Cybersecurity threats are advancing faster than ever, with attackers increasingly combining social engineering, AI-driven manipulation, and cloud exploitation to target systems once deemed secure. From communication platforms to smart devices, every technological convenience simultaneously expands the potential attack surface.
This edition of ThreatsDay Bulletin highlights these overlapping risks and the necessary measures to maintain trust in a landscape dominated by intelligent threats.
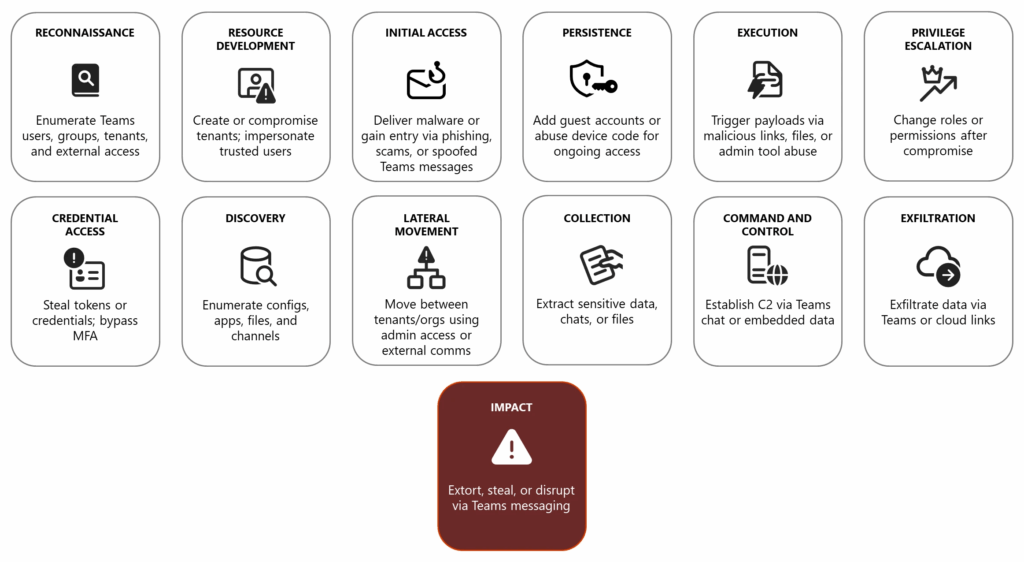
Microsoft Teams Exploitation by Threat Actors
How Attackers Exploit Teams for Extortion, Social Engineering, and Financial Gain
Microsoft has revealed how cybercriminals are abusing Teams chat software across multiple stages of the attack chain, including financial theft via extortion and social engineering. “Octo Tempest has leveraged communication apps like Teams to send intimidating messages to organizations, defenders, and incident response teams as part of extortion and ransomware tactics,” Microsoft explained. “By hijacking MFA using social engineering techniques and password resets, attackers gain access to Teams to identify sensitive information that fuels financially motivated operations.”
Recommended Safeguards: Strengthen identity protection, secure endpoints, and safeguard Teams clients and integrated apps.
LNK Files in a New Malware Campaign
Malicious Shortcut Files Deliver PowerShell Droppers and DLL Implants
A new campaign distributing ZIP archives themed around passports or payments contains malicious Windows shortcut (.LNK) files, which execute a PowerShell dropper that installs a DLL implant on infected devices. These archives are spread through phishing emails.
Blackpoint Cyber detailed, “The staged payload launches the DLL implant using rundll32.exe and connects to faw3[.]com. The dropper evades detection by constructing commands from byte arrays, suppressing output, clearing consoles, and renaming files based on antivirus processes. The implant runs in user context, enabling remote tasks, host reconnaissance, and additional payload delivery while blending into normal Windows activity.”
AI Disinformation Campaign Targeting Iran
Israeli-Linked Network Uses Deepfakes and AI to Influence Iranian Public
Citizen Lab reported that an Israeli-backed network of roughly 50 X accounts, codenamed PRISONBREAK, pushed anti-government propaganda using AI-generated content, aiming to incite unrest in Iran. These accounts, created in 2023, became active in January 2025.
“While overall engagement was limited, some posts received tens of thousands of views,” Citizen Lab said. The campaign appears connected to an Israeli government agency or closely supervised contractor.
