Dozens of organizations may have been impacted after threat actors exploited a zero-day vulnerability in Oracle E-Business Suite, starting around August 9, 2025, researchers from Google Threat Intelligence Group, GTIG, and Mandiant reported. The intrusion campaign, which shows hallmarks associated with the Cl0p ransomware brand, used a chain of vulnerabilities to gain remote code execution, exfiltrate data, and launch a high-volume extortion campaign weeks later.
What happened, briefly
Security researchers discovered exploitation of a critical, high-severity flaw tracked as CVE-2025-61882, with a CVSS score of 9.8. Evidence indicates activity going back to July 10, 2025, although the full scope of successful intrusions is still being evaluated. Oracle released patches to address the flaw after the activity was detected.
Attack timeline and campaign mechanics
- July 10, 2025, onward: Signs of suspicious activity were observed, but the level of success varied.
- August 9, 2025: Initial exploitation activity is reported.
- Late August 2025: Researchers observed exploitation of the /OA_HTML/SyncServlet component, used to trigger an XSL payload via Template Preview.
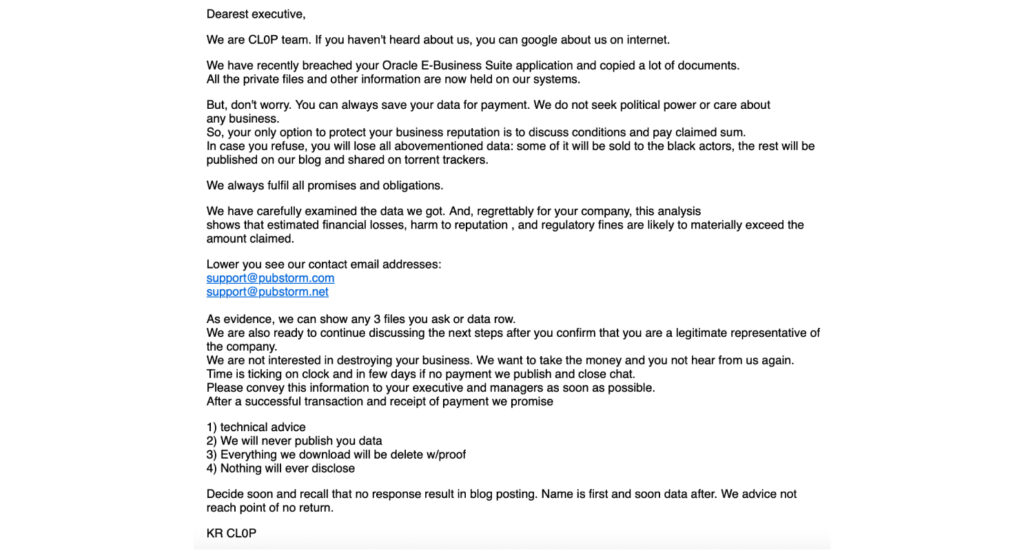
- September 29, 2025: The attackers launched a large-scale, high-volume email extortion campaign targeting executives, sending messages from hundreds of compromised third-party accounts. These accounts were likely acquired through underground markets, possibly from infostealer logs.
The extortion emails claimed the adversary had stolen data from victims’ Oracle EBS instances and demanded payment to avoid public disclosure. As of the reporting, no victims had been posted on the Cl0p leak site, consistent with prior campaigns where actors delay publication.
