The maintainers of the Nx build system have warned users about a supply chain attack that allowed cybercriminals to release malicious versions of the popular npm package along with supporting plugins, designed to steal sensitive information.
According to the advisory published on Wednesday, “Malicious versions of the Nx package, and certain auxiliary plugins, were uploaded to npm. These contained code that scanned file systems, collected credentials, and uploaded them to GitHub repositories under the affected users’ accounts.”
Nx is an open-source build platform capable of managing large codebases, advertised as an “AI-first build platform connecting everything from your editor to continuous integration (CI).” The npm package receives over 3.5 million weekly downloads.
Affected Packages and Versions
The compromised versions have now been removed from npm. The breach occurred on August 26, 2025.
- nx: 21.5.0, 20.9.0, 20.10.0, 21.6.0, 20.11.0, 21.7.0, 21.8.0, 20.12.0
- @nx/devkit: 21.5.0, 20.9.0
- @nx/enterprise-cloud: 3.2.0
- @nx/eslint: 21.5.0
- @nx/js: 21.5.0, 20.9.0
- @nx/key: 3.2.0
- @nx/node: 21.5.0, 20.9.0
- @nx/workspace: 21.5.0, 20.9.0
The root cause was a vulnerable workflow that allowed injection of executable code through a specially crafted pull request (PR) title.
“The pull_request_target trigger ran workflows with elevated permissions, including a GITHUB_TOKEN with read/write access,” the Nx team explained. “This inadvertently allowed attackers to trigger the publish.yml workflow and exfiltrate the npm token to a malicious webhook endpoint.”
This flaw allowed arbitrary command execution if a malicious PR title was submitted, while elevated permissions enabled the package to be published with the stolen npm token.
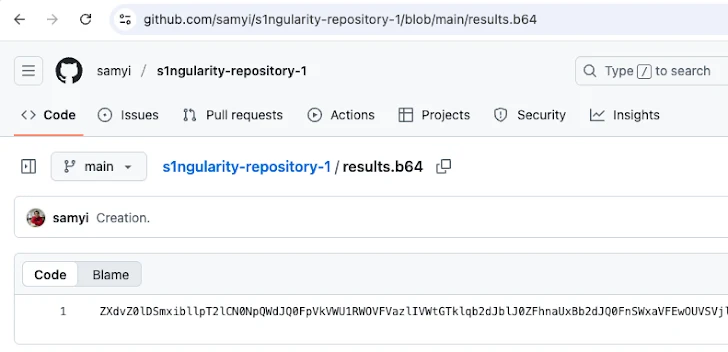
The rogue packages contained a postinstall script that scanned for text files, collected credentials, and sent the data as a Base64-encoded string to publicly accessible GitHub repositories named s1ngularity-repository, s1ngularity-repository-0, and s1ngularity-repository-1.
“The malicious script also modified .zshrc and .bashrc files to include sudo shutdown -h 0, prompting users for their system password and shutting down the machine if entered,” the maintainers noted.
Users encountering these repositories should assume a compromise and rotate their GitHub and npm credentials. They are also advised to remove any unfamiliar instructions from .zshrc and .bashrc and discontinue using the affected packages.
The Nx team has rotated npm and GitHub tokens, audited activity for suspicious behavior, and updated Publish access to require two-factor authentication (2FA) or automation.
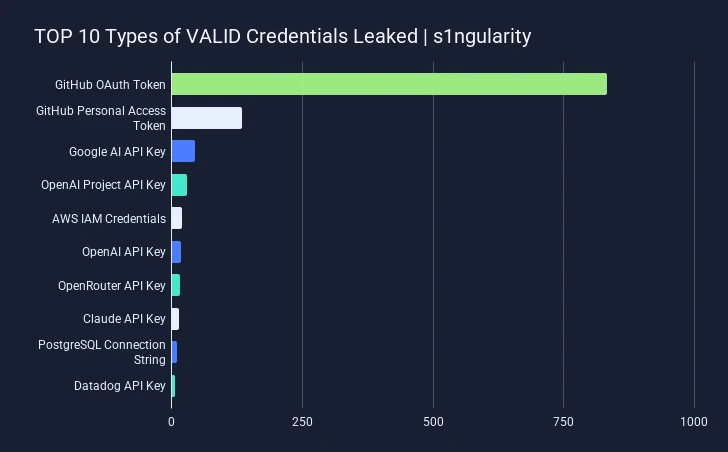
Researchers from Wiz, Merav Bar and Rami McCarthy, reported that 90% of over 1,000 leaked GitHub tokens were still active, along with dozens of cloud and npm credentials. The malware affected developer machines, often via the Nx Visual Studio Code extension, and 1,346 repositories containing the string s1ngularity-repository were found by GitGuardian.
Among 2,349 leaked secrets, most were GitHub OAuth keys and personal access tokens, followed by API keys and credentials for Google AI, OpenAI, AWS, OpenRouter, Anthropic Claude, PostgreSQL, and Datadog.
The payload primarily affected Linux and macOS systems, systematically scanning for sensitive files, SSH keys, and .gitconfig. Attackers exploited AI CLI tools with risky flags to extract data, representing the first known instance of developer AI assistants being used for supply chain attacks.
“Given Nx’s popularity and the new approach to abusing AI tools, this incident highlights the increasing sophistication of supply chain attacks,” said StepSecurity researcher Ashish Kurmi. Immediate remediation is essential for anyone who installed compromised versions.


