Security researchers have uncovered an active malware campaign, named Stealit, that uses a newer Node.js capability to ship malicious code as single-file executables, enabling infections on systems without Node.js installed. Researchers at Fortinet FortiGuard Labs also note some variants are built with the Electron framework, making delivery simpler and more covert.

How the malware is spread, and what actors offer
Operators behind Stealit distribute the trojan through counterfeit installers that mimic popular games and VPN apps, then upload these fake packages to public file-hosting services such as Mediafire, and to messaging platforms like Discord. The threat actors run a public-facing site that markets “professional data extraction solutions” and sells access to the malware as a service, with subscription tiers for Windows stealers, and a separate pricing structure for an Android remote access trojan (RAT). Windows stealer plans range from $29.99 for a weekly subscription, to $499.99 for a lifetime license, while Android RAT subscriptions span $99.99 up to $1,999.99.
Technical behavior, persistence, and evasion
The fake installers first perform a series of anti-analysis checks to detect virtual machines, sandboxes, and other analysis environments. If those checks pass, the installer writes a Base64-encoded authentication key, a 12-character alphanumeric token, into a temporary cache file at %temp%\cache.json. This key is used to authenticate with a command-and-control server, and it also serves as an account credential for paying customers to access the malware dashboard.
Stealit adjusts Microsoft Defender Antivirus exclusions so the directory containing downloaded components is not scanned, reducing detection. The campaign deploys multiple executables, each with a focused role, for example:
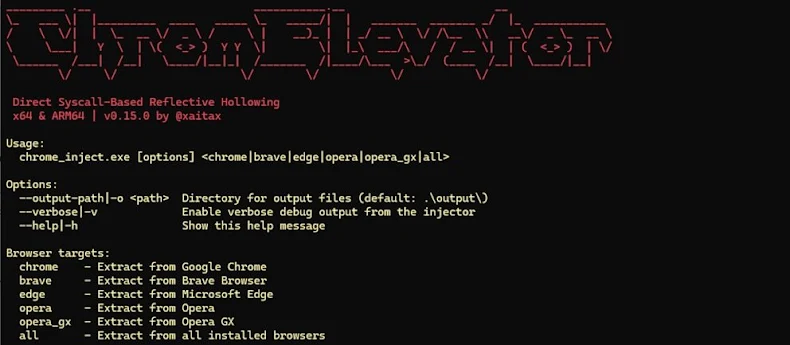
- save_data.exe, executed only when the process has elevated privileges, drops a helper called cache.exe, which leverages an open-source tool (ChromElevator) to extract credentials and data from Chromium-based browsers.
- stats_db.exe, used to collect data from messaging apps (Telegram, WhatsApp), cryptocurrency wallets and browser wallet extensions (Atomic, Exodus), and game platforms (Steam, Minecraft, GrowTopia, Epic Games Launcher).
- game_cache.exe, which establishes persistence by creating a Visual Basic startup script that runs on system boot, connects to the C2 to stream the victim’s screen, run arbitrary commands, transfer files, and change the desktop wallpaper.