A new and highly deceptive phishing campaign is targeting Microsoft 365 accounts by abusing Microsoft’s own Active Directory Federation Services (ADFS). The attackers redirect users from legitimate office.com links to malicious login pages, making the scam exceptionally hard to detect.
Evolution of Phishing Attacks
Researchers at cybersecurity firm Push Security revealed this tactic, describing it as a major step forward in phishing operations. Unlike traditional phishing emails, this method bypasses both user awareness and common security defenses.
The attack relies on malvertising combined with clever manipulation of Microsoft’s infrastructure. For instance, a user searching for Office 365 may click on what appears to be a genuine search engine ad. That ad redirects them to a real outlook.office.com link, but the URL is crafted to activate the exploit.
Abuse of Microsoft ADFS
At the core of this attack is ADFS, a Microsoft feature designed for single sign-on (SSO). It normally connects an organization’s internal directory with cloud applications.
The attackers created their own Microsoft tenant and reconfigured its ADFS settings to redirect authentication requests to a phishing domain under their control.
This manipulation causes Microsoft’s servers to forward victims from the trusted office.com domain to a fake login portal that looks identical to the official Microsoft page. Push Security compared this trick to Outlook.com having an open redirect vulnerability.

ADFSjacking: Nearly Impossible to Detect
The technique, nicknamed “ADFSjacking”, is extremely dangerous because the redirect originates from a legitimate Microsoft source. This makes it almost undetectable by URL filtering systems and hard for cautious users to recognize.
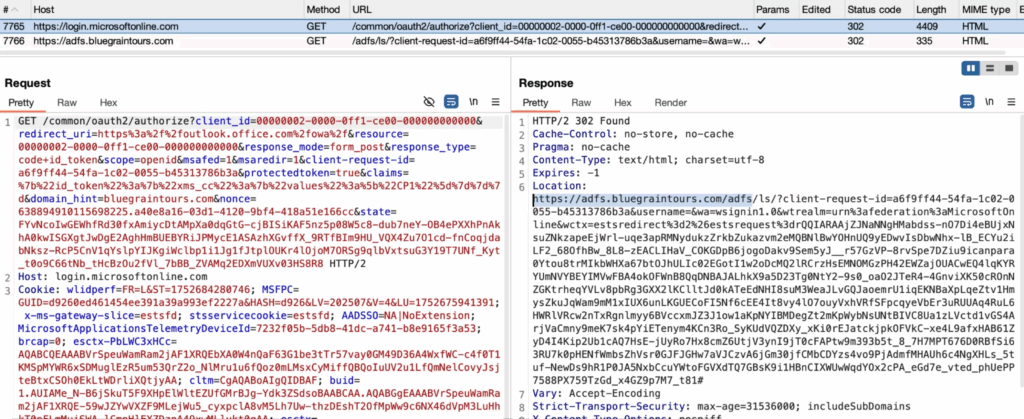
Investigations uncovered a multi-stage redirect chain. After clicking the ad, the user’s browser first passes through an intermediary website, sometimes disguised as an unrelated blog, before landing on the phishing site.
This step helps bypass automated domain categorization tools, which may mark the middle site as harmless, allowing the attack to slip through web filters.
Attacker-in-the-Middle Technique
Once the victim reaches the fake Microsoft login page, which operates as an Attacker-in-the-Middle (AitM) proxy, any credentials entered are immediately stolen.
Even worse, this setup lets attackers capture session cookies, enabling them to bypass multi-factor authentication (MFA) and gain complete access to the compromised account.
Shift in Phishing Delivery Methods
This campaign shows a broader trend: attackers are moving away from email-based phishing and instead exploiting channels like malvertising, social media, and instant messaging. This shift helps them bypass email security systems that organizations have heavily invested in.
Defense and Mitigation Strategies
To reduce risk, security experts recommend:
- Monitoring network logs for unusual ADFS redirects, especially those pointing to unknown domains.
- Filtering Google Ad parameters in traffic directed toward office.com to catch malicious campaigns.
- Encouraging end-users to install and maintain a reliable ad blocker across all browsers.


