Cybersecurity experts have uncovered a rapidly growing social engineering method known as ClickFix, which has been increasingly adopted by attackers since early 2024.
This technique impacts both Windows and macOS devices, convincing users to unknowingly run harmful commands under the guise of routine troubleshooting steps. According to recent findings, thousands of enterprise and personal systems worldwide are being affected daily, making it a notable shift in social engineering tactics.
How the ClickFix Attack Works
The attack begins with deceptive prompts such as fake error messages, verification pop-ups, or CAPTCHA challenges that demand quick user interaction.
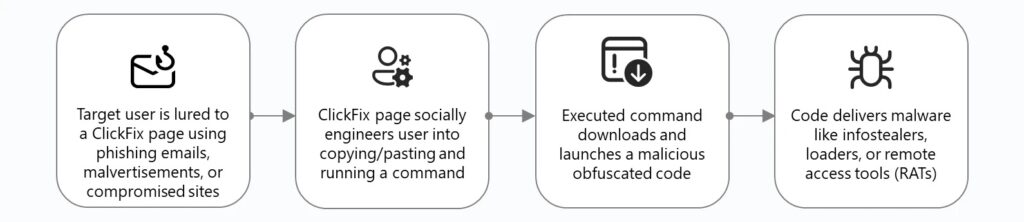
These lures are usually distributed through phishing campaigns, malicious ads, or hijacked websites that redirect users to fraudulent landing pages. Because the attack manipulates human behavior rather than relying solely on malware, it can easily bypass traditional automated defenses.
Malware Delivered via ClickFix
Microsoft researchers have observed attackers using ClickFix to distribute multiple types of malicious software, including:
- Lumma Stealer (infostealer)
- Remote Access Tools like Xworm and AsyncRAT
- Loaders such as Latrodectus and MintsLoader
- Rootkits including modified versions of the open-source r77
These threats often operate as fileless malware, staying in memory through built-in system tools instead of writing executable files to disk.
Exploitation through Fake Verifications
Victims are commonly shown fake verification pages that mimic trusted services such as Google reCAPTCHA, Cloudflare Turnstile, or even Discord. When the user interacts, hidden JavaScript executes and silently copies malicious code into the system clipboard using navigator.clipboard.writeText().
Technical Execution
The main trick lies in the misuse of the Windows Run dialog box (Windows key + R). Because many users are unfamiliar with its risks, attackers exploit this feature to execute malicious commands.
Most commands rely on PowerShell functions like:
iwr(Invoke-WebRequest)irm(Invoke-RestMethod)iex(Invoke-Expression)
These are used to pull malware from remote servers.
Case Study: Lampion Campaign
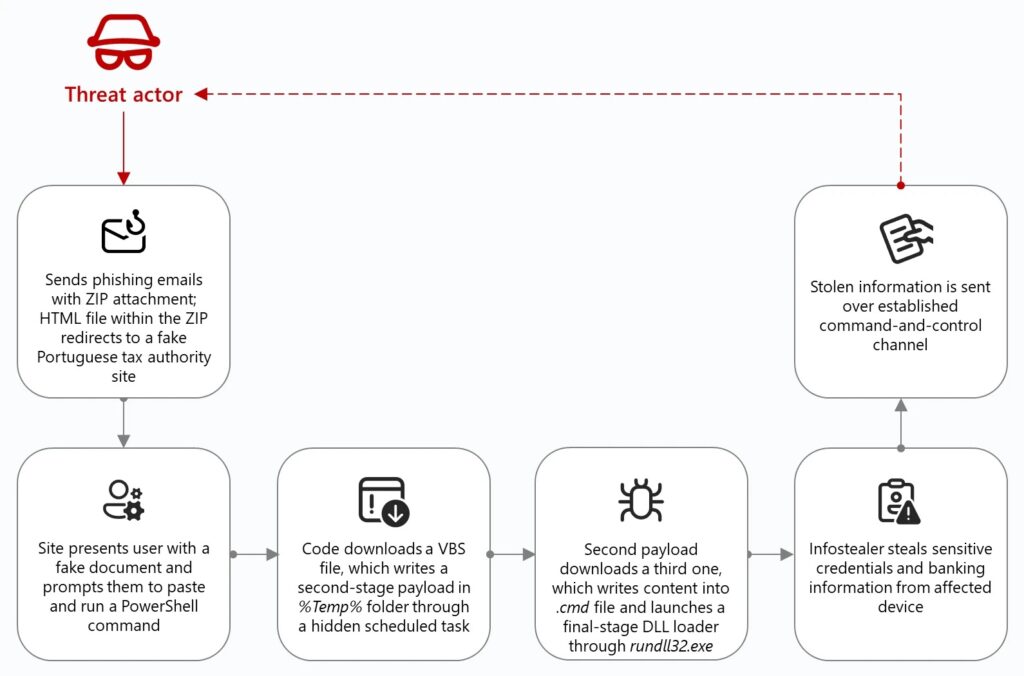
In May 2025, a major ClickFix-driven campaign was uncovered in Portugal. Phishing emails carrying ZIP files contained HTML pages that redirected victims to a fake Portuguese tax authority website.
Once there, users triggered ClickFix lures that executed PowerShell commands, downloading an obfuscated VBScript into the %TEMP% folder and maintaining persistence through scheduled tasks.
macOS Variant of ClickFix
Attackers have also adapted this method for macOS devices. One example is the deployment of Atomic macOS Stealer (AMOS), which repeatedly requested users’ system passwords and used them to bypass protections with commands like xattr -c.
Detection and Defense
ClickFix activity can be detected by monitoring the RunMRU registry key, which records the history of commands executed via the Run dialog. Security teams should look for entries referencing:
- Living-off-the-land binaries (LOLBins)
- Direct IP connections
- CDN-based malicious domains
- Suspicious file extensions
To further avoid detection, attackers often employ Base64 encoding, string concatenation, and escaped characters.


