A newly analyzed malware strain named KorPlug has surfaced as a significant cybersecurity threat. This malware leverages advanced obfuscation techniques that make detection and reverse engineering extremely challenging.
Obfuscation and Execution Techniques
KorPlug stands out due to its use of O-LLVM-based obfuscation, which transforms normal program structures into complex control flow graphs (CFGs). These techniques prevent analysts from easily tracing its operations through traditional static or dynamic analysis.
The malware begins its attack by exploiting DLL side-loading, abusing legitimate software to run malicious code.
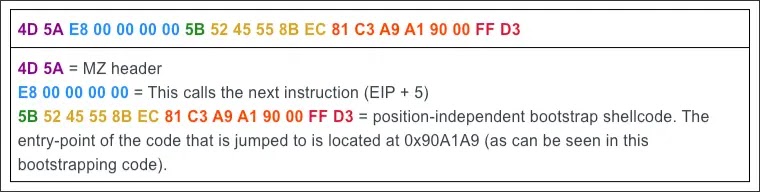
The primary payload, with the following identifier:
- SHA-256:
b6b239fe0974cf09fe8ee9bc5d0502174836a79c53adccdbb1adeb1f15c6845c - File size: 624 KB
- Architecture: x86 PE
This payload bypasses Windows DLL loading by executing shellcode via the EnumSystemGeoID API call.
Control Flow Anomalies
Research by RevEng.AI uncovered that the malware’s second-stage payload modifies its execution paths to resist standard disassembly. In particular, its Initialize function includes an abnormal CFG structure, making both manual and automated analysis difficult.
KorPlug applies three primary O-LLVM obfuscation techniques:
- Control flow flattening
- Bogus control flow injection
- Instruction substitution
These methods alter the program’s execution architecture itself, not just the code, making signature-based detection largely ineffective. Public deobfuscation tools are ineffective unless heavily modified.
Advanced Control Flow Obfuscation
The malware’s most unique trait is its control flow flattening, which reorganizes function structures into switch-based dispatch mechanisms. This creates multiple interconnected basic blocks, hiding the real logic.
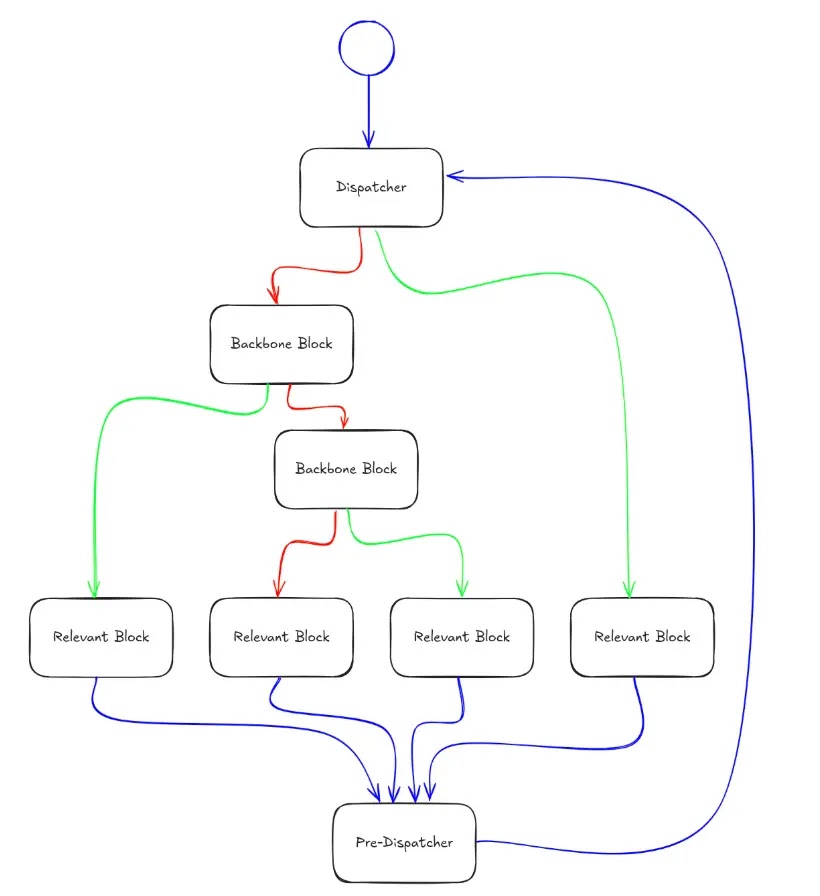
Key elements inside the obfuscated CFG include:
- Pre-dispatcher blocks: Act as the primary entry point with high predecessor counts.
- Dispatcher mechanism: Uses a state variable to guide execution across blocks.
- Backbone blocks: Handle transitions using operations like
JMP,MOV,SUB, andJZ.
def identify_relevant_blocks(cfg):
relevant_blocks = []
for block in cfg.nodes():
if has_state_variable_assignment(block):
block_type = classify_assignment_type(block)
relevant_blocks.append((block, block_type))
return relevant_blocks
RevEng.AI analysts noted that proper deobfuscation requires tracking state variable assignments across all relevant blocks. Once mapped, researchers can correlate these assignments with backbone operations to reconstruct the original flow.
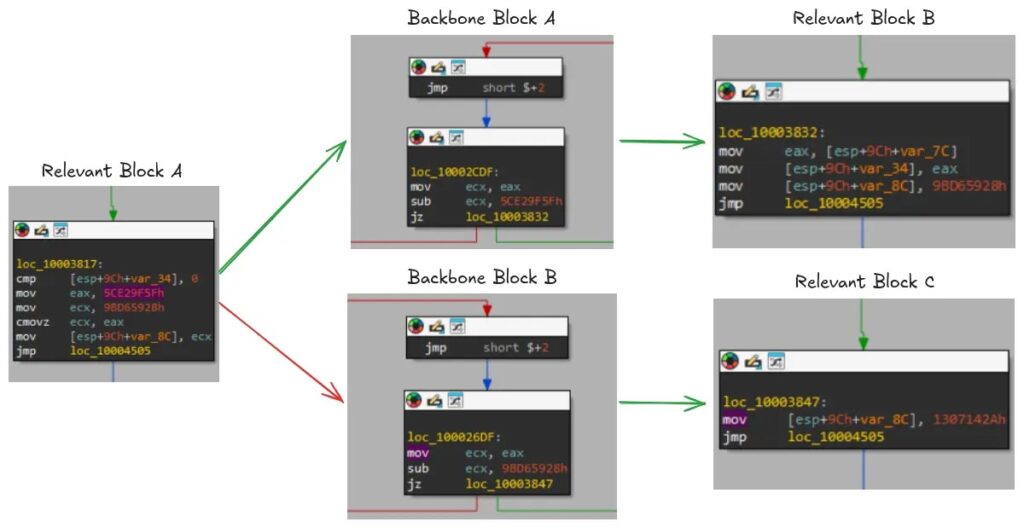
The binary patching process allows analysts to bypass dispatcher blocks entirely, restoring the malware’s intended execution sequence.
| Indicator Type | Value |
|---|---|
| SHA-256 Hash | b6b239fe0974cf09fe8ee9bc5d0502174836a79c53adccdbb1adeb1f15c6845c |
| File Type | 624 KB x86 PE |
| Execution API | EnumSystemGeoID (used for shellcode execution) |


