Cybersecurity experts have recently uncovered an evolved form of a cryptojacking campaign that leverages the TOR network to target misconfigured Docker APIs.
Akamai, which identified this activity in August 2025, reported that the attackers attempt to lock down exposed Docker APIs to prevent other threat actors from gaining access.
This development expands on Trend Micro’s findings from June 2025, which documented a malicious operation exploiting vulnerable Docker environments. That campaign stealthily deployed an XMRig cryptocurrency miner while relying on a TOR domain for anonymity.
Yonatan Gilvarg, a security researcher, explained that while the new variant appears to reuse some of the same tools, its ultimate objective may differ. According to him, it could be laying the groundwork for a large-scale botnet.
Attack Methodology
The intrusion begins with exploitation of misconfigured Docker APIs. Attackers create a container based on the Alpine Docker image, mounting the host file system into it. A Base64-encoded payload is then executed to fetch a shell script from a TOR-based (.onion) server.
The downloaded script alters SSH settings to establish persistence and installs tools such as masscan, libpcap, libpcap-dev, zstd, and torsocks. These are used for reconnaissance, contacting command-and-control (C2) infrastructure, and retrieving an additional binary from another hidden service.
Gilvarg noted that the first file downloaded is a Go-based dropper containing all the embedded resources it deploys. It avoids external communication except for dropping another binary. Interestingly, the dropper also reads the utmp file to identify currently logged-in users, even using an emoji in its source code to mark them, suggesting possible use of a large language model (LLM) during development.
The malware then launches Masscan to detect systems with Docker APIs exposed on port 2375 and spreads by repeating the same container-creation process.
Potential Expansion of Capabilities
The binary also scans for ports 23 (Telnet) and 9222 (remote debugging for Chromium). While the logic for these attack paths is incomplete, it points toward future enhancements.
- Telnet Route: The malware attempts brute-force logins using known default credentials for routers and IoT devices. Successful logins are exfiltrated to a webhook[.]site endpoint, containing IP addresses and compromised credentials.
- Chromium Route: By using the Go library chromedp, the malware attaches to Chromium’s remote debugging port. This technique, already abused by North Korean groups and stealer malware, can extract cookies, session data, and other sensitive information. It also sends collected data to a TOR domain endpoint labeled httpbot/add, raising concerns that compromised browsers could be recruited into a botnet for data theft or DDoS campaigns.
Although current scans are limited to Docker APIs, the existence of these unused features shows that the malware developers are preparing for expanded attack capabilities.
Gilvarg stressed that preventing exposure of sensitive services is critical. Proper network segmentation, restricting internet-facing APIs, and avoiding default credentials are essential defenses against such attacks.
AWS SES Abuse Campaign Uncovered
In a separate incident, cloud security company Wiz disclosed a phishing campaign that exploited Amazon Simple Email Service (SES) in May 2025. Attackers used stolen AWS access keys to launch large-scale phishing operations.
The exact method of key theft remains unclear. However, common attack vectors include accidental exposure in public code repositories, insecure configurations, or credential theft through malware.
According to Wiz researchers Itay Harel and Hila Ramati, the attackers bypassed SES restrictions, added new sender identities, and carried out phishing attacks using tax-related lures. Victims were redirected to credential harvesting websites.
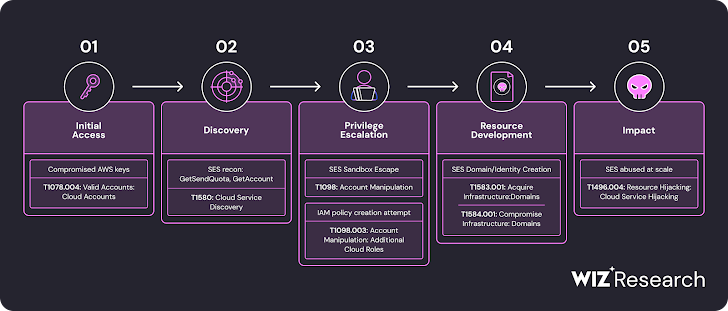
The phishing emails targeted multiple organizations across different sectors and regions. Wiz warned that once SES is misused, attackers can impersonate legitimate domains, leading to spearphishing, fraud, and data theft.
AWS, in response, reiterated that customers should follow best practices to secure their accounts. The company also advised reporting any misuse of AWS resources through its abuse reporting form.


