A critical security flaw affecting 7-Zip, tracked as CVE-2025-11001, is currently being actively exploited in the wild. The issue allows remote code execution via symbolic links in ZIP archives and impacts versions prior to 25.00, which was released in July 2025.
Details of the Vulnerability
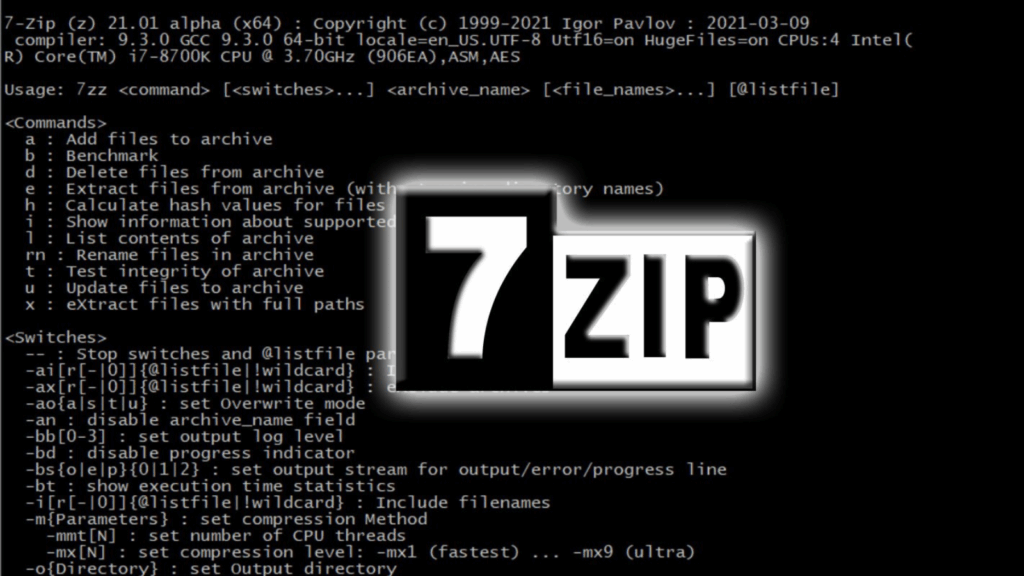
The vulnerability arises from improper handling of symbolic links in ZIP files. Crafted ZIP archives can force the extraction process to traverse unintended directories, allowing attackers to execute arbitrary code within the context of a service or elevated account.
According to Trend Micro’s Zero Day Initiative (ZDI), attackers can leverage this flaw to execute code in Windows systems specifically, making it highly relevant for enterprise and personal users alike.
Discovery and Reporting
Ryota Shiga of GMO Flatt Security Inc., together with the AI-powered AppSec Auditor Takumi, discovered and responsibly reported the vulnerability. The PoC released by security researcher Dominik (aka pacbypass) demonstrates the issue on Windows, emphasizing that exploitation requires either an elevated user account, service account, or a developer mode enabled machine.
Additional Related Vulnerability
7-Zip 25.00 also addresses CVE-2025-11002, another symbolic link–based remote code execution vulnerability introduced in version 21.02. Both flaws are linked to ZIP file directory traversal, highlighting the criticality of applying updates immediately.
Impact and Mitigation
The U.K. NHS England Digital advisory confirms that CVE-2025-11001 is actively exploited in the wild. While the exact threat actors and attack vectors remain unclear, proof-of-concept exploits are publicly available, which increases the urgency of patching.
Users should update to 7-Zip 25.00 or later without delay. Ensuring that extraction processes run under minimal privilege accounts can further reduce potential attack impact.