Shuyal Stealer has quickly become one of the most flexible credential theft tools observed in recent months. First seen in early August, its modular design enables it to target a wide variety of web browsers, including Chromium-based, Gecko-based, and legacy engines, making it a high-risk threat for many environments.
Early signs and impact
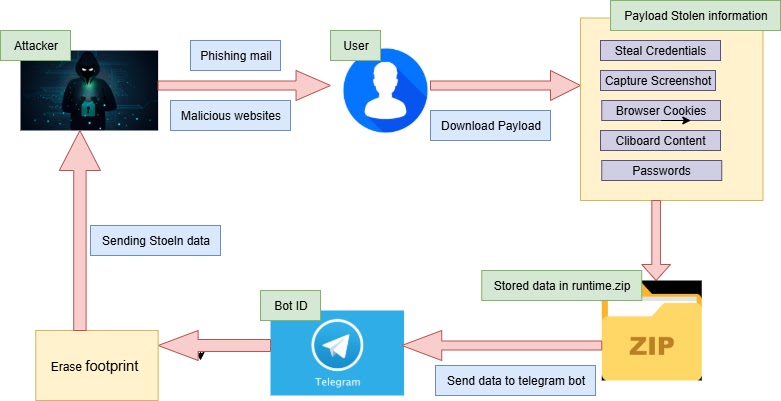
Initial indicators of compromise included unusual network activity from infected machines, unexplained browser crashes, and a sudden rise in outbound connections to unfamiliar command and control servers. Point Wild researchers reported that within days of discovery, Shuyal Stealer had breached hundreds of endpoints across multiple sectors, including finance, healthcare, and manufacturing. The malware is typically distributed through social engineering, usually disguised as software updates or utility installers, delivered via phishing emails or malicious advertisements.
Delivery, side-loading, and persistence
The attacker delivers Shuyal Stealer as a self-extracting archive. The archive unpacks and executes a legitimate system binary together with an obfuscated DLL loader, using a side-loading technique to evade many application whitelisting solutions. The loader writes the benign executable, for example svchost.exe, into the Windows directory, drops a malicious DLL beside it, and registers the executable to run at logon, typically by adding an entry under HKCU\Software\Microsoft\Windows\CurrentVersion\Run. Because Windows resolves DLLs by name, the legitimate executable ends up loading the malicious DLL automatically, establishing persistence.
In-memory unpacking and process injection, technical overview
Once the malicious DLL is loaded, its DllMain triggers a staged unpacker. The unpacker decrypts an embedded payload in memory, allocates memory in a target browser process, writes the payload into that process, and spawns a remote thread to run it. By keeping the primary payload in memory and reusing legitimate binaries, the malware avoids writing its core components to disk, reducing detection opportunities.
A simplified unpack routine looks like this, showing the core steps:
// Simplified unpack routine
void UnpackAndInject() {
BYTE* encryptedPayload = LoadResource(MAKEINTRESOURCE(101));
BYTE* payload = DecryptAES256(encryptedPayload, payloadSize, key, iv);
HANDLE hProc = OpenProcess(PROCESS_ALL_ACCESS, FALSE, targetPid);
LPVOID remoteMem = VirtualAllocEx(hProc, NULL, payloadSize, MEM_COMMIT, PAGE_EXECUTE_READWRITE);
WriteProcessMemory(hProc, remoteMem, payload, payloadSize, NULL);
CreateRemoteThread(hProc, NULL, 0, (LPTHREAD_START_ROUTINE)remoteMem, NULL, 0, NULL);
}The loader also uses API hashing and encrypted string tables to hide calls to key Windows functions such as LoadLibrary and GetProcAddress, complicating static analysis.
Data collection and exfiltration
After injection, the stealer harvests cookies, saved passwords, autofill entries, and other credentials from browser SQLite databases and from memory. It supports 19 browsers, including mainstream browsers like Chrome, Edge, Firefox, Opera, Vivaldi, and Brave, as well as lesser-known regional forks. The malware can extract banking session tokens and cached two-factor authentication approvals where available.
Collected data is compressed using a custom ZIP implementation, then encrypted with AES-256 in CBC mode. Network analysis shows stolen data is batched into 512 KB chunks and sent over HTTPS to a per-victim, dynamically generated subdomain, which increases the complexity of takedown and attribution efforts.
Evasion techniques and analysis challenges
Shuyal Stealer combines several stealth techniques, including DLL side-loading, in-memory payload decryption and injection, API hashing, and the use of legitimate binaries, all of which reduce forensic artifacts and hinder endpoint detection. These approaches make static signatures less effective, and they force defenders to rely more on behavioral detection and network telemetry.