Pushback Against E.U. Chat Control
Signal, Tech Firms, and Officials Resist Mass Surveillance Proposal
Signal Foundation’s president warned that new E.U. Chat Control regulations would force encrypted messaging apps to scan all communications and files, prompting Signal to consider leaving the E.U. market.
“Under the guise of child protection, these proposals would enable mass surveillance of all messages, photos, and videos, affecting everyone from government officials to activists,” said Meredith Whittaker.
Over 40 tech companies, including CryptPad, Element, and Tuta, have opposed this proposal in an open letter. German officials also plan to vote against it.
Autodesk Revit File Parsing Leads to Remote Code Execution (RCE)
Researchers discovered a file parsing crash in Autodesk Revit (CVE-2025-5037) that can reliably lead to code execution, even on modern Windows x64 systems. Trend Micro’s Simon Zuckerbraun warned that misconfigurations in Axis cloud amplify the potential for exploitation.
Apple Siri Voice Recording Probe in France
French authorities are investigating Apple for collecting Siri voice recordings following a whistleblower complaint. Apple insists it never used Siri data for marketing, advertising, or selling purposes.
North Korea Linked to $2B Cryptocurrency Theft
North Korean hackers have stolen an estimated $2 billion in cryptocurrency in 2025, including $1.46 billion from the Bybit hack. Other victims include LND.fi, WOO X, and Seedify.
Elliptic highlighted a shift toward targeting high-net-worth individuals, exploiting weak security measures. Okta observed that these actors infiltrated AI-related jobs globally using AI-generated credentials and faces, laundering stolen funds through complex methods like token swapping and bridge protocols.
YoLink Smart Hub Vulnerabilities
Remote Control and Credential Exposure Risks
Security flaws in YoLink Smart Hub (v0382) allow attackers to bypass authentication, control connected devices remotely, and access Wi-Fi credentials in plaintext. Vulnerabilities (CVE-2025-59448, CVE-2025-59449, CVE-2025-59451, CVE-2025-59452) include insecure session management and unencrypted MQTT communication.
Tesla TCU Authentication Bypass
A flaw in Tesla’s telematics control unit (CVE-2025-34251, CVSS: 8.6) allows attackers with physical access to write arbitrary files via ADB, potentially executing code with root privileges.
Spoofed Domains Deliver Malware
Threat actors have used over 80 spoofed websites to deliver Android and Windows malware targeting credentials via fake banking, government, or social media apps. Meta tracking pixels suggest campaigns are promoted via paid traffic.
NoName057(16) Hacktivist Group Resurgence
Following disruption by Operation Eastwood, NoName057(16) has resumed activities, targeting German, Spanish, Belgian, and Italian sites, including municipalities and government portals. Russia-based infrastructure limits global mitigation efforts.
BlackStink Malware Attacks LATAM Banks
Malicious Chrome extensions impersonating Google Docs can remotely hijack banking sessions in Latin America. IBM X-Force reports the malware auto-fills and submits forms to steal credentials and execute real-time fraudulent transfers.
Oracle E-Business Suite Exposed
2,043 Oracle E-Business Suite instances remain internet-accessible, vulnerable to CVE-2025-61882. Attackers, including Cl0p, may exploit this zero-day in extortion campaigns.
Asgard Protector Crypter
Used to evade detection, Asgard Protector distributes payloads like Lumma Stealer and others, decrypting them in memory for execution. Connections to CypherIT are suspected.
WARMCOOKIE Malware Updates
WARMCOOKIE (aka BadSpace) continues development, now using CastleBot for propagation. Latest builds handle DLL/EXE execution and leverage PowerShell scripts for file operations.
Mic-E-Mouse Data Exfiltration
Researchers at UC Irvine demonstrated a method to convert optical mice into microphones, exfiltrating air-gapped network data via neural network analysis of mouse movement vibrations.

Crimson Collective Targets AWS Environments
The Crimson Collective, linked to Red Hat breaches and associated with Scattered Spider and LAPSUS$ groups, exploits AWS environments using leaked IAM credentials. Using the open-source TruffleHog tool, attackers perform reconnaissance, exfiltrate data, and demand ransom.


