Microsoft has issued a serious warning after confirming that a newly discovered zero-day vulnerability in the Windows Remote Access Connection Manager (RasMan) service is being actively exploited in real-world attacks. The flaw allows threat actors to gain SYSTEM-level privileges, giving them complete control over the targeted machine. This vulnerability, tracked as CVE-2025-59230, is considered a high-severity escalation flaw, putting both enterprise and government systems at risk.
Understanding the Vulnerability
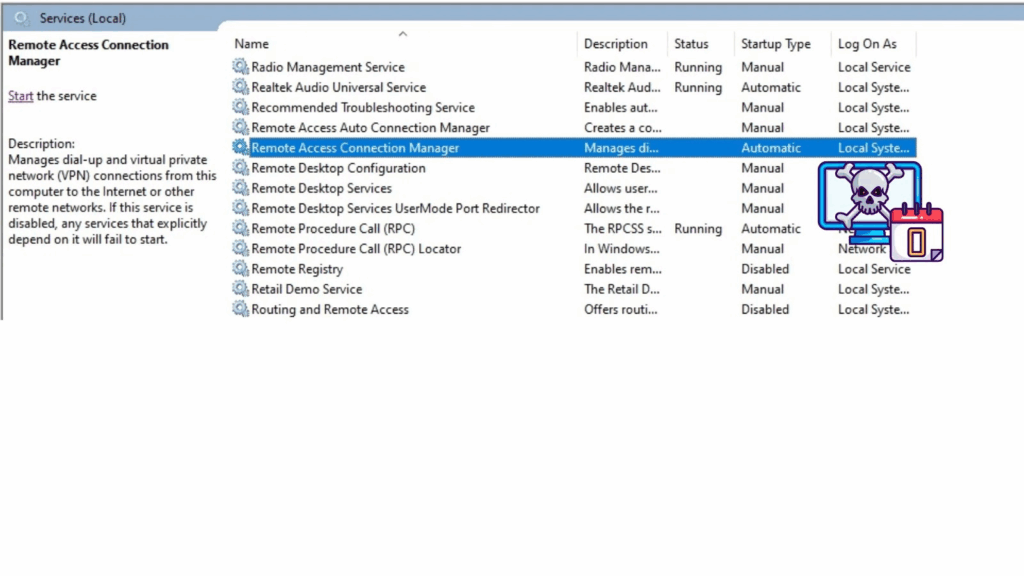
The issue lies within RasMan, a crucial Windows service responsible for managing remote access connections such as VPNs and dial-up networking. Due to improper access control, a user with limited privileges can exploit weak permission checks and manipulate RasMan configurations. This manipulation enables the attacker to bypass standard privilege boundaries and execute commands with elevated permissions.
Microsoft officially disclosed the vulnerability on October 14, 2025, noting that it affects multiple Windows versions, including Windows 10 (version 1809 and above), Windows 11, and Windows Server 2019 through 2025. The flaw has already gained attention from threat actors who are targeting enterprise infrastructures.
Severity and Exploitation
According to the Common Vulnerability Scoring System (CVSS) v3.1, the flaw has received a base score of 7.8, which classifies it as high severity. It requires local access and low privileges, making it particularly appealing for attackers who already have an initial foothold through methods such as phishing, social engineering, or unpatched software.
Key CVE-2025-59230 Metrics:
- Base Score: 7.8 (High)
- Attack Vector: Local (AV:L)
- Attack Complexity: Low (AC:L)
- Privileges Required: Low (PR:L)
- User Interaction: None (UI:N)
- Impact: High on Confidentiality, Integrity, and Availability
- Exploit Maturity: Functional (E:F)
This means an attacker only needs local access to exploit the weakness. Once exploited, the attacker can gain complete system control, modify configurations, or install malware capable of spreading laterally across a network.
Real-World Exploitation
Microsoft has classified the flaw as “Exploitation Detected”, confirming that active attacks are taking place. However, details about the attackers or specific victims remain undisclosed. Security researchers suggest that exploit techniques might include registry manipulation or DLL injection into the RasMan service.
For example, an attacker could overwrite accessible files located in the C:\Windows\System32\ras directory, replacing legitimate files with malicious DLLs. Upon restarting the RasMan service, the injected code executes with SYSTEM privileges, granting full access to system processes and data. Such exploitation could serve as a post-compromise escalation technique within larger cyberattacks or ransomware operations.
Potential Attack Scenarios
This zero-day vulnerability can be combined with other entry points to maximize damage. A common attack sequence could involve:
- Initial infection through phishing emails or malicious attachments.
- Establishing local access using a low-privileged account.
- Exploiting the RasMan flaw to elevate privileges to SYSTEM level.
- Deploying malware, ransomware, or backdoors for persistence.
- Conducting lateral movement across connected systems.
Mitigation and Microsoft Response
Microsoft recommends all organizations immediately apply the October 2025 Patch Tuesday updates, which include the fix for CVE-2025-59230. Unpatched systems are at significant risk, especially from nation-state attackers and ransomware operators who target Windows environments.
Administrators are also advised to:
- Restrict unnecessary local user access.
- Enable automatic updates.
- Monitor system logs for suspicious changes in RasMan activity.
- Use endpoint detection and response (EDR) tools for early detection.
While no public proof-of-concept (PoC) has been released yet, security experts warn that exploit attempts are already circulating in underground communities.