A sophisticated malware loader known as QuirkyLoader has emerged as a serious cyber threat, actively spreading prominent infostealers and remote access trojans (RATs) since November 2024.
This malware stands out due to its ability to deliver multiple types of malicious payloads, including Agent Tesla, AsyncRAT, FormBook, MassLogger, Remcos, Rhadamanthys, and Snake Keylogger, making it a versatile tool for cybercriminals to execute varied attack scenarios on different targets.
Multi-Stage Infection Strategy
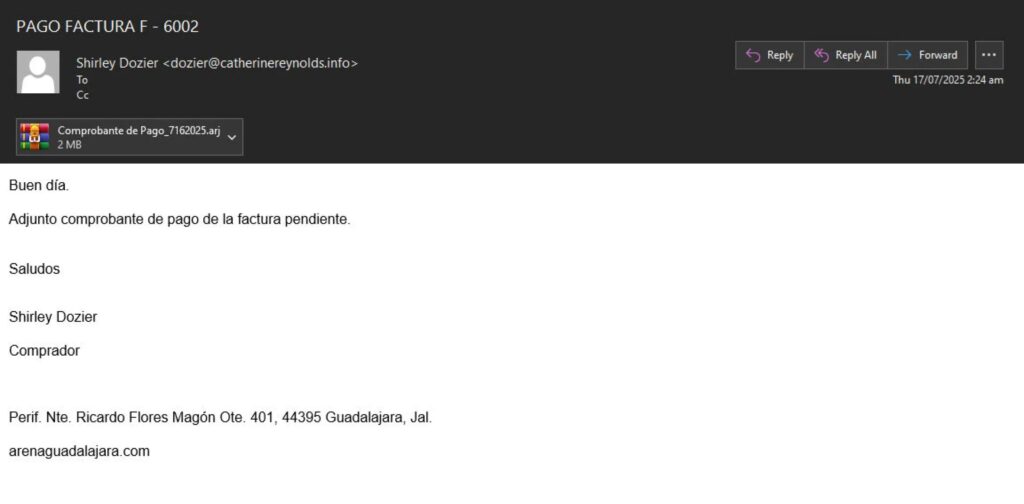
QuirkyLoader begins its attack through carefully designed spam emails that contain malicious archive attachments. These archives include three essential components: a legitimate executable, an encrypted malicious payload disguised as a DLL, and a malicious DLL loader module.
Threat actors behind QuirkyLoader employ both trusted email service providers and self-hosted email servers for distribution, which enhances campaign resilience and reduces the risk of takedown.
Advanced DLL Side-Loading Techniques
Security researchers at IBM have identified QuirkyLoader’s unique attack methods, which rely on DLL side-loading to execute malicious code while appearing legitimate.
When the target runs the seemingly harmless executable, it automatically loads the malicious DLL. This DLL then decrypts and injects the final payload into target processes using process hollowing, ensuring the malware operates stealthily.
Ahead-of-Time (AOT) Compilation for Evasion
One of QuirkyLoader’s key technical advancements is its consistent use of Ahead-of-Time (AOT) compilation for DLL loader modules.

The malware’s components are written in C# .NET but compiled using AOT methods that first convert the code into Microsoft Intermediate Language (MSIL) and then directly into native machine code. This bypasses traditional .NET runtime dependencies, making the malware resemble programs written in C or C++, and complicates detection and analysis.
Payload Decryption and Stealth Execution
QuirkyLoader uses the Speck-128 cipher in Counter (CTR) mode for decrypting its payloads, with complex Add-Rotate-XOR (ARX) operations to generate secure keystreams.
The malware performs process hollowing on legitimate Windows processes such as AddInProcess32.exe, InstallUtil.exe, and aspnet_wp.exe, ensuring the payload executes stealthily while avoiding detection.


