Cybersecurity researchers have identified a highly sophisticated malware distribution campaign that uses GitHub repositories disguised as legitimate software projects to infiltrate systems globally.
The operation leverages GitHub’s reputation as a trusted code-sharing platform, deploying SmartLoader malware across multiple repositories to target unsuspecting users.
Targeting Gaming and Software Enthusiasts
The malicious campaign specifically focuses on individuals searching for:
- Game cheats
- Software cracks
- Automation tools
By strategically positioning fake repositories at the top of GitHub search results, attackers significantly increase the chances of luring victims.
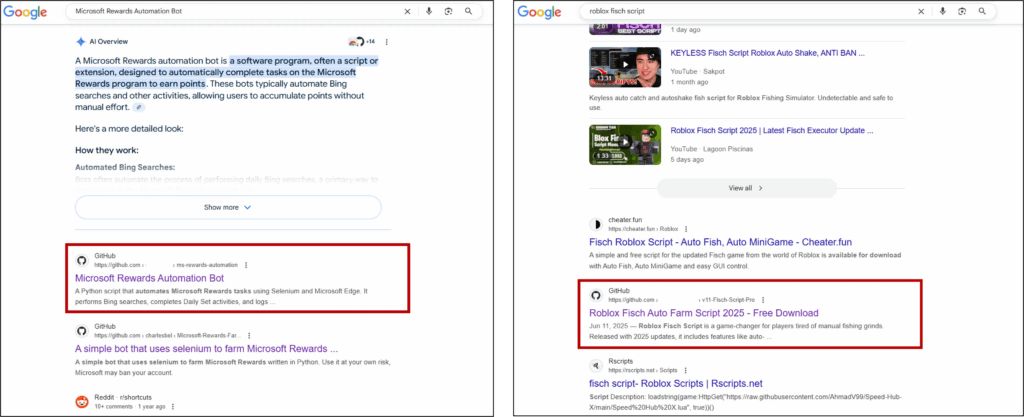
These repositories appear genuine, featuring:
- Professionally written README files
- Detailed project documentation
- Realistic file structures matching legitimate open-source projects
The level of detail makes these fraudulent repositories nearly indistinguishable from authentic software projects.
How the Infection Works
Each compromised repository contains compressed files hiding the SmartLoader payload. When downloaded and executed, these files initiate a multi-stage infection process that grants attackers persistent access to the victim’s system.
According to ASEC analysts, this method is especially dangerous because it exploits the trust of both the developer community and gaming enthusiasts who frequently use GitHub as a reliable source for tools.
Technical Breakdown – SmartLoader Deployment
The infection chain begins when users run the Launcher.cmd file, the initial attack vector.
This malicious batch file uses luajit.exe — a legitimate Lua interpreter — to execute an obfuscated Lua script.

The malware package contains:
- java.exe – Legitimate Lua loader
- Launcher.cmd – Malicious batch file
- lua51.dll – Luajit runtime interpreter
- module.class – Obfuscated Lua script
Persistence and Data Theft
Once executed, SmartLoader:
- Copies essential files to %AppData%\ODE3
- Registers itself in Windows Task Scheduler as SecurityHealthService_ODE3
- Captures screenshots and system information
- Sends the stolen data to command-and-control (C2) servers using Base64 encoding
Loader for Additional Malware
SmartLoader’s primary threat lies in its ability to deliver secondary payloads.
Analysis revealed it can download and run Rhadamanthys infostealer, a malware that steals sensitive data from:
- Email clients
- FTP applications
- Online banking services
The malware uses process injection into legitimate Windows executables like openwith.exe, dialer.exe, and dllhost.exe to evade detection.
Dynamic Command-and-Control Capabilities
SmartLoader communicates with C2 servers through encrypted channels. It receives JSON-formatted commands that define configurations and tasks, allowing attackers to:
- Change malware behavior in real time
- Deploy additional payloads based on system characteristics
Security Implications
This campaign serves as a warning to verify:
- Repository credibility
- Commit history
- Author authenticity
before downloading any GitHub-hosted software, especially tools related to gaming modifications or software cracking.