SSHamble – An Advanced Open-Source Tool for Uncovering SSH Vulnerabilities
SSHamble is a cutting-edge open-source reconnaissance utility built to detect and exploit security weaknesses in SSH protocol implementations across internet-facing systems.
First showcased at DEFCON 33, the tool has already revealed major flaws in enterprise networking equipment and exposed widespread SSH misconfigurations impacting millions of systems globally.
How SSHamble Works
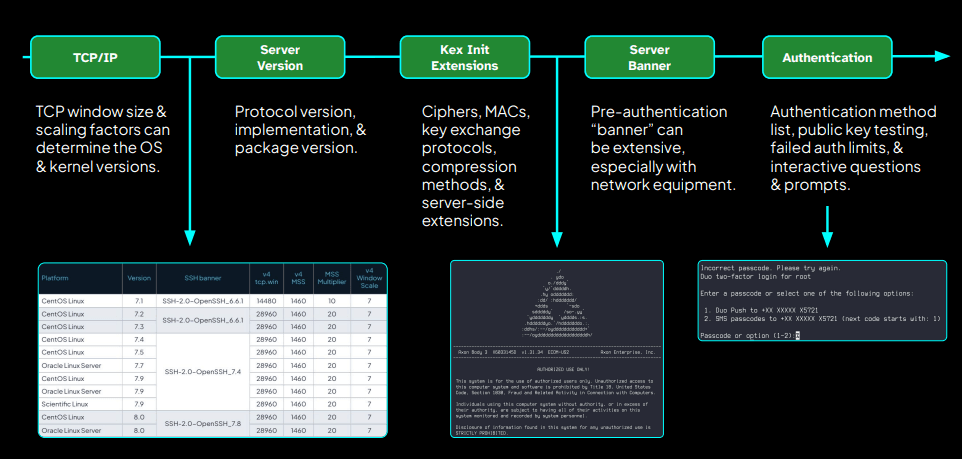
SSHamble performs comprehensive pre-authentication analysis of SSH servers, investigating:
- Protocol negotiations
- Authentication methods
- Implementation-specific behaviors
Key Points:
- SSHamble is an open-source tool designed to identify vulnerabilities in the SSH protocol.
- It has discovered zero-day flaws in enterprise-grade networking devices.
- Version 2.0 includes 30+ vulnerability checks to help organizations mitigate SSH risks.
Using methods such as kex init parsing, authentication bypass testing, and timing analysis, SSHamble can detect misconfigurations without the need for valid credentials.
Critical Security Findings
Cybersecurity researcher HDMoore used SSHamble to uncover severe zero-day vulnerabilities, including:
- Unauthenticated root command execution in Ruckus Wireless access points
- Unauthenticated remote CLI access in Digi TransPort gateways and Panasonic Ethernet switches
- Authenticated remote code execution in Git hosting platforms like GOGS and Soft Serve
Internet-Wide Exposure Statistics
During large-scale scanning, SSHamble found:
- Around 22 million IPv4 addresses with SSH open on port 22
- 15.4 million of those completing SSH protocol negotiation
- 48,000 systems where sessions were established, indicating possible authentication bypass or credential compromise
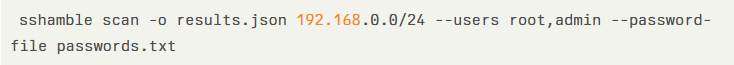
SSHamble’s 30+ built-in checks include techniques like auth-none, skip-auth, pubkey-any, and vuln-tcp-forward. The tool can also execute targeted commands.
SSHamble v2.0 – New Features
The latest release, SSHamble 2.0, brings:
- Automatic BadKeys.info blocklist lookups
- Experimental blind execution checks
- Integration with Nuclei for extended security workflows
- Wider algorithm negotiation testing
- Improved host key verification bypass methods
Moore’s analysis highlights serious flaws in embedded devices and network infrastructure, often caused by:
- Hardcoded credentials
- Reused host keys
- Pre-authentication port forwarding vulnerabilities
Security Recommendations
The research strongly advises organizations to:
- Audit SSH configurations regularly
- Enable PerSourcePenalties rate limiting (OpenSSH 9.8)
- Move away from password-based logins and adopt public key authentication with strong key management
SSHamble is available via its official website and is already integrated into popular security testing frameworks, enabling proactive detection of SSH weaknesses before cybercriminals exploit them.


