A persistent threat actor known as Confucius has been linked to a fresh phishing campaign focused on Pakistan, deploying information stealers and, more recently, a Python-based backdoor. Security firms have observed the group using malware families such as WooperStealer and Anondoor to harvest sensitive data and to establish longer-term access on compromised systems.
Background and targets,
Confucius is a long-running hacking group, active since around 2013, operating primarily across South Asia. Over the years the group has repeatedly targeted government bodies, military-related organizations, defense contractors, and critical infrastructure, using spear-phishing and weaponized documents as the primary initial access vectors, according to Fortinet FortiGuard Labs researcher Cara Lin.
Attack chains and timelines
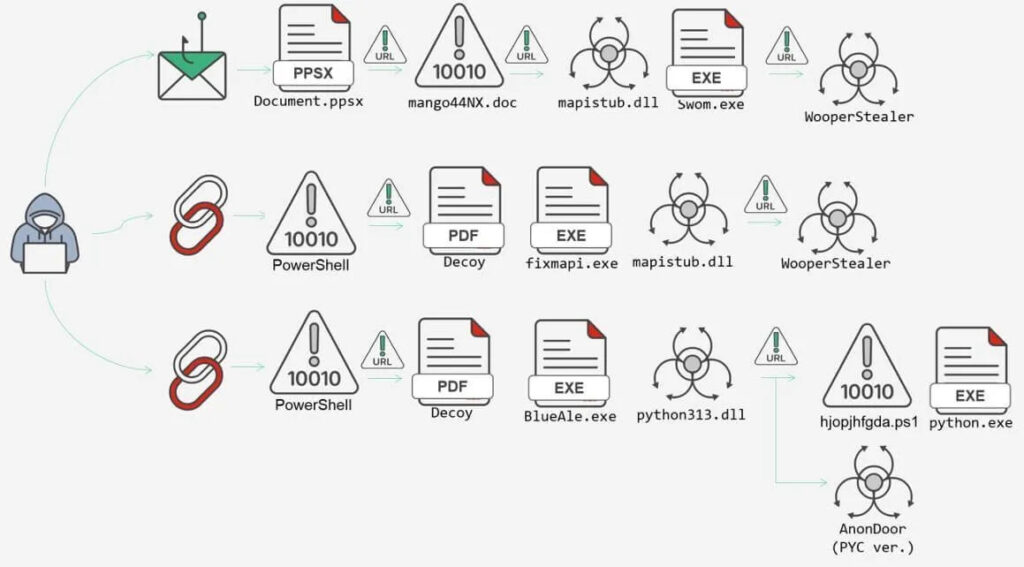
Security researchers documented multiple waves of activity that affected users in Pakistan, beginning with incidents observed in December 2024. In that campaign, recipients were tricked into opening a .PPSX file, which initiated a chain of events that delivered WooperStealer through DLL side-loading techniques. A later wave, observed in March 2025, relied on malicious Windows shortcut (.LNK) files to execute a WooperStealer DLL, again leveraging DLL side-loading to evade detection while extracting data from infected hosts.
Transition to backdoor operations
In August 2025 a similar attack used a .LNK file to sideload a malicious DLL which, instead of only acting as a stealer, paved the way for Anondoor. Anondoor is a Python implant that collects device information and communicates with a remote server, awaiting further instructions. Its capabilities include executing commands, taking screenshots, enumerating files and directories, and extracting stored browser passwords, including credentials from Google Chrome. The move from pure information theft towards deploying a backdoor signals the actor’s shift toward persistent monitoring and longer-term access.
Techniques and evasions
Confucius has shown strong operational adaptability, layering obfuscation and using trusted or abused DLLs to perform side-loading, a technique that enables malicious code to run under the guise of legitimate processes. This approach reduces detection likelihood by security tools that trust signed or common executables. The threat actor customizes tooling and tactics to match intelligence objectives, enabling quick pivots between different malware families and delivery methods.
Industry observations and corroboration
The appearance of Anondoor was independently documented in July 2025 by Seebug’s KnownSec 404 Team, corroborating the shift toward backdoor implants. Fortinet emphasized the group’s ability to change infrastructure and toolsets rapidly, sustaining operational effectiveness across campaigns. Additional analysis from K7 Security Labs detailed a related infection sequence tied to the Patchwork group, which begins with a malicious macro that downloads a .LNK file containing embedded PowerShell code. That script then fetches further payloads and uses DLL side-loading to launch the main malware while showing a decoy PDF to the user.
Payload behavior and persistence
In the campaigns described by security vendors, the final payload establishes contact with the actor’s command-and-control (C2) infrastructure, gathers system telemetry, and retrieves encoded instructions which are decoded and executed via cmd.exe. The implant is capable of uploading files, downloading remote resources to temporary storage, taking screenshots, and persistently attempting exfiltration. One notable behavior recorded by analysts is a configurable retry mechanism, where the malware waits between attempts and retries up to 20 times, tracking failures to maximize data transfer success without raising immediate alerts.
Implications for defenders
The combination of information-stealing malware and the deployment of a Python backdoor increases the risk profile, as attackers gain both immediate exfiltration capability and long-term footholds. Organizations, especially those in targeted sectors, should prioritize email hygiene, user awareness training, and layered defenses, including email attachment scanning, macro protection, application allowlisting, and monitoring for abnormal DLL loading and unusual outbound connections. Regular patching and endpoint hardening reduce the attack surface for side-loading and script-based payloads.