A new wave of sophisticated ransomware attacks is targeting organizations worldwide by abusing legitimate database commands, bypassing traditional security tools through “malware-free” operations.
Unlike typical ransomware that relies on malicious binaries to encrypt files, attackers are exploiting exposed database services, using standard database functionality to steal, erase, and demand ransom for critical information.
This technique represents a significant shift in cybercriminal tactics, focusing on internet-facing database servers with weak or absent authentication controls.
Affected Database Platforms
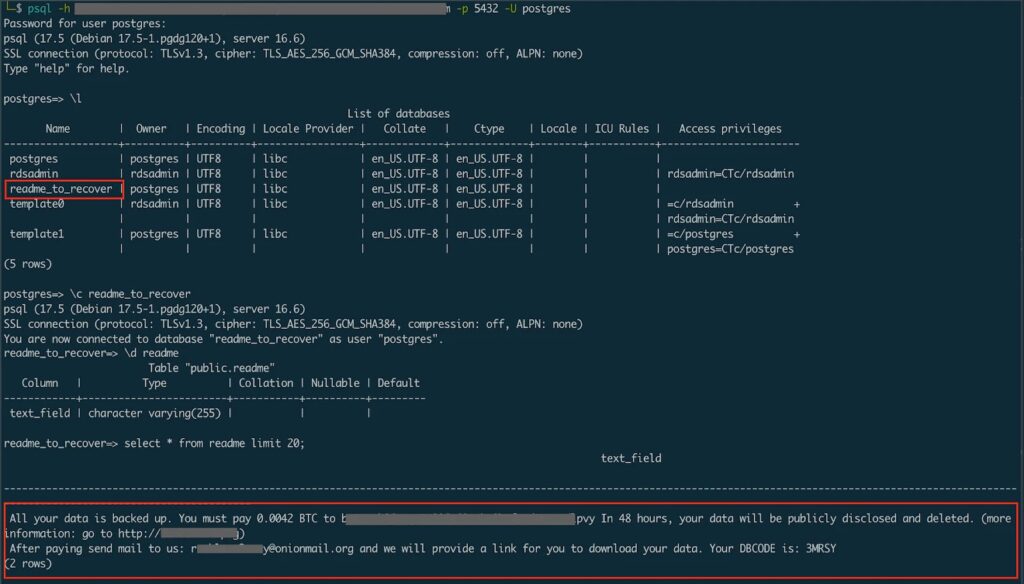
These attacks have been reported across multiple database platforms including MySQL, PostgreSQL, MongoDB, Hadoop, CouchDB, and Elasticsearch. Cybercriminals remotely access these servers, copy sensitive data to external locations, execute destructive commands to erase databases, and leave ransom notes within the compromised database structures.
This malware-free approach is particularly effective in avoiding detection since no malicious files are installed on the target system. All damage is carried out using legitimate database commands, which makes it difficult for conventional security solutions to recognize the breach.
The ransom strategy has escalated from isolated incidents to automated campaigns, with bots continuously scanning for misconfigured databases.
According to Wiz.io researchers, these attacks have grown exponentially since February 2017, when Rapid7 first documented thousands of open databases being hijacked. Modern attackers now operate automated systems capable of compromising newly exposed targets within hours or even minutes.
Attack Methodology and Exploited Commands
The attacks follow a systematic approach designed for maximum stealth and impact.
Attackers begin by scanning the internet for exposed database ports, focusing on port 3306 for MySQL and port 5432 for PostgreSQL servers.
After identifying potential targets, they use fingerprinting techniques to confirm genuine database services, avoiding honeypots or decoy systems.
Authentication bypass is a critical phase where attackers test for missing authentication controls, try default credentials, and perform brute-force attacks on weak passwords.
Once authenticated, attackers proceed to extract small samples of data to verify access and assess value. The destructive phase uses standard SQL commands, such as DROP DATABASE or bulk DELETE, to erase data systematically.
In relational databases like PostgreSQL, attackers create tables with names like RECOVER_YOUR_DATA or README_TO_RECOVER to store ransom notes as table rows. In NoSQL databases like MongoDB, they create collections with similar names and insert ransom messages as documents.
A captured MongoDB session shows the attack flow: mongosh “mongodb://target:27017/” followed by enumeration commands like show dbs to locate valuable targets. The ransom notes usually state messages such as:
“All your data is backed up. You must pay 0.043 BTC to recover it. After 48 hours, we will leak and expose all your data.