Cybersecurity experts are sounding the alarm over a rising threat vector, as malicious actors increasingly exploit Dynamic DNS (DDNS) providers to create resilient command and control (C2) infrastructure.
These subdomain rental services, originally intended for legitimate hosting purposes, have become a preferred tool for cybercriminals seeking to bypass traditional security defenses and regulatory oversight.
The growing sophistication of attacks using DDNS services highlights an evolution in cybercriminal infrastructure, with serious implications for enterprise security worldwide.
Why Threat Actors Prefer Dynamic DNS Providers
The appeal of Dynamic DNS lies in its ease of access and limited oversight. Unlike traditional domain registrars that operate under ICANN and IANA regulations, DDNS providers typically require minimal registration details and impose weaker enforcement mechanisms.
This regulatory gap enables cybercriminals to quickly set up malicious infrastructure without undergoing strict identity verification, lowering the risk of immediate takedowns.
Recent studies reveal that approximately 70,000 domains offering subdomain rental services are currently being abused by threat actors. These platforms allow attackers to host malicious content under the cover of legitimate parent domains, further masking their activities.
Since DNS records are automatically managed by the providers, attackers benefit from an additional layer of operational security that obscures their direct involvement.
Evidence of Advanced Persistent Threat (APT) Abuse
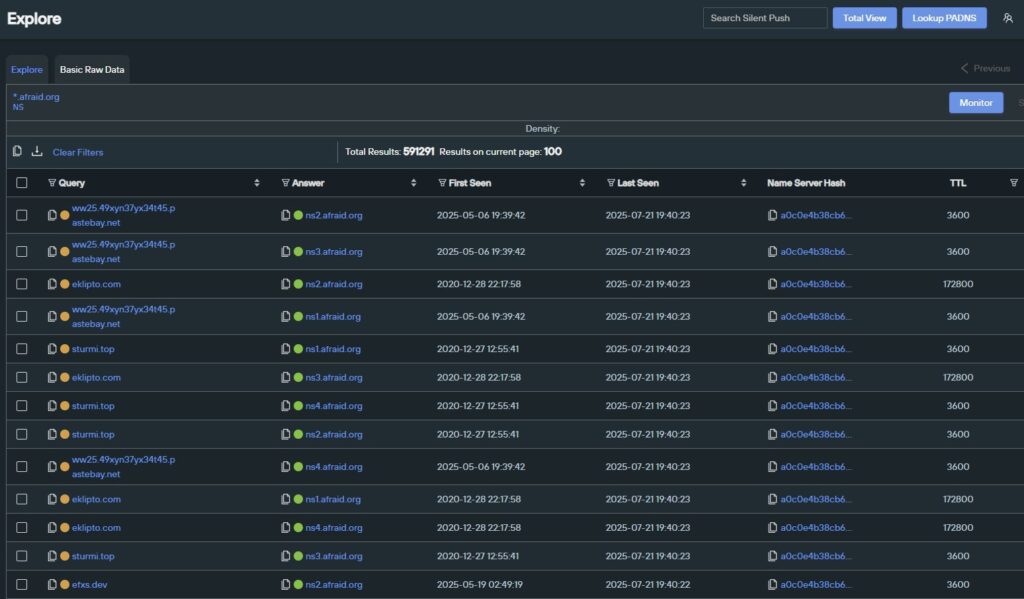
Security analysts at Silent Push have uncovered multiple high-profile threat groups leveraging DDNS services.
- APT28 (Fancy Bear) has repeatedly used Dynamic DNS domains in documented campaigns.
- APT29 integrated DDNS infrastructure into its QUIETEXIT C2 operations, proving the strategic value of these services for long-term persistence.
- Chinese APT groups, including APT10 and APT33, also use DDNS in their playbooks, reflecting the global adoption of this tactic across different regions.
Command and Control Infrastructure Abuse
One of the most concerning uses of DDNS is in command and control communications. These services enable attackers to maintain persistent communication with compromised machines while remaining flexible and resistant to takedown attempts.
The distributed nature of these providers complicates monitoring and blocking efforts by traditional security solutions.
From a technical perspective, attackers exploit multiple layers of obfuscation and redundancy. By registering numerous subdomains across providers and employing domain generation algorithms (DGAs), they can seamlessly rotate between active C2 nodes.
This rotation ensures continuity of operations, even if specific domains are identified and blocked. The use of automated DNS record management further reduces the attacker’s need to maintain direct infrastructure, shrinking their digital footprint.
Long-Term Persistence Strategies
Investigations show that threat actors often pre-register dozens of subdomains and activate them on a timed schedule. This rotation technique allows them to extend campaign lifespans while hiding the scope of their infrastructure.
With low costs, minimal verification, and built-in redundancy, Dynamic DNS services allow attackers to maintain large-scale backup infrastructure. This creates major challenges for defenders tasked with tracking, disrupting, and mitigating these operations.
Conclusion
The abuse of Dynamic DNS providers demonstrates how cybercriminals exploit regulatory and technical blind spots to strengthen their campaigns. As state-sponsored and financially motivated groups continue to adopt this approach, organizations must enhance their detection and defense strategies to counter the growing threat of DDNS-enabled infrastructure.


