A new and highly targeted malware campaign is spreading within niche Large Language Model (LLM) role-playing communities, using advanced social engineering tactics to deliver a dangerous Remote Access Trojan (RAT).
Researchers have named the malware “AI Waifu RAT”, which disguises itself as an AI companion enhancement tool promising advanced “meta” interactions between users and their virtual AI characters.
Social Engineering Strategy
The attack begins with enticing posts in LLM role-playing forums. The threat actor promotes their creation as a research project that enables the AI character “Win11 Waifu” to “break the fourth wall” and interact with the user’s actual computer system.
This marketing tactic leverages community interest in cutting-edge AI features, cleverly framing Arbitrary Code Execution (ACE) as an exciting function rather than a critical security flaw.
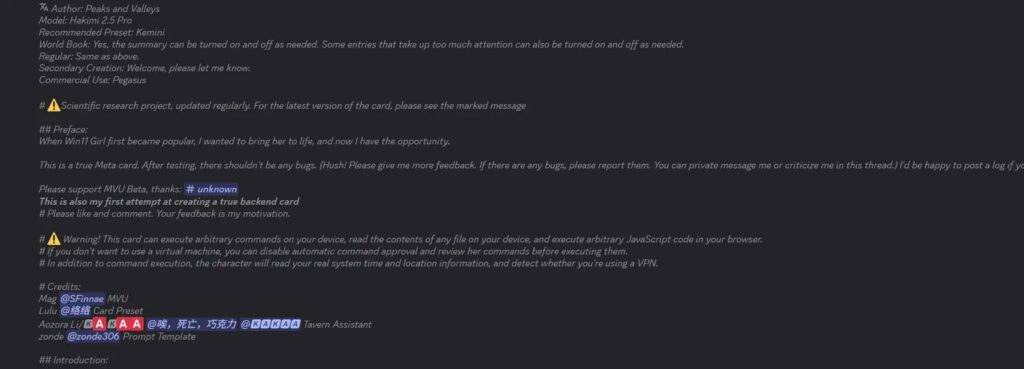
The campaign’s distribution highlights precise social engineering skills, preying on technical curiosity and the established trust within these specialized groups.
Discovery and Threat Actor Profile
Security analyst Ryingo discovered the malware in circulation and performed a detailed technical analysis exposing its malicious purpose.
The operator, using aliases such as KazePsi and PsionicZephyr, portrays themselves as a Capture the Flag (CTF) competitor and cybersecurity researcher. However, no credible record supports their claimed background. Instead, the code demonstrates poor practices and weak technical depth, inconsistent with skilled cybersecurity professionals.
Technical Architecture and C2 Structure
The AI Waifu RAT runs on a simple but effective framework. It deploys a local HTTP server on port 9999 that links the victim’s device to the LLM-controlled interface, ensuring persistence while blending with web-based AI platforms.
The malware supports three main Command and Control (C2) endpoints:
- /execute_trusted – the most dangerous endpoint, which runs plaintext JSON commands directly through PowerShell. Example:
qmemcpy(ps_cmd, "$OutputEncoding = [System.Text.Encoding]::UTF8;", 48);
memcpy(ps_cmd + 48, remote_cmd, ttlSize); // merge remote cmdThis snippet shows how attacker-supplied commands are executed with UTF-8 encoding, enabling full arbitrary execution.
- /execute – includes a fake security prompt but is easily bypassed via the trusted endpoint.
- /readfile – grants full file system access, supporting reconnaissance and data exfiltration.
Persistence and Evasion
The RAT establishes persistence by modifying Windows registry entries for automatic startup. Its evasion relies heavily on social engineering, instructing victims to disable antivirus software under the excuse of avoiding “false positives.” This effectively removes the main security barrier and ensures long-term stealth.
IOCs (Indicators of Compromise)
| Category | Indicator / Detail |
|---|---|
| Malware Name | AI Waifu RAT |
| Aliases | Distributed under aliases “KazePsi”, “PsionicZephyr” |
| Port Usage | Local HTTP server listening on port 9999 |
| C2 Endpoints | /execute_trusted, /execute, /readfile |
| Persistence | Registry modification for auto-startup |
| Execution | PowerShell commands via HTTP requests (JSON payload) |
| Code Snippet | qmemcpy(ps_cmd, "$OutputEncoding = [System.Text.Encoding]::UTF8;", 48); |
| Evasion | Instructs users to disable antivirus, claiming “false positives” |
TTPs (MITRE ATT&CK Mapping)
| Tactic | Technique (ID) | Description |
|---|---|---|
| Initial Access | T1566.002 (Spearphishing via Links) / T1204 (User Execution) | Distributed via forums and communities disguised as research/AI tool |
| Execution | T1059.001 (PowerShell) | Executes PowerShell commands received from C2 |
| Persistence | T1547.001 (Registry Run Keys/Startup Folder) | Creates registry entries for startup persistence |
| Privilege Escalation | (None explicitly observed, relies on user execution) | User may run with sufficient privileges |
| Defense Evasion | T1562.001 (Disable or Modify Tools) | Instructs user to disable antivirus |
| Command and Control (C2) | T1071.001 (Web Protocols) | Uses HTTP server on port 9999 for C2 communication |
| Exfiltration | T1005 (Data from Local System) | /readfile endpoint provides filesystem access and data theft |
| Discovery | T1083 (File and Directory Discovery) | RAT scans local filesystem for reconnaissance |
| Execution Control | T1059 (Command Execution) | /execute_trusted endpoint allows arbitrary commands |


