A new large-scale cybercrime operation known as ClickTok has surfaced, aiming at TikTok Shop users through a complex mix of phishing and malware distribution. Security researchers have discovered over 10,000 malicious domains involved in stealing login credentials and deploying spyware.
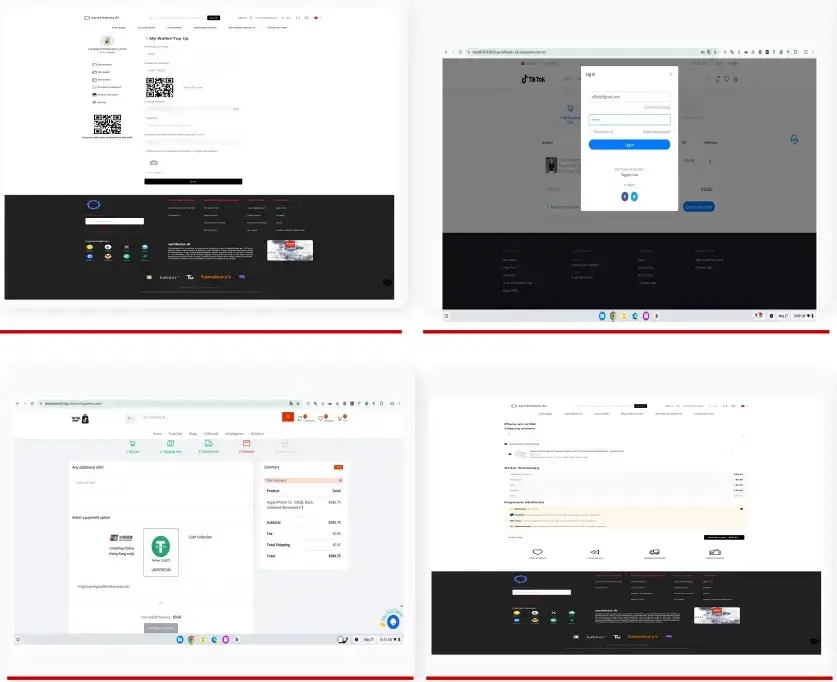
The campaign marks a significant rise in e-commerce cyberattacks, leveraging the popularity of TikTok’s in-app shopping feature to lure both casual shoppers and affiliate marketers. Fraudulent websites are designed to closely replicate TikTok Shop, including fake versions of TikTok Wholesale and TikTok Mall, creating an entire ecosystem of malicious storefronts.
First identified by CTM360 in August 2025, ClickTok exploits the trust users place in TikTok and the financial appeal of affiliate programs. The attackers are using more than 5,000 fake app download pages, many embedded with QR codes and download links, to distribute trojanized applications.
These apps are hosted on domains using cheap TLDs like .top, .shop, and .icu. Many of these domains are deployed on free or shared hosting services, allowing the campaign to scale rapidly while remaining difficult to trace.
To extend their reach, the attackers also use AI-generated content and fake ads on social media platforms. This expands their victim pool far beyond the 17 countries where TikTok Shop officially operates.
Spyware Capabilities and Command & Control Infrastructure
The malware distributed via ClickTok contains a modified version of SparkKitty spyware, which maintains persistent contact with attacker-controlled servers.
A key detail from the malware’s code includes a hardcoded command-and-control (C2) URL:
URL url = new URL("https://aa.6786587.top/?dev=az");
This static approach to C2 communication indicates that the malware may still be in early development, as advanced threats typically use dynamic infrastructure for resilience.
Once installed, the malware sends POST and GET requests containing stolen TikTok user IDs and session tokens like PHPSESSID to the attacker’s servers. In return, it receives Base64-encoded payloads with updated configurations and attack instructions tailored for each infected device.
Its main purpose is data exfiltration, particularly targeting:
- Cryptocurrency seed phrases
- Wallet screenshots
- Device fingerprinting data (OS, device ID, location)
It systematically scans galleries for sensitive images and collects device metadata to send back to the attacker’s C2 servers.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


