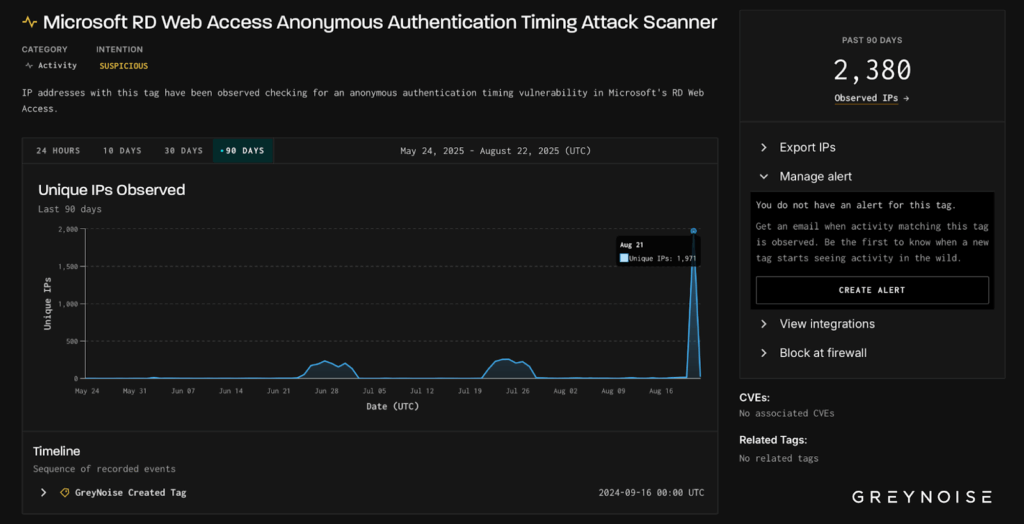
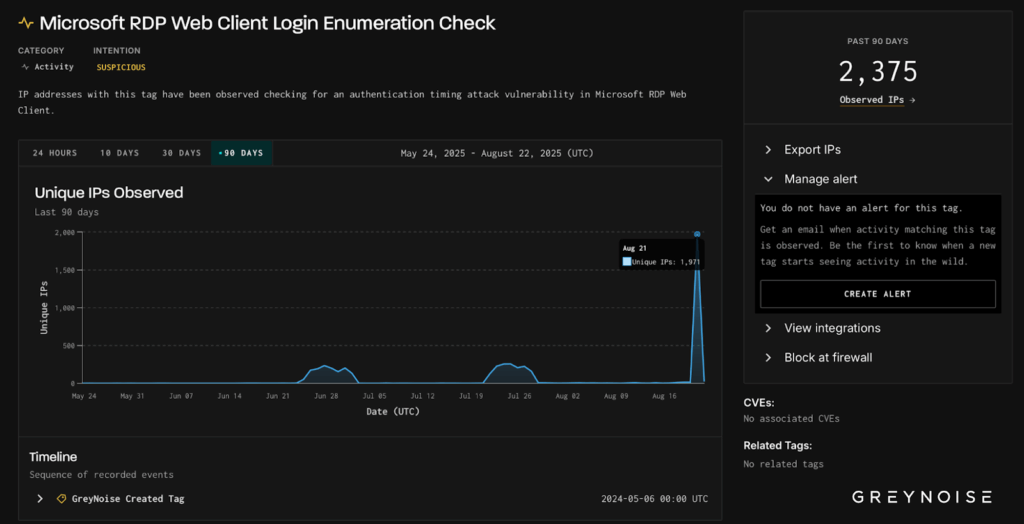
The first wave of activity was recorded on August 21, 2025, involving nearly 2,000 IP addresses that probed both RD Web Access and RDP Web Client systems.
By August 24, the activity had intensified significantly, with more than 30,000 IPs launching synchronized probes. Researchers discovered identical client signatures across these sources, suggesting either a sophisticated botnet or a centralized toolset deployment.
Attack Methodology
Reports from GreyNoise confirm that the attackers relied on timing-based authentication enumeration. This method leverages minor server response time differences to determine whether a username is valid, without triggering standard brute-force defenses.
Such tactics enable adversaries to quietly compile lists of valid usernames, later used in credential stuffing or password spraying campaigns.
Telemetry analysis further revealed:
- 92% of IPs involved had already been flagged as malicious.
- 73% of the traffic originated from Brazil, yet exclusively targeted US-based RDP endpoints.
- 1,851 out of 1,971 initial scanning hosts shared uniform client signatures, consistent with APT-style coordination.
Targeting the Education Sector
The timing aligns with the US back-to-school period, when universities and schools typically activate RDP-based labs and remote systems for students.
Attackers exploited the fact that educational networks often use predictable username formats (such as studentID or firstname.lastname), making them prime candidates for enumeration attacks.
The reconnaissance is being conducted in multiple stages:
- Identifying exposed RDP endpoints.
- Probing authentication processes for vulnerabilities.
- Collecting valid usernames and compiling target databases.
Broader Threat Landscape
Interestingly, the same infrastructure was also observed scanning for open proxy services and web crawling tasks, hinting at a multi-purpose toolkit for large-scale reconnaissance.
Historical data shows that such spikes in scanning activity often precede zero-day discovery or exploitation within six weeks, with an 80% correlation rate.
Experts warn that the scale and organization of this campaign could be a precursor to ransomware attacks, credential theft, or even new RDP zero-day exploitation.
Organizations using Microsoft RDP services are strongly advised to apply hardening measures immediately and monitor for client signature-based follow-up activity.


