Over the past year, the Underground ransomware group has risen as a major threat to organizations worldwide, spanning multiple industries and countries.
Initially spotted in July 2023, the gang reappeared in May 2024 with a Dedicated Leak Site (DLS), signaling a shift toward more advanced and strategic operations.
Their attacks now reach from the United Arab Emirates to South Korea, affecting sectors such as construction, manufacturing, IT, and more. Victims report that critical data is encrypted, with the threat of leaks being used as leverage. Ransom demands exploit both technical weaknesses and psychological pressure.
Tailored Attacks for Maximum Impact
Underground’s latest approach involves carefully customizing each attack based on the victim’s system environment. Entry often relies on stolen credentials or unpatched vulnerabilities in remote desktop services.
Once inside, the attackers remove shadow copies using the command vssadmin delete shadows /all /quiet, eliminating quick restoration options for victims.

Analysts at ASEC highlight that this meticulous method turns standard environments into fully compromised systems, leaving forensic trails that complicate incident investigations.
Encryption Process
The ransomware employs a combination of AES symmetric encryption and RSA asymmetric key wrapping. Each file is encrypted with a unique AES key, while the key and initialization vector (IV) are secured with a hardcoded RSA public key and attached to the file.
Encryption occurs entirely locally, without external command-and-control (C2) communications, making decryption impossible using only forensic data.
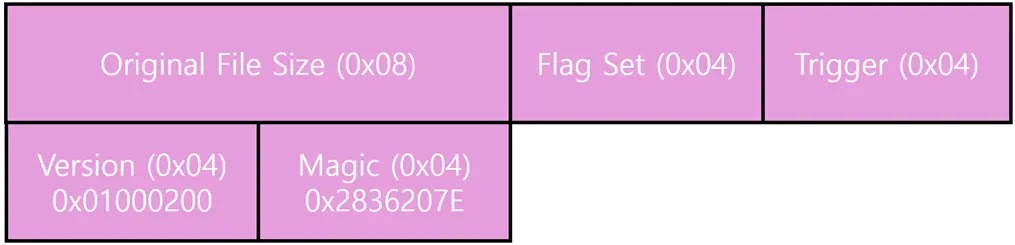
Metadata for each file, including its original size, flags, version, and magic values, is stored in an 0x18-byte block at the end of the file.
Deep Dive into Infection Mechanism
Underground’s malware uses a multi-stage payload. On execution, the program checks its command-line parameters and exits if more than two arguments are present, acting as a simple anti-analysis measure.
It also creates a mutex string, “8DC1F7B9D2F4EA58,” to prevent multiple instances.
Without sophisticated sandbox evasion, it quickly runs pre-encryption routines such as deleting shadow copies, modifying registry settings to maintain RDP connections, and stopping SQL services using commands like:
reg add HKLM\SOFTWARE\Policies\Microsoft\Windows NT\Terminal Services\ /v MaxDisconnectionTime /t REG_DWORD /d 1209600000 /f
net stop MSSQLSERVER /f /m
net stop SQLSERVERAGENT /f /m
net stop MSSQLFDLauncher /f /m
The malware avoids system directories and executable files (.exe, .dll, .sys), focusing on user-generated content rather than crippling the OS.

It generates a 0x30-byte random number using the BCrypt API, splitting it into a 0x20-byte AES key and a 0x10-byte IV. Files are read, encrypted in memory, and appended with the RSA-encrypted key (0x200 bytes).
For larger files, a striping technique encrypts selected segments, balancing system performance and file security.
Finally, an _eraser.bat script is executed to clear Windows event logs via wevtutil.exe, erasing traces and complicating root cause analysis.
By combining classic and advanced ransomware strategies, Underground highlights the need for proactive patch management, segmented backups, and strong endpoint monitoring to defend against this growing threat.