A highly advanced phishing operation has been detected, abusing the trusted reputation of SendGrid to harvest user credentials. Attackers are using SendGrid’s legitimate cloud-based email service to distribute phishing emails that evade traditional email security filters.
Campaign Overview
This campaign relies on psychological manipulation and urgency tactics, with three crafted email themes designed to pressure recipients into quick action. Each email impersonates official SendGrid notifications while using spoofed sender addresses to increase authenticity.
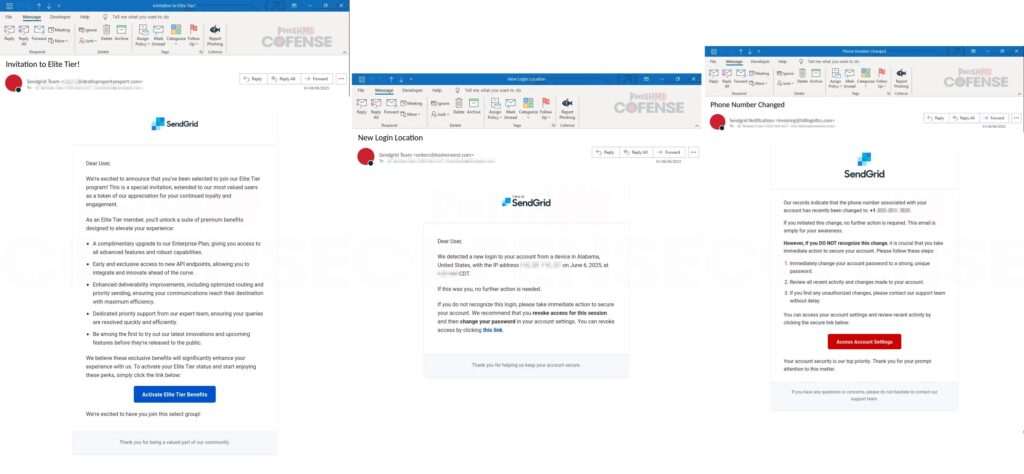
The emails are polished with professional formatting, legitimate-looking logos, and a design style almost identical to genuine SendGrid communications.
Social Engineering Techniques
The attackers employ classic fear and reward manipulation, including:
- Fake security alerts about unusual login attempts from fabricated IP addresses.
- Promotional offers for higher-tier SendGrid services to lure victims.
Cofense researchers uncovered the operation through their Phishing Defense Center, highlighting the advanced social engineering behind the attack.
Redirect Chain Exploitation
The technical core of this attack lies in abusing open redirect vulnerabilities. The attackers use domains such as:
hXXp://url6849[.]destinpropertyexpert[.]com/ls/click?upn=[encoded_parameters]
These redirect URLs contain base64-encoded payloads that hide the final malicious destination, bypass URL reputation checks, and enable attacker-side tracking.
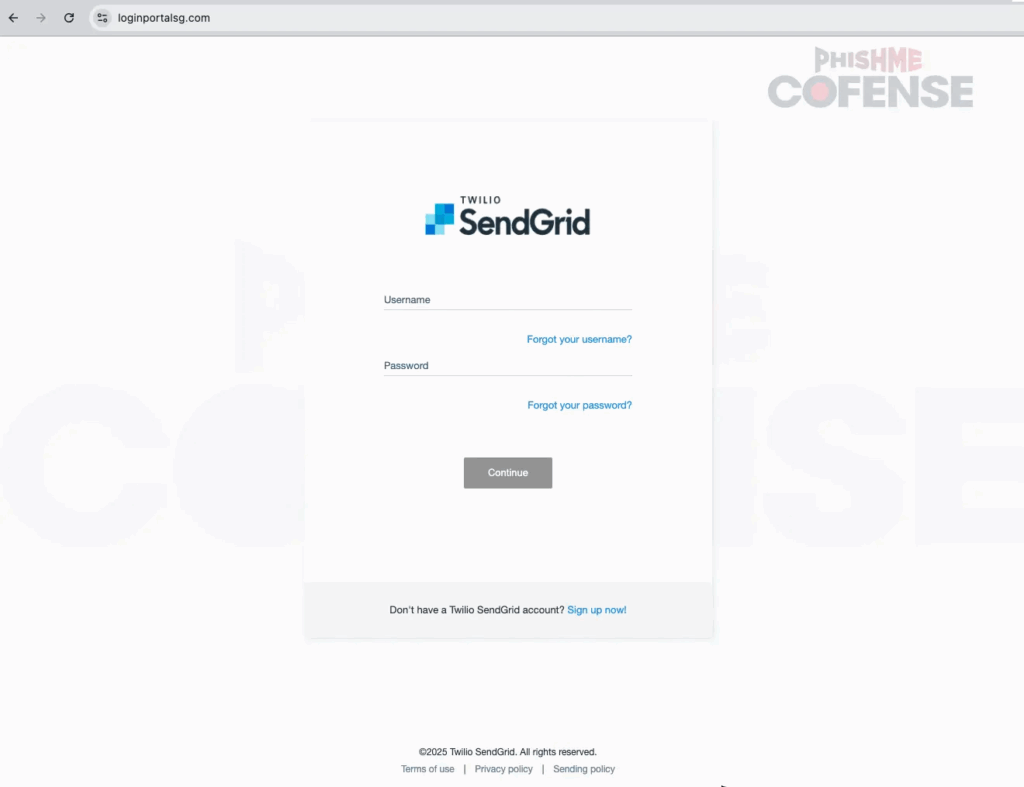
Once decoded, victims are redirected to phishing portals hosted on:
- loginportalsg[.]com
- sendgrid[.]aws-us5[.]com
Both hosted on IP 185.208.156.46.
These fake login pages closely replicate SendGrid’s genuine design, making it highly convincing for users and dramatically increasing the chance of stolen credentials.
| Indicator Type | Value |
|---|---|
| Malicious Domain | loginportalsg[.]com |
| Malicious Domain | sendgrid[.]aws-us5[.]com |
| Exploited Domain | url6849[.]destinpropertyexpert[.]com |
| Phishing IP Address | 185.208.156.46 |
| Example Redirect URL | hXXp://url6849[.]destinpropertyexpert[.]com/ls/click?upn=[encoded] |


