Hackers Can Exploit New Win-DDoS Flaws to Turn Public Domain Controllers into Powerful Botnets
A newly discovered attack method could be used to hijack thousands of publicly accessible Domain Controllers (DCs) worldwide, transforming them into a massive botnet capable of delivering high-powered Distributed Denial-of-Service (DDoS) attacks.
The technique, named Win-DDoS, was uncovered by SafeBreach researchers Or Yair and Shahak Morag, who shared their findings at the DEF CON 33 security conference.
“We found a flaw in the Windows LDAP client code that lets us manipulate the URL referral process, directing Domain Controllers to a victim server and overwhelming it,” the researchers explained in a report published by The Hacker News.
By exploiting this weakness, attackers could assemble a botnet made entirely of legitimate Windows DCs — without buying servers, installing malware, or leaving a clear trace.
How the Win-DDoS Attack Works
The attack does not require code execution or stolen credentials. Instead, it turns Windows systems into both the target and the weapon.
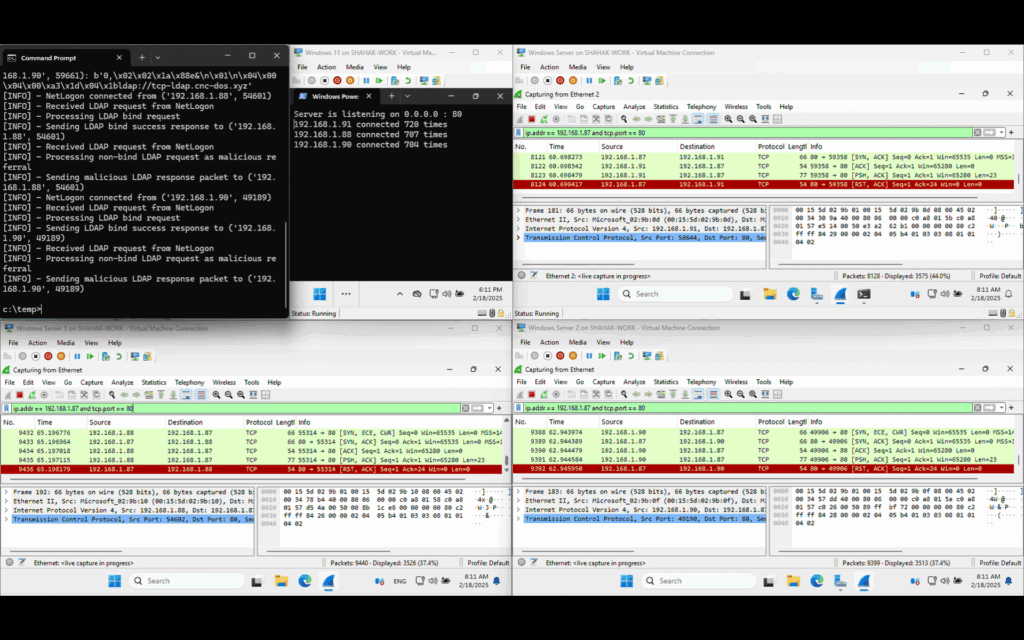
Step-by-step process:
- The attacker sends an RPC call to target DCs, making them act as CLDAP clients.
- The DCs send a CLDAP request to the attacker’s CLDAP server, which responds with a referral to the attacker’s LDAP server.
- This forces a switch from UDP to TCP connections.
- The attacker’s LDAP server replies with a referral list containing many identical URLs pointing to a single port and IP.
- The DCs send repeated LDAP queries to that port, overloading the victim server.
When the TCP connection closes, the DC immediately tries the next referral — which again points to the attacker’s chosen server. This loop continues until the list is exhausted, creating a persistent and high-bandwidth attack.
Why This Method is Dangerous
- No Infrastructure Costs: The botnet consists of legitimate DCs already connected to the internet.
- No Device Breach Required: The attacker does not need to hack into each DC.
- Difficult to Detect: The activity appears as normal network traffic.
Researchers also discovered that by sending extra-long referral lists, attackers can cause:
- LSASS process crashes
- System reboots
- Blue Screen of Death (BSoD)
These issues arise because Windows imposes no size limits on referral lists, and memory from the DC’s heap is not released until data retrieval completes.
Additional DoS Vulnerabilities Found
While analyzing the process, SafeBreach identified four denial-of-service (DoS) flaws in Windows components:
- CVE-2025-26673 (CVSS 7.5) – LDAP uncontrolled resource consumption, exploitable without authentication. (Patched May 2025)
- CVE-2025-32724 (CVSS 7.5) – LSASS uncontrolled resource consumption, exploitable without authentication. (Patched June 2025)
- CVE-2025-49716 (CVSS 7.5) – Netlogon uncontrolled resource consumption, exploitable without authentication. (Patched July 2025)
- CVE-2025-49722 (CVSS 5.7) – Print Spooler uncontrolled resource consumption, requires adjacent network access. (Patched July 2025)
Lessons for Enterprises
The Win-DDoS research highlights that:
- DoS risks are not limited to public-facing systems.
- Even internal systems can be abused without full compromise.
- Risk models need to account for zero-click, unauthenticated threats.
“These findings break common enterprise security assumptions,” the researchers warned. “Private infrastructure can be weaponized without a breach, making resilience and defense strategies more critical than ever.”