A sophisticated phishing campaign is actively targeting Gmail users by exploiting legitimate Microsoft Dynamics infrastructure to bypass security protections and steal user credentials.
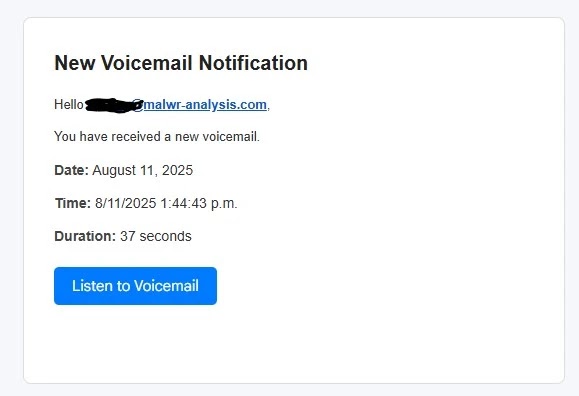
The scam begins with deceptive “New Voice Notification” emails, appearing to come from trusted voicemail services. These messages include spoofed sender details and prominent “Listen to Voicemail” buttons that redirect victims through a series of compromised websites.
<–image import–Voice mail Phishing–>
Attack Vector Using Trusted Platforms
The initial stage of the attack is hosted on Microsoft’s official Dynamics marketing platform (assets-eur.mkt.dynamics.com). By using a trusted domain, the attackers gain instant credibility and avoid typical email security filters that block suspicious domains.
Clicking the malicious link redirects victims to a CAPTCHA page hosted on horkyrown[.]com, a domain registered in Pakistan. The CAPTCHA creates the impression of legitimate security while functioning as part of the phishing infrastructure.
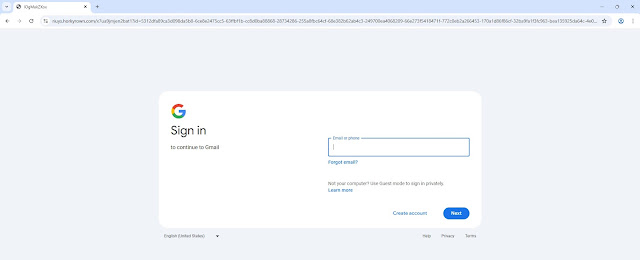
Replica Gmail Login Page
The final stage presents a highly accurate copy of Gmail’s login interface, complete with Google branding. This fake login form is designed to capture:
- Primary Gmail credentials
- Two-factor authentication codes
- Backup codes
- Security question answers
Advanced Evasion Techniques
Security analyst Anurag discovered that the JavaScript behind this phishing page is heavily obfuscated, using AES encryption to conceal its purpose. Anti-debugging features redirect users to the real Google login page if developer tools are opened.
The attack also uses multiple redirection layers and cross-site requests to servers in Russia (purpxqha[.]ru), revealing a complex international setup meant to evade detection and hinder forensic investigation.
All captured credentials are transmitted via encrypted channels to attacker-controlled servers, enabling rapid account compromise. The system targets a variety of Gmail security measures, including:
- Passwords and primary email
- SMS and voice verification codes
- Google Authenticator tokens
- Backup recovery codes
- Alternative email addresses
- Security question responses
Protecting Against This Threat
This phishing campaign highlights a new trend of combining social engineering with legitimate service abuse and technical evasion. Microsoft’s Dynamics platform is being exploited to gain user trust.
Users should carefully check unsolicited voicemail notifications and confirm login requests only through official channels.
Organizations should enhance email security protocols and train staff to recognize these threats.
The domain horkyrown[.]com, registered via Onamae[.]com in Karachi, Pakistan, is the primary attack infrastructure. Security teams should block this domain and watch for similar campaigns using legitimate marketing platforms.
Victims are advised to immediately change Google account passwords and review account activity to prevent further compromise.


