A new and sophisticated phishing campaign is currently targeting PayPal users, exploiting deceptive emails titled “Set up your account profile” to compromise accounts through a clever secondary user addition scheme.
This scam uses advanced email spoofing and psychological manipulation to bypass traditional security measures, marking a notable evolution in online financial fraud.
The fraudulent emails are designed to look like they come from legitimate PayPal addresses, such as service@paypal.com or service@paypal.co.uk.
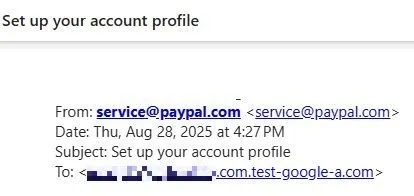
However, attackers manipulate email headers using spoofing techniques that exploit weaknesses in email authentication protocols. This allows them to display seemingly legitimate sender addresses, taking advantage of the fact that many email systems do not verify the “From” field stringently.
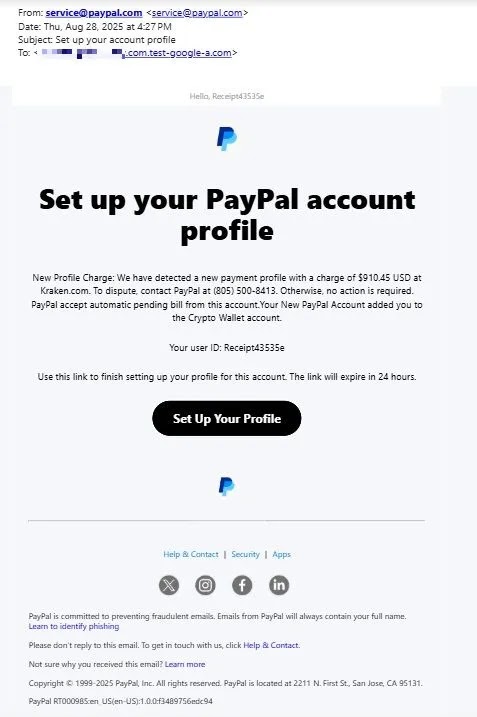
Recipients receive alarming notifications about a new payment profile with charges of $910.45 USD at Kraken.com, a recognized cryptocurrency trading platform. The messages mimic PayPal’s official branding and design, likely copied from real PayPal communications.
Key Red Flags Identified
Malwarebytes experts highlighted several warning signs, including:
- Strange recipient addresses using compromised domains like .test-google-a.com
- Subject lines that do not match the email content
- Lack of personalized greetings, which are standard in genuine PayPal emails
Advanced Account Takeover Technique
The most dangerous aspect of this campaign is the use of authentic PayPal infrastructure instead of typical phishing websites.
When users click the links, they are redirected to PayPal’s official secondary user addition process, rather than a fake profile setup or payment dispute page.
This approach is unique, as it uses PayPal’s own functionality for malicious purposes. Adding a secondary user grants attackers significant privileges, including payment authorization.
Once added, threat actors can access the victim’s PayPal balance and perform unauthorized transactions. Since the URLs resolve to legitimate PayPal domains, many traditional anti-phishing tools and even cautious users may fail to detect the attack.
Scope of the Campaign
The phishing operation has reportedly been active for over a month, targeting PayPal’s 434 million active users through databases containing email addresses linked to PayPal accounts or prior interactions.


