A new and sophisticated supply chain attack has been uncovered, targeting developers through a malicious Go module package. This package disguises itself as a legitimate SSH brute force tool but secretly collects and transmits stolen credentials to cybercriminal operators.
Disguised Package with Hidden Malicious Intent
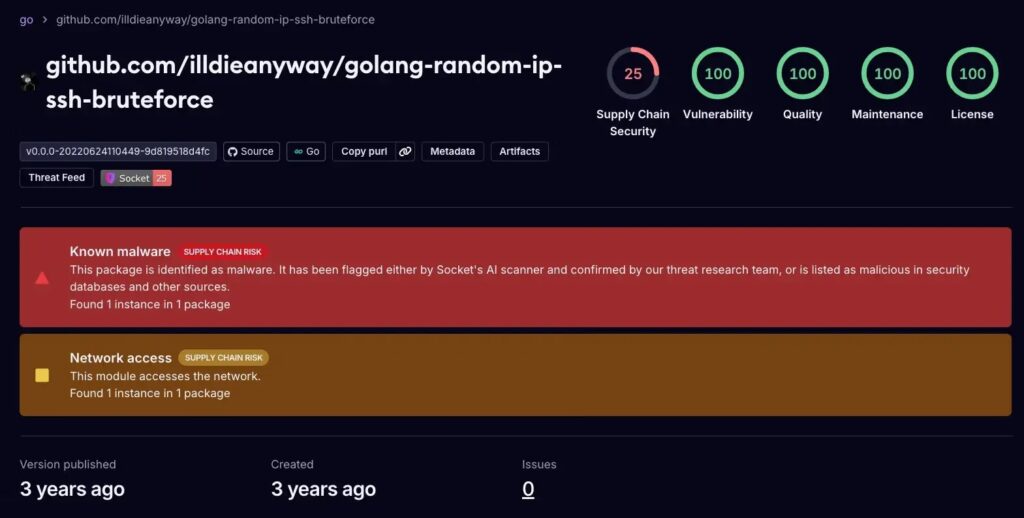
The malicious package, named “golang-random-ip-ssh-bruteforce,” promotes itself as a fast brute forcing utility for SSH. However, researchers discovered that its real purpose is to exfiltrate successful login credentials through a Telegram bot under the control of threat actors.
This package scans random IPv4 addresses on TCP port 22, attempts logins using a built-in wordlist of usernames and passwords, and automatically forwards any successful results to its operators.
The deceptive part is that many victims believe they are engaging in ethical penetration testing or security research, while in reality, they are unknowingly feeding valuable credentials to cybercriminals.
Discovery by Security Researchers
Security analysts from Socket.dev identified the hidden malicious behavior embedded in the tool. They confirmed that the package has been active since June 24, 2022, operating as a backdoor credential harvester.
The first successful SSH login immediately triggers the exfiltration process. The compromised IP address, username, and password are sent directly to a Telegram bot endpoint, controlled by a Russian-speaking actor who uses the alias “IllDieAnyway” on GitHub.

Exploiting Developer Trust in Open-Source Packages
This attack highlights the increasing abuse of developer trust in open-source ecosystems. Malicious actors now disguise their tools as penetration testing utilities while secretly embedding backdoor functionalities.
By downloading and running the package, users unintentionally assist criminals in large-scale credential harvesting campaigns, rather than conducting legitimate security testing.
Technical Implementation and Evasion Techniques
The malicious package uses multiple methods to remain stealthy and efficient:
- Minimal Wordlist: Includes only default credentials such as
root:toor,admin:password, and IoT-specific combinations (root:raspberry,root:dietpi). This reduces scanning noise while keeping attacks effective. - Telegram API Exploitation: Compromised credentials are sent via an HTTP GET request to the hardcoded endpoint:
Telegram API Endpoint
Credentials are delivered in the format: ip:username:password to chat ID 1159678884, linked to the Telegram user @io_ping. - Bypassing Security Checks: The malware configures SSH connections with
HostKeyCallback: ssh.InsecureIgnoreHostKey()which disables server verification, allowing rapid testing across multiple systems.
Researchers also noted that the tool contained an embedded wordlist file (wl.txt), specifically targeting IoT devices, single-board computers, and poorly secured Linux systems.


