Large-Scale Attack Campaign
A newly identified cyber campaign, codenamed ShadowCaptcha, has compromised more than 100 WordPress websites to redirect visitors toward fake CAPTCHA verification pages. These pages use the ClickFix social engineering technique to deliver information stealers, ransomware, and cryptocurrency miners.
The operation, first discovered in August 2025 by the Israel National Digital Agency, highlights the growing use of multi-stage payloads and social engineering in modern cybercrime.
“The campaign combines social engineering, living-off-the-land binaries (LOLBins), and staged payload delivery to gain and sustain access within victim systems,” noted researchers Shimi Cohen, Adi Pick, Idan Beit Yosef, Hila David, and Yaniv Goldman.
Attack Flow and Objectives
The main goals of ShadowCaptcha are:
- Harvesting sensitive credentials and browser data
- Installing cryptocurrency miners for illicit profits
- Triggering ransomware attacks for financial extortion
The attack begins when a victim unknowingly visits a compromised WordPress site. Malicious JavaScript embedded in the site redirects the visitor to a fake Cloudflare or Google CAPTCHA page.
From this point, the ClickFix method presents two different execution paths:
- Windows Run Dialog Path – Victims are tricked into using the Windows Run dialog, which leads to the deployment of Lumma and Rhadamanthys stealers through MSI installers or HTA files executed via
mshta.exe. - HTA File Path – Victims are instructed to save and run an HTML Application (HTA). This results in the installation of Epsilon Red ransomware.
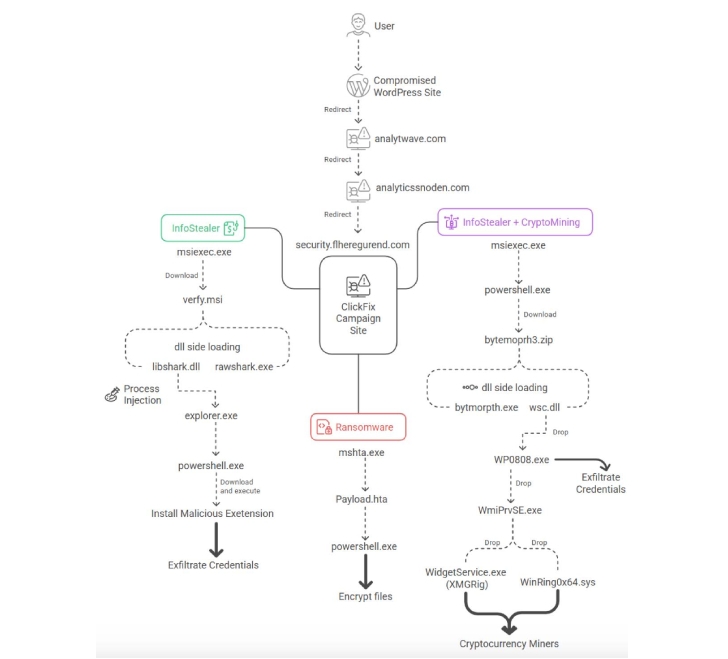
CloudSEK previously documented similar ClickFix techniques being used to distribute Epsilon Red ransomware. In these cases, malicious JavaScript automatically copies a harmful command to the victim’s clipboard using navigator.clipboard.writeText, waiting for the user to paste and run it.
Advanced Evasion and Payloads
The campaign uses several stealth methods:
- Anti-debugging techniques to prevent inspection of the malicious pages
- DLL side-loading to disguise malicious code as legitimate processes
In addition to stealers and ransomware, select ShadowCaptcha operations deploy an XMRig-based crypto miner. Some versions pull their configuration from Pastebin URLs, allowing attackers to adjust mining parameters dynamically.
For mining optimization, attackers drop a vulnerable driver (WinRing0x64.sys) to gain kernel-level privileges and interact with CPU registers.
Global Impact
Most compromised sites are located in Australia, Brazil, Italy, Canada, Colombia, and Israel, targeting industries such as technology, healthcare, hospitality, legal, finance, and real estate.
The exact method of compromise is uncertain, though researchers suggest attackers are exploiting WordPress plugins or using stolen administrator credentials.
