A newly discovered ransomware family named Cephalus has emerged as a serious cyber threat, infiltrating organizations by exploiting compromised Remote Desktop Protocol (RDP) credentials that lack multi-factor authentication (MFA).
The ransomware’s name comes from Greek mythology, referencing Cephalus, the son of Hermes, who accidentally killed his wife with an infallible javelin. This symbolism underscores the destructive precision of the malware’s design.
Distinctive Characteristics of Cephalus
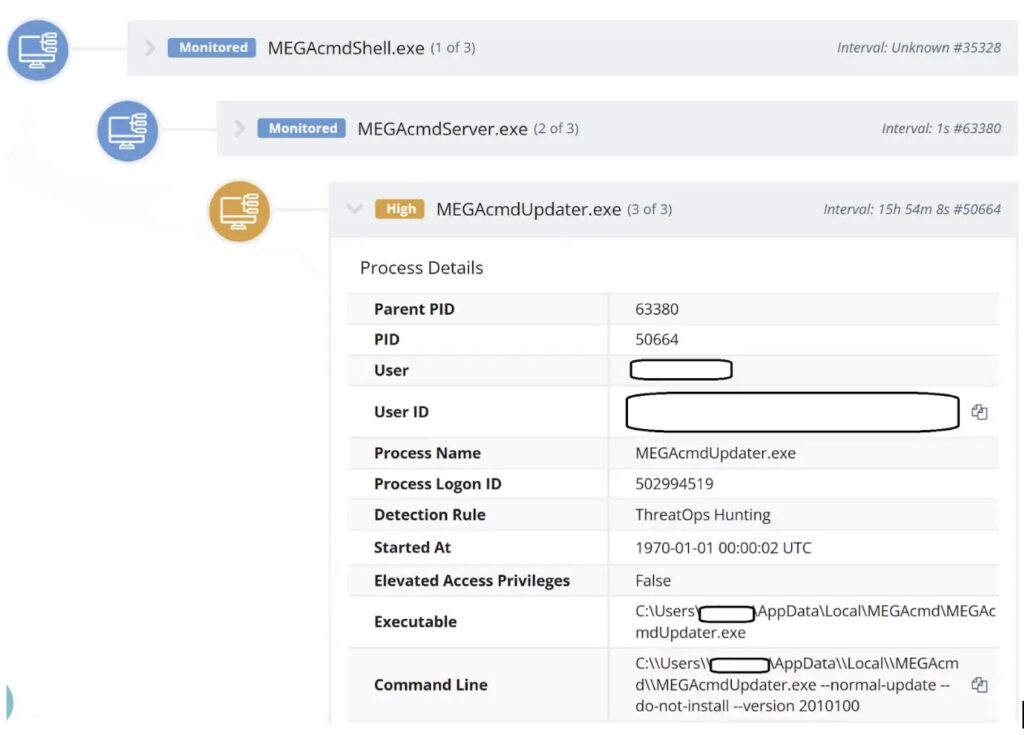
Unlike many ransomware strains, Cephalus stands out with its unique infection techniques and advanced evasion methods. After gaining access, attackers exfiltrate sensitive data to the MEGA cloud storage platform before deploying the ransomware payload.
DLL Sideloading via Security Software
Huntress researchers identified Cephalus in two confirmed incidents on August 13 and 16, 2025, where it successfully compromised organizations using SentinelOne security products.
The malware abuses a legitimate SentinelOne executable, SentinelBrowserNativeHost.exe, by placing it in the Downloads folder. From there, it sideloads a malicious DLL named SentinelAgentCore.dll, which then loads an additional file, data.bin, containing the ransomware code.
This multi-stage execution chain provides stealth, enabling the malware to bypass standard detection mechanisms.
System Disruption and Defense Evasion
Once active, Cephalus immediately executes system recovery prevention measures, beginning with the command:
vssadmin delete shadows /all /quietThis deletes all shadow copies, making recovery through snapshots impossible.
It then executes PowerShell commands to disable Windows Defender, creating exclusions for file types like .cache, .tmp, .dat, and .sss.
Registry modifications are also applied to disable:
- Real-time protection
- Behavior monitoring
- On-access protection
In addition, Cephalus stops services such as SecurityHealthService, Sense, WinDefend, and WdNisSvc, further weakening defenses.
Ransom Note and Extortion Strategy
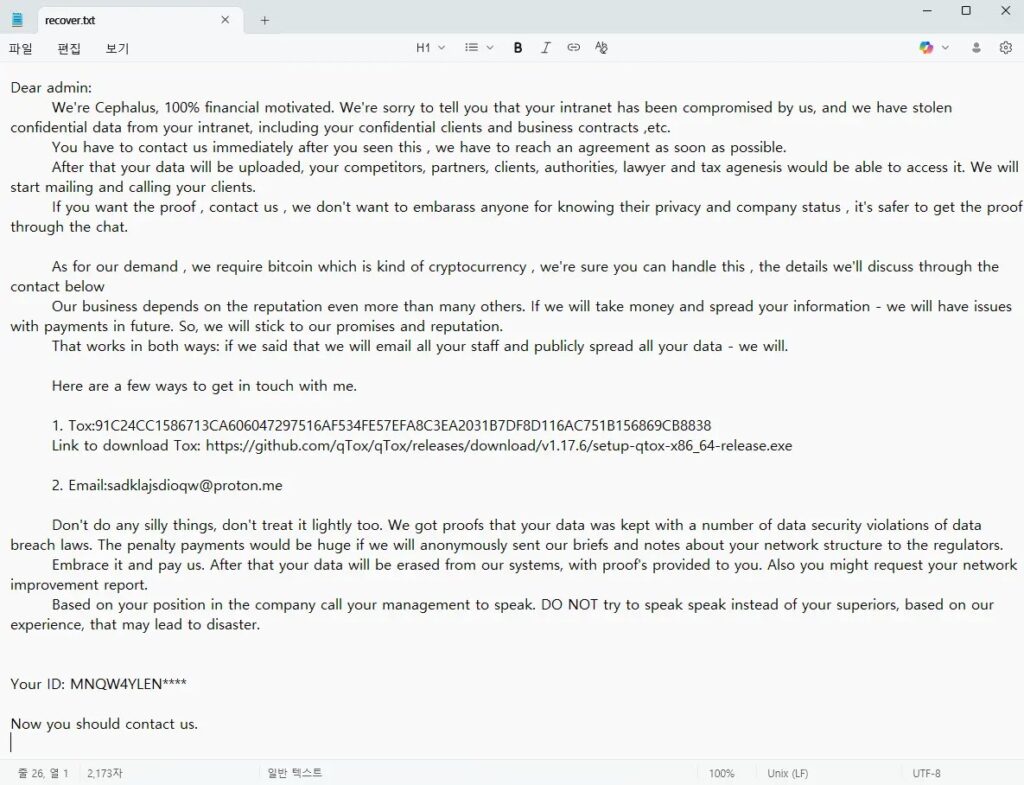
The ransomware encrypts victim files with the “.sss” extension and drops recover.txt ransom notes.
A unique feature of Cephalus ransom demands is their reference to real-world news articles about past ransomware incidents, an intimidation tactic meant to enhance credibility and pressure victims into payment.
Defense Recommendations
To reduce exposure and mitigate risks, organizations should:
- Implement MFA for all RDP access.
- Monitor for legitimate security tool executables placed in unusual directories.
- Maintain robust Endpoint Detection and Response (EDR) capabilities to spot anomalous activity.