A new, persistent Android campaign, attributed to GhostBat RAT, impersonates Regional Transport Office, RTO, applications to steal banking data from Indian users. Attackers distribute malicious droppers through WhatsApp, SMS with shortened URLs, GitHub hosted APKs, and compromised websites, then use multi stage loading, ZIP header manipulation, native libraries, and extensive string obfuscation to avoid detection and analysis.
![Phishing activity implemented by the malware to steal UPI PIN]](https://sctocs.com/wp-content/uploads/2025/10/Figure-3-–-Phishing-activity-implemented-by-the-malware-to-steal-UPI-PIN-1024x559-1.webp)
How the campaign spreads
Threat actors use several infection vectors to maximize reach. Common delivery methods include WhatsApp image shares that contain shortened links, SMS messages with obfuscated URLs, direct hosting on GitHub for APKs, and poisoned or compromised web pages. Recipients who follow the links are urged to download an APK disguised as an official RTO app, often an imitation of the popular mParivahan application.
Once a dropper is launched, it requests SMS related permissions under the pretext of an app update, then proceeds with staged unpacking and payload activation. Device registration to the attacker infrastructure is handled via a Telegram bot named GhostBatRat_bot, which helps the campaign track and manage compromised devices.

Technical evasion and architecture
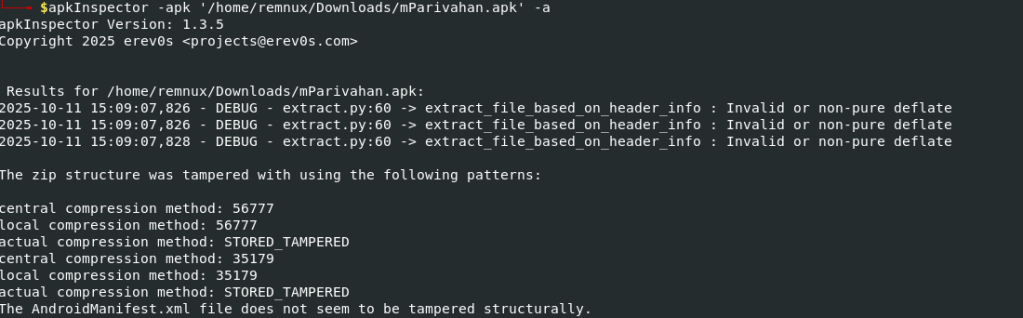
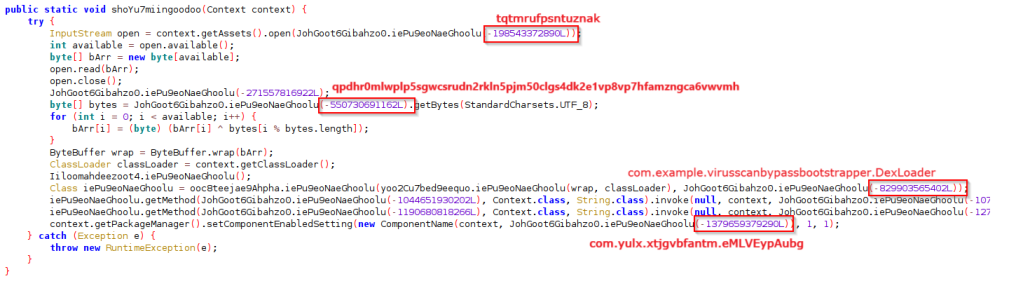
GhostBat RAT employs a layered, multi stage architecture designed to bypass static detection and sandbox analysis. Key technical traits include, first stage droppers that check device architecture and manufacturer, intentionally terminating on x86 or x86_64 to avoid analysis in emulated environments, deliberate corruption of ZIP headers to defeat signature scanners, and heavy string obfuscation where readable strings are replaced with long numeric sequences.
The dropper decrypts an embedded asset using XOR, loads it with DexClassLoader, then executes a second stage which itself decrypts another asset with an AES key derived from the SHA 1 hash of its filename. That decrypted content is placed into a classes.zip, which houses the third stage module. The final stage often fetches and executes a cryptominer library, then installs a malicious APK that performs credential theft.
