Cybersecurity researchers have uncovered a sophisticated phishing campaign abusing Scalable Vector Graphics (SVG) files to spread malicious content disguised as official documents from the Colombian judicial system.
According to a report from VirusTotal, the attackers distribute the SVG files through email. These files contain hidden JavaScript code that decodes and loads a Base64-encoded phishing page posing as a legitimate portal of Fiscalía General de la Nación (Office of the Attorney General of Colombia).
Once opened, the phishing page simulates a government-style document download with a fake progress bar. Behind the scenes, it secretly triggers the download of a ZIP archive. While the exact contents of this archive remain unclear, researchers confirmed that the technique enables attackers to slip past common detection systems.
Undetected SVG Malware
VirusTotal identified 44 unique malicious SVG files that successfully bypassed antivirus detection. The attackers relied on methods such as obfuscation, polymorphism, and junk code injection, making it difficult for traditional security tools to recognize the threat. In total, 523 malicious SVG files have been detected since August 14, 2025, with early samples measuring up to 25 MB before shrinking in size as the campaign evolved.
Expanding Threat Landscape: macOS Attacks
This development coincides with rising threats targeting Apple macOS systems. Security firm Trend Micro highlighted the growing use of cracked software and ClickFix-style tactics to spread Atomic macOS Stealer (AMOS).
AMOS is a powerful information-stealing malware capable of harvesting:
- Login credentials
- Browser history and saved data
- Cryptocurrency wallets
- Telegram chat logs
- VPN profiles
- Keychain and Apple Notes data
- Files from commonly used directories
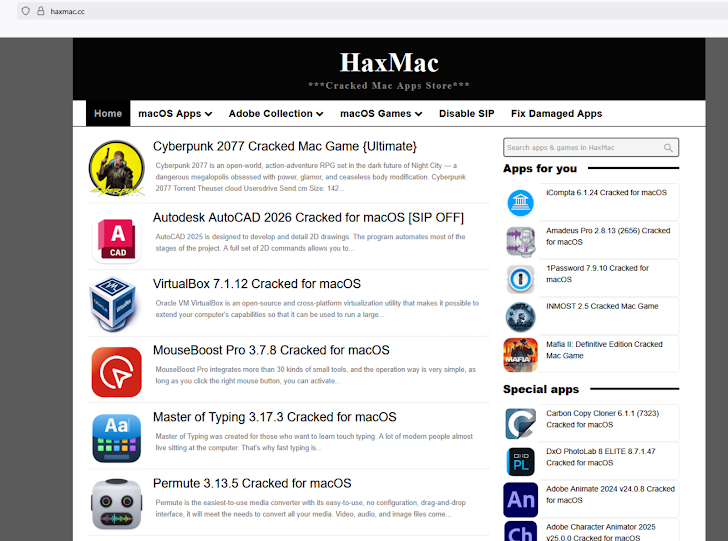
Attackers lure victims with cracked applications on sites like haxmac[.]cc, tricking them into following installation instructions that execute malicious commands in the Terminal app, leading to AMOS deployment.
Apple’s Security Response
Apple’s Gatekeeper feature, along with the release of macOS Sequoia, prevents unsigned or unverified .dmg files from being installed. While this reduces traditional infection attempts, cybercriminals now increasingly rely on ClickFix methods using curl commands in Terminal, which bypass standard protections.
Trend Micro noted, “Although Sequoia blocks unsigned .dmg-based attacks, adversaries quickly shifted to Terminal-based methods that are harder to detect, highlighting the need for multi-layered defenses.”
Growing Cybercrime Targeting Gamers
The threat landscape is expanding further, with CyberArk reporting a large-scale campaign targeting gamers with StealC malware. This malware uses loader functionality to deliver additional payloads, including cryptocurrency stealers, netting attackers over $135,000 in stolen assets.
These campaigns highlight a dangerous trend where attackers weaponize diverse platforms — from SVG files in phishing campaigns to cracked macOS software and gaming communities — to achieve financial gain and data theft.


