Palo Alto Networks Releases Comprehensive Malware Analysis Tutorial on Remcos RAT
Palo Alto Networks has published a highly detailed malware analysis tutorial, showcasing the dissection of a complex .NET-based loader that ultimately delivers the Remcos remote access trojan (RAT).
Abuse of Legitimate Environments
The case underlines a growing threat trend: adversaries increasingly misuse legitimate development frameworks, such as the Microsoft .NET runtime, to orchestrate multi-stage infection campaigns.
This specific sample demonstrated advanced evasion capabilities, including:
- Managed-to-unmanaged code transitions
- Runtime API resolution
- Process injection into benign executables
Attack Chain Overview
The infection begins with an obfuscated .NET executable, designed to appear harmless. This initial loader retrieves an online payload disguised as a PDF file hosted on a compromised Bitbucket repository.
Rather than a document, the file contains Donut-generated shellcode engineered for in-memory execution. By avoiding disk writes, the malware evades detection by traditional antivirus solutions dependent on static signatures.
During threat hunting operations, Palo Alto analysts uncovered the sample and highlighted its ability to shift execution across multiple runtime environments, a technique typical of advanced intrusion operations.
Payload Decoding and Execution
Once retrieved, the payload is ASCII-hex decoded into usable shellcode. Using .NET interop services, the loader dynamically calls Windows APIs, allocating memory with VirtualAlloc and copying the decoded shellcode.
This mix of obfuscated managed code and late-bound unmanaged calls hinders static detection, while runtime API resolution allows the attacker to omit suspicious imports from the Portable Executable (PE) header.
AMSI and ETW Bypass Mechanisms
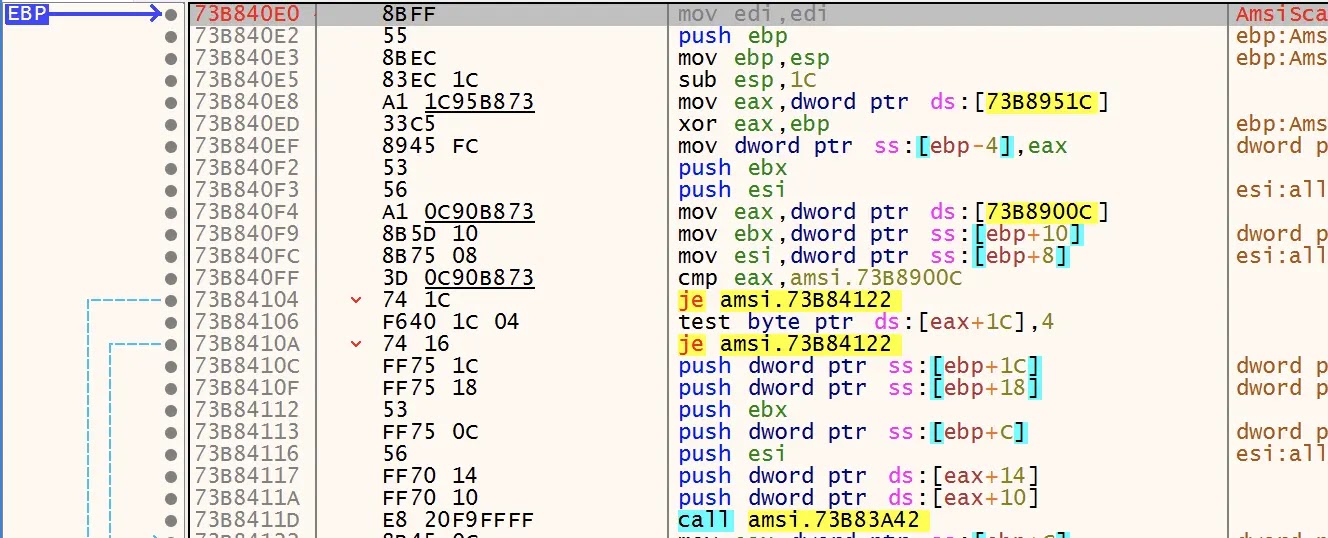
The payload contains anti-detection features, including:
- AMSI bypass: Patching AmsiScanBuffer in memory to always return clean results.
- ETW evasion: Replacing EtwEventWrite calls with a single return instruction, preventing monitoring systems from logging malicious behavior.
Code snippet from the AMSI patch:
byte[] patch = { 0x33, 0xC0, 0xC2, 0x18, 0x00 }; // xor eax,eax; ret 0x18
Marshal.Copy(patch, 0, amsiScanBufferPtr, patch.Length);These bypasses ensure that security monitoring tools fail to flag suspicious activity.
Runtime Hijacking with CLR Injection
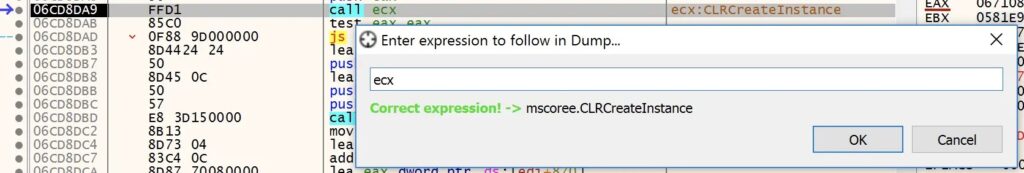
Another sophisticated step involves spawning a new .NET runtime instance from unmanaged shellcode using CLRCreateInstance and ICLRMetaHost::GetRuntime. The loader then injects an obfuscated .NET assembly into the runtime’s AppDomain.
The malware uses _Type.InvokeMember to call the entry point of the injected assembly, which launches InstallUtil.exe in a suspended state.
Persistence is achieved through process injection, where the decrypted Remcos RAT payload is written into the memory of InstallUtil.exe using WriteProcessMemory. After altering permissions with VirtualProtectEx, execution resumes.
This multi-chunk injection strategy helps evade memory scanners that focus on large, contiguous allocations.
Confirmation of Final Payload
Dynamic analysis confirmed the presence of the Remcos RAT ASCII banner embedded in the injected process.

Empowering Analysts with Practical Techniques
By explaining each stage — from initial obfuscation to payload activation — Palo Alto Networks’ tutorial not only reveals a real-world Remcos campaign but also provides practical methodologies that malware analysts can apply to investigate other hybrid-runtime malware samples.