Mitigation Recommendations
To reduce risks:
- Educate users about ClickFix-style social engineering traps
- Segment networks to limit lateral movement
- Keep WordPress sites updated and enforce multi-factor authentication (MFA)
As the researchers explained:
“ShadowCaptcha demonstrates how social engineering has evolved into full-spectrum cyber operations. By abusing built-in Windows tools, obfuscated scripts, and vulnerable drivers, attackers gain persistence and can shift between stealing data, mining cryptocurrency, or deploying ransomware.”
Related Campaigns – Help TDS Evolution
This disclosure aligns with research from GoDaddy, which analyzed the Help TDS traffic distribution system active since 2017. Help TDS is linked to schemes such as VexTrio Viper, redirecting victims to malicious destinations based on targeting rules.
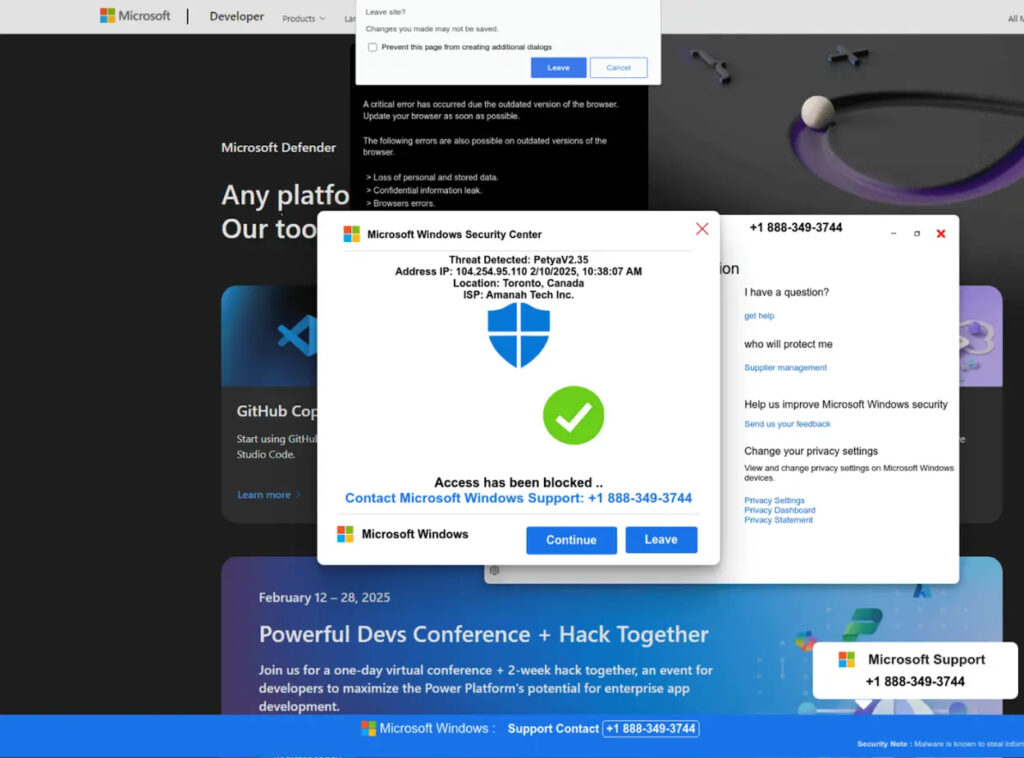
Help TDS supports operations like tech support scams, fake security alerts, and fraudulent CAPTCHA challenges, all designed to trap users.
Between late 2024 and August 2025, attackers also created a malicious WordPress plugin called woocommerce_inputs. This fake plugin masquerades as WooCommerce but enables:
- Traffic redirection
- Credential theft
- Geographic filtering
- Advanced evasion
According to GoDaddy, the plugin is installed on over 10,000 WordPress sites worldwide.
“This plugin represents a transition from simple redirects to a full malware-as-a-service ecosystem. By providing ready-made C2 infrastructure, PHP injection templates, and malicious plugins, Help TDS lowers the entry barrier for cybercriminals,” GoDaddy stated.


