Cybersecurity experts have noticed a notable shift in Android malware campaigns, where dropper apps—traditionally used to deliver banking trojans—are now distributing simpler malicious software such as SMS stealers and lightweight spyware.
According to a report by ThreatFabric last week, these campaigns often impersonate government or banking apps in India and other Asian countries.
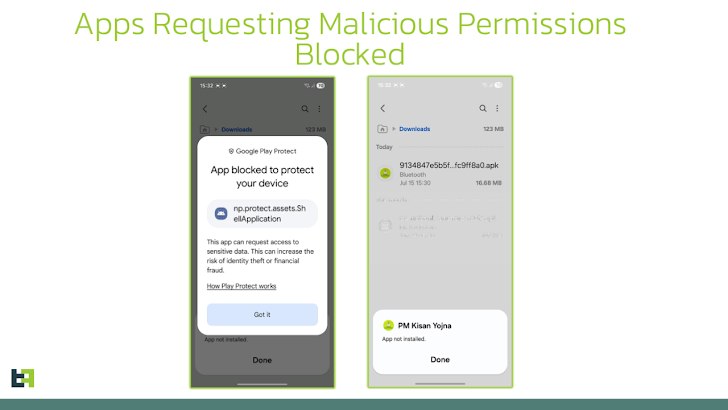
The Dutch mobile security company explained that this change is largely driven by new security measures Google is testing in countries like Singapore, Thailand, Brazil, and India. These measures prevent sideloading of apps requesting risky permissions, including SMS access and accessibility services, which are frequently abused for malicious activity on Android devices.
“Google Play Protect’s defenses, especially through targeted pilot programs, are becoming increasingly effective at blocking unsafe apps before they run,” the report stated. “Additionally, attackers are adapting to secure their operations for the future.”
ThreatFabric noted that wrapping even simple malware inside a dropper gives attackers a protective shell that can bypass current detection systems while allowing them to swap payloads and modify campaigns in the future.
To evade Google’s Pilot Program, some droppers are designed to initially request only harmless permissions and display a fake “update” screen that passes security scans in targeted regions. The actual malicious payload is downloaded or unpacked only after the user clicks the “Update” button, at which point the app seeks the necessary permissions to perform its malicious actions.
“Play Protect may warn users about risks during scans, but if users accept them, the app installs and delivers the malware,” ThreatFabric said. “This highlights a key gap: risky apps can still pass through if the user clicks Install, even under the Pilot Program.”
One example, RewardDropMiner, has historically delivered spyware and a remotely activated Monero cryptocurrency miner, although recent versions have removed the mining functionality.
Some malicious apps distributed by RewardDropMiner targeting Indian users include:
- PM YOJANA 2025 (com.fluvdp.hrzmkgi)
- RTO Challan (com.epr.fnroyex)
- SBI Online (com.qmwownic.eqmff)
- Axis Card (com.tolqppj.yqmrlytfzrxa)
Other droppers avoiding Play Protect detection include SecuriDropper, Zombinder, BrokewellDropper, HiddenCatDropper, and TiramisuDropper.
When contacted, Google confirmed to The Hacker News that none of these malware techniques have been detected on the Play Store, and Play Protect continues to automatically scan apps for threats.
Meanwhile, Bitdefender Labs warned of a related campaign that uses malicious Facebook ads promoting a free premium version of the TradingView app. This campaign distributes an advanced version of the Brokewell banking trojan, enabling attackers to monitor and steal sensitive data from Android devices.
Since July 22, 2025, over 75 malicious ads have targeted tens of thousands of users across the European Union. The campaign also affects Windows desktops through the same malvertising strategy, posing as financial or cryptocurrency apps.
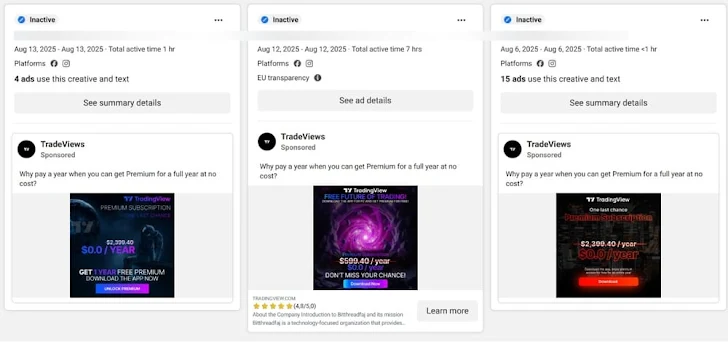
“This campaign demonstrates how cybercriminals adjust their techniques to align with user habits,” Bitdefender noted. “By targeting mobile users and disguising malware as trusted trading tools, attackers aim to exploit the increasing popularity of crypto and financial applications.”
Indicators of Compromise (IOCs)
| Type | Indicator | Description |
|---|---|---|
| Android Package Name | com.fluvdp.hrzmkgi | PM YOJANA 2025 dropper targeting Indian users |
| Android Package Name | com.epr.fnroyex | RTO Challan dropper |
| Android Package Name | com.qmwownic.eqmff | SBI Online dropper |
| Android Package Name | com.tolqppj.yqmrlytfzrxa | Axis Card dropper |
| Malware Families | RewardDropMiner | Dropper delivering spyware, previously included Monero miner |
| Malware Families | SecuriDropper | Dropper variant evading Play Protect |
| Malware Families | Zombinder | Dropper variant evading Play Protect |
| Malware Families | BrokewellDropper | Dropper variant evading Play Protect |
| Malware Families | HiddenCatDropper | Dropper variant evading Play Protect |
| Malware Families | TiramisuDropper | Dropper variant evading Play Protect |
| Network / Payload | Remote server URLs | External servers used to download actual payload after user interaction |
| Campaign | Facebook Malvertising | Delivery of Brokewell trojan via fake TradingView app ads |
| Affected Region | India, EU | Targeted regions for mobile malware campaigns |