A threat actor, tracked by security researchers as Cavalry Werewolf, has been observed targeting Russian government organisations and critical industry networks, using malware families known as FoalShell and StallionRAT. Cybersecurity vendor BI.ZONE links this cluster to multiple other tracked groups, including SturgeonPhisher, Silent Lynx, Comrade Saiga, ShadowSilk, and Tomiris, which suggests overlapping toolsets and tactics.
What happened, and who is targeted
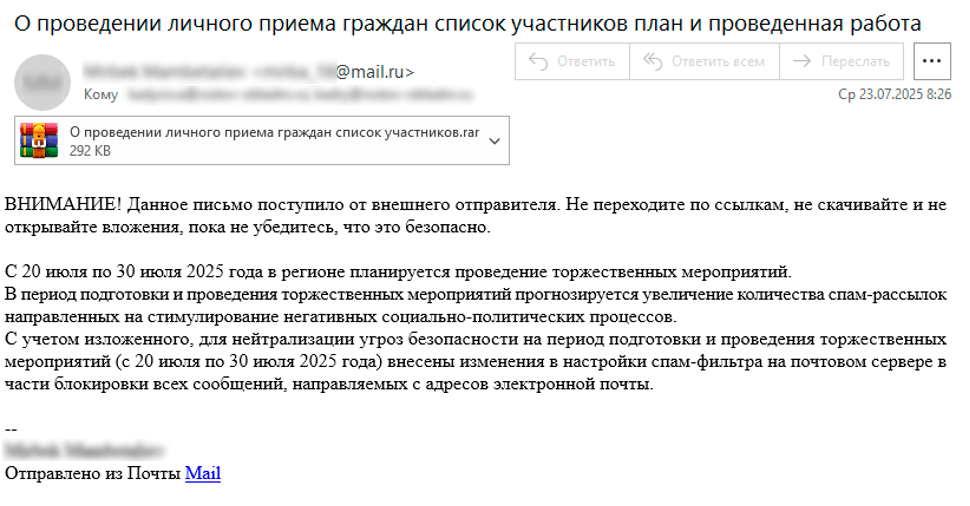
Between May and August, 2025, defenders recorded targeted phishing campaigns aimed primarily at Russian state agencies, and at organisations in energy, mining, and manufacturing sectors. The attackers impersonated Kyrgyz government officials, sending messages that delivered RAR archives, which unpacked either FoalShell or StallionRAT on victim systems. In at least one incident, the adversary used a legitimately compromised email address from a Kyrgyz regulatory body to distribute malicious mail, increasing the credibility of their lures.
Tools and techniques, high level
Cavalry Werewolf uses a compact toolkit focused on remote command execution, persistence, and data theft. Key elements observed include, but are not limited to:
- FoalShell, a lightweight reverse shell that appears in Go, C++, and C# variants, enabling arbitrary command execution via cmd.exe on compromised hosts.
- StallionRAT, implemented in Go, PowerShell, and Python, providing capabilities to run commands, load additional modules, and exfiltrate data.
- Supplementary utilities such as ReverseSocks5Agent and ReverseSocks5, plus commands to enumerate device details and maintain access.
StallionRAT, Telegram exfiltration, and supported commands
StallionRAT’s operators employ a Telegram bot as a command-and-control, allowing remote operators to manage infected devices, and to collect stolen data. Observed bot commands include, for example:
- /list, returns a roster of compromised hosts, showing DeviceID and computer name
- /go [DeviceID] [command], executes the specified command on the target, using Invoke-Expression
- /upload [DeviceID], uploads a file to the victim endpoint
These capabilities let attackers run arbitrary commands, deploy additional files, and siphon data back to their infrastructure, while blending with normal network traffic.
Attribution clues and regional context
BI.ZONE notes substantial ties between Cavalry Werewolf and groups such as Tomiris, which supports a working hypothesis that some operators may be affiliated with Kazakhstan-related clusters. Microsoft, in a prior report, linked the Tomiris backdoor to a Kazakhstan-based actor tracked as Storm-0473. Separately, Group-IB revealed ShadowSilk activity in August, 2025, targeting Central Asian and APAC government entities with proxy tools and remote access trojans originally developed in Python, then ported to PowerShell, which shows parallels in tool evolution across these clusters.
Wider findings from BI.ZONE
BI.ZONE’s telemetry also highlights a concerning trend across Russia, where, over the last year, underground publications and leak channels revealed compromises of at least 500 organisations, spanning commerce, finance, education, and entertainment. In about 86 percent of those incidents, attackers first breached public-facing web applications, then installed lightweight persistent backdoors such as gs-netcat, and occasionally additional web shells. Attackers frequently used legitimate database tools, for example Adminer, phpMiniAdmin, and mysqldump, to extract records, which complicates detection because the activity can resemble normal administrative tasks.
Why this matters
The blend of targeted phishing, legitimate-seeming sender addresses, lightweight cross-platform tools, and use of commodity utilities makes these campaigns hard to detect and contain. The expansion of Cavalry Werewolf’s arsenal, and overlaps with other named clusters, increases the risk to regional public sector entities and industrial organisations, particularly those with externally facing applications and weak web exposure controls.
Practical guidance for defenders
To reduce exposure to similar campaigns, organisations should prioritise these controls, at minimum:
- Harden email security, use sender authentication (SPF, DKIM, DMARC), and apply targeted phishing simulations and user training.
- Inspect and restrict archive handling policies, especially for RAR and other compressed attachments, at gateway and endpoint stages.
- Monitor for unusual use of common administration tools, for example mysqldump, Adminer, and phpMiniAdmin, and set behavioural alerts on atypical exports or remote execution.
- Employ endpoint detection that can spot reverse shells, suspicious PowerShell usage, and unexpected Go or C# binaries running with network sockets.
- Maintain strict logging and rapid incident response playbooks so that if an attacker achieves initial access, containment can be swift.