Many variants include a native loader, a .so library that decrypts and loads additional native binaries using JNI calls like FindClass, resolving API names at runtime. This native component mirrors the three stage pattern, ultimately delivering both a banking credential stealer and a cryptocurrency miner.
Social engineering and phishing tactics
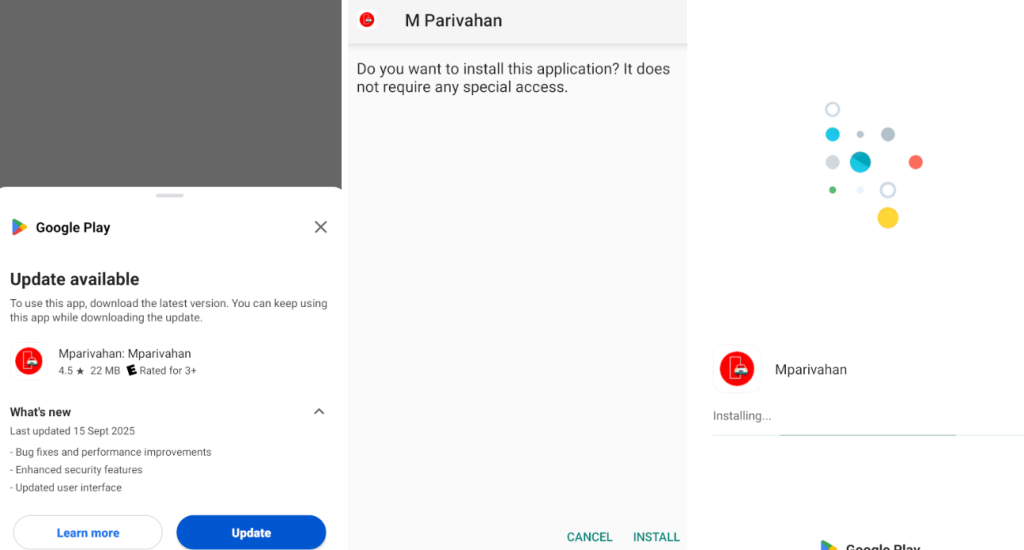
The malicious APK mimics legitimate UI flows to trick users. After the initial fake Google Play update prompt, users are asked to allow installations from unknown sources. The app then requests SMS permissions, presenting a convincing interface resembling mParivahan that asks for mobile numbers, vehicle details, and verification steps. Attackers also present a fake payment verification, requesting a nominal fee, for example ₹1, to “complete verification.” During this flow, users are prompted to enter their UPI PIN into a counterfeit input, which is then forwarded to a Firebase endpoint controlled by the attackers.
All SMS messages containing banking related keywords are filtered and exfiltrated to command and control servers, while incoming OTPs can be forwarded, uploaded, or intercepted for real time fraud. This dual approach, harvesting both static credentials and dynamic OTPs, enables unauthorized transactions and account takeovers.
[image import, Malicious application installation flow]
Operational timeline and samples
CRIL first documented RTO themed Android malware in July 2024 that targeted contacts and SMS messages. Renewed and expanded observations from September 2025 onward show over forty distinct samples spreading via WhatsApp and smishing campaigns, with variations in custom packers, anti emulation checks, and native packing strategies, yet all converging on a malicious mParivahan imitation.
VirusTotal and other scanners report low detection rates for many samples, due to the layered dropper design, header corruption, and runtime obfuscation.
Impact and mitigation
GhostBat RAT combines advanced technical evasion with convincing social engineering to target Indian banking users, especially those who rely on SMS and UPI flows. Key mitigation steps include, manage SMS permissions strictly, avoid installing apps from outside official app stores, be suspicious of shortened URLs and unexpected WhatsApp links, verify app authenticity through official channels, and disable installations from unknown sources unless absolutely necessary for trusted apps. Organizations and researchers should monitor Telegram bot infrastructure, GitHub hosted APK repositories, and smishing trends as part of ongoing mobile threat intelligence.