Technical details, payloads, and techniques
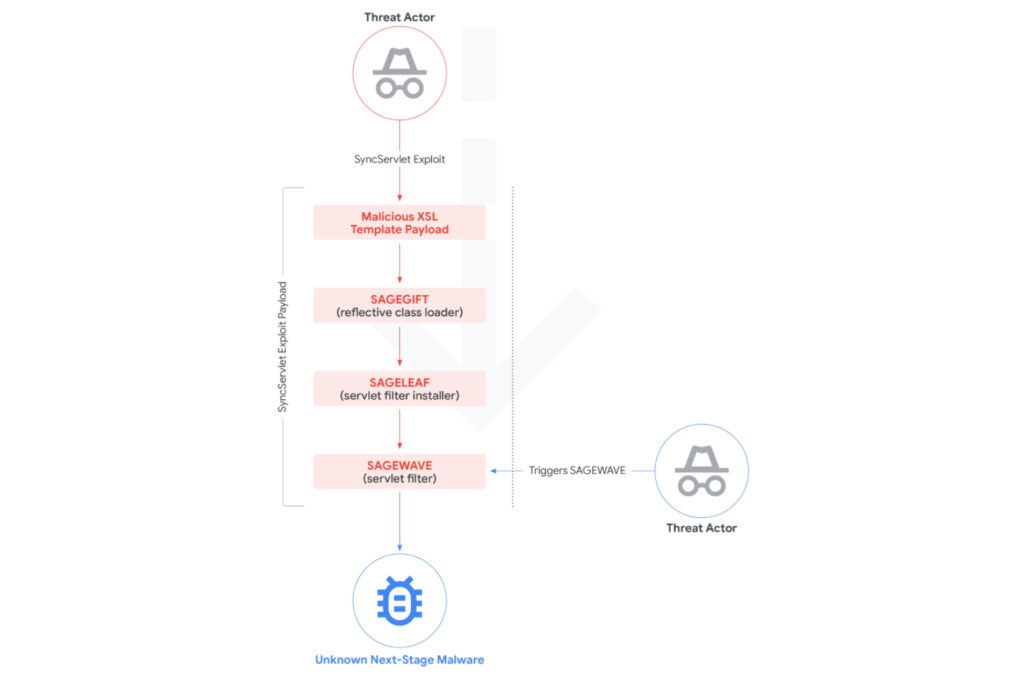
The intrusion combined several exploitation techniques and weaknesses to reach remote code execution on Oracle EBS servers, including, SSRF, CRLF injection, authentication bypass, and XSL template injection. Two distinct Java payload chains were identified embedded in the malicious XSL payloads:
- GOLDVEIN.JAVA, a Java variant of a downloader family called GOLDVEIN, which can fetch second-stage payloads from a command-and-control server. GOLDVEIN has ties to a PowerShell downloader first seen in December 2024 during exploitation campaigns against Cleo products.
- A Base64-encoded loader named SAGEGIFT, tailored for Oracle WebLogic servers, used to deploy SAGELEAF, an in-memory dropper, which then installs SAGEWAVE, a Java servlet filter. SAGEWAVE can deploy an encrypted ZIP archive containing a subsequent payload. Parts of the final payload overlap with a client module found in a FIN11 backdoor called GOLDTOMB.
Post-exploitation activity included reconnaissance commands run from the EBS account applmgr, and execution of bash commands spawned from Java processes running GOLDVEIN.JAVA.
Attribution and actor analysis
Google and Mandiant have noted similarities to previous Cl0p operations, including the branding of the extortion messages. Cl0p, also tracked as Graceful Spider since about 2020, has a history of mass exploitation and data-extortion campaigns against Accellion FTA, GoAnywhere MFT, Progress MOVEit MFT, and Cleo LexiCom.
However, researchers stopped short of a formal, exclusive attribution. The campaign shows overlap with tooling and behaviors previously tied to suspected FIN11 activity, such as GOLDVEIN and GOLDTOMB families, and one breached account used to send extortion emails had earlier links to FIN11 activity. GTIG noted that the overall pattern, exploiting a widely used enterprise application zero-day and following with a large branded extortion campaign weeks later, is consistent with tactics FIN11 has used before, but such methods may appeal to other groups as well.
Researchers also observed artifacts from July 2025 that overlap with an exploit leaked in a Telegram group called Scattered LAPSUS$ Hunters on October 3, 2025, but there is insufficient evidence to tie that group to the campaign.
Strategic context and why this worked
Targeting public-facing enterprise applications that store sensitive data reduces the need for extensive lateral movement, making data theft operations faster and higher yield. The attack required significant up-front reconnaissance and investment, indicating the actor prioritized speed and scale, followed by a branded extortion phase to pressure victims into paying.
Mitigation, response, and recommendations
- Apply Oracle’s published patches for CVE-2025-61882 immediately, if not already installed.
- Audit public-facing EBS instances for signs of compromise, including unusual processes run by applmgr, unexpected Java processes, or suspicious reverse shell activity.
- Review email systems and any third-party accounts used for business workflows, rotate credentials, and apply MFA where possible to reduce the impact of stolen credentials.
- Monitor for indicators of GOLDVEIN, SAGEGIFT, SAGELEAF, SAGEWAVE, and GOLDTOMB families in logs and endpoint telemetry.
- Implement network segmentation and limit external access to administrative EBS components.


