Cybersecurity experts have identified a new malware loader, dubbed CountLoader, being actively used by Russian ransomware operators. This loader is designed to deliver post-exploitation frameworks such as Cobalt Strike and AdaptixC2, along with a remote access trojan known as PureHVNC RAT.
According to Silent Push, CountLoader is deployed either as part of an Initial Access Broker (IAB) toolkit or directly by affiliates connected to ransomware groups including LockBit, Black Basta, and Qilin.
Multiple Versions and Phishing Campaigns
CountLoader has been spotted in three separate versions (.NET, PowerShell, and JavaScript). Current campaigns target individuals in Ukraine, using PDF-based phishing lures that impersonate the National Police of Ukraine. Silent Push disclosed to The Hacker News that it remains unclear which additional malware strains were dropped through CountLoader in these campaigns.
Earlier, Kaspersky flagged the PowerShell variant, noting its distribution through DeepSeek-related decoys. These attacks resulted in the deployment of BrowserVenom, an implant capable of rerouting all browsing sessions through attacker-controlled proxies, allowing for traffic manipulation and data harvesting.
Technical Capabilities of CountLoader
Silent Push’s analysis revealed that the JavaScript variant is the most advanced, incorporating:
- Six different download methods (curl, PowerShell, MSXML2.XMLHTTP, WinHTTP.WinHttpRequest.5.1, bitsadmin, certutil.exe)
- Three execution methods for running malware binaries
- Victim fingerprinting based on Windows domain details
In addition, the malware can harvest system information, create scheduled tasks disguised as Google Chrome updates for persistence, and connect to remote servers for further commands. Its ability to fetch and execute DLL and MSI payloads via rundll32.exe and msiexec.exe further underscores its flexibility.
Silent Push highlighted that by leveraging LOLBins (Living-off-the-Land Binaries) like certutil and bitsadmin, paired with dynamic PowerShell command encryption, CountLoader demonstrates a deep understanding of Windows internals and malware engineering.
Notable Features and Infrastructure
One distinctive aspect of CountLoader is its use of the victim’s Music folder as a staging area. While the .NET version shares some overlap with the JavaScript build, it is a stripped-down variant supporting only two command types: UpdateType.Zip and UpdateType.Exe.
CountLoader operates across 20+ unique domains, enabling delivery of Cobalt Strike, AdaptixC2, and PureHVNC RAT. Notably, PureHVNC RAT is a commercial malware developed by a threat actor known as PureCoder, and it served as a precursor to PureRAT (ResolverRAT).
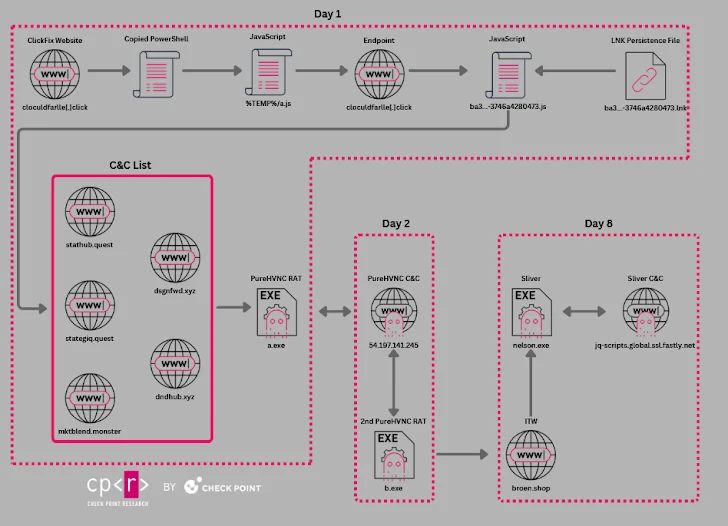
Recent campaigns distributing PureHVNC RAT have exploited the ClickFix phishing technique, often disguised as fake job offers. Victims were redirected to phishing pages where malicious PowerShell payloads were executed. According to Check Point, PureCoder maintains multiple GitHub accounts to support PureRAT operations.
Analysis of GitHub activity linked to PureCoder indicated activity consistent with the UTC+03:00 timezone, which covers Russia and nearby regions.
Insights into the Russian Ransomware Ecosystem
Parallel research by DomainTools Investigations revealed strong interconnections between different ransomware actors in Russia. Their findings show that these groups commonly use AnyDesk and Quick Assist, tools that allow remote access, further evidencing collaboration and resource sharing.
DomainTools concluded that brand loyalty among ransomware actors is weak. Instead, trust-based personal networks dominate. Operators frequently shift affiliations, reorganize after law enforcement crackdowns, and adapt to market changes. The primary asset is human expertise, not specific malware families.


