A newly discovered malware campaign is spreading rapidly across Brazil, using WhatsApp as its main delivery channel. Cybersecurity experts have identified this advanced banking Trojan as “Maverick”, a threat capable of taking remote control of infected computers and stealing sensitive financial data.
Massive Scale of Infection
Researchers report that over 62,000 infection attempts were blocked in Brazil during just the first ten days of October, showing how widespread and dangerous this campaign has become.
The attack starts when victims receive a malicious ZIP file through WhatsApp messages. Inside the ZIP file is an LNK shortcut file disguised as a legitimate banking document. The filenames, written in Portuguese, make the file appear authentic and trustworthy.
Victims are typically instructed to open the file on a computer and ignore Chrome’s security warnings by choosing the “keep file” option, which leads directly to infection.
Self-Propagating Through WhatsApp
What makes this campaign exceptionally dangerous is its self-spreading capability. Once a system is infected, Maverick uses WPPConnect, an open-source WhatsApp automation framework, to hijack the victim’s account. It then automatically sends the same malicious ZIP file to the victim’s WhatsApp contacts via WhatsApp Web.
This worm-like behavior allows Maverick to spread exponentially, turning every infected user into a new distributor of the malware.
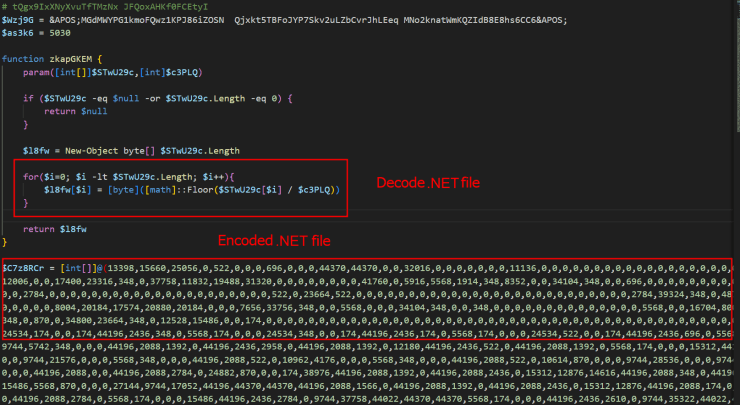
Advanced Fileless Infection Chain
Maverick’s infection process is highly advanced and mostly runs in memory, which makes it difficult for traditional antivirus tools to detect.
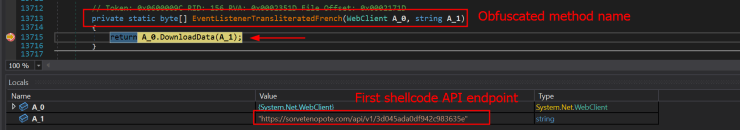
When the LNK file is executed, it runs a series of PowerShell scripts that download encrypted payloads from command-and-control (C2) servers. These scripts perform User-Agent validation to ensure that only genuine infected systems can fetch the payloads, preventing researchers from analyzing the malware easily.
The attack uses multiple modular components, including PowerShell, .NET assemblies, and Donut-encrypted shellcode, each loading the next stage until the final Maverick Trojan is deployed.
Before installing, the malware checks for Brazil-specific system configurations like language, timezone, and date format to ensure that only local users are targeted.
AI-Powered Capabilities and Banking Functions
Investigators found signs that artificial intelligence was involved in Maverick’s code development. In particular, AI appears to have been used to refine the malware’s certificate decryption routines and improve its overall modular structure.
Maverick communicates with its backend servers through API requests using a special key in the “X-Request-Headers” field of the HTTP header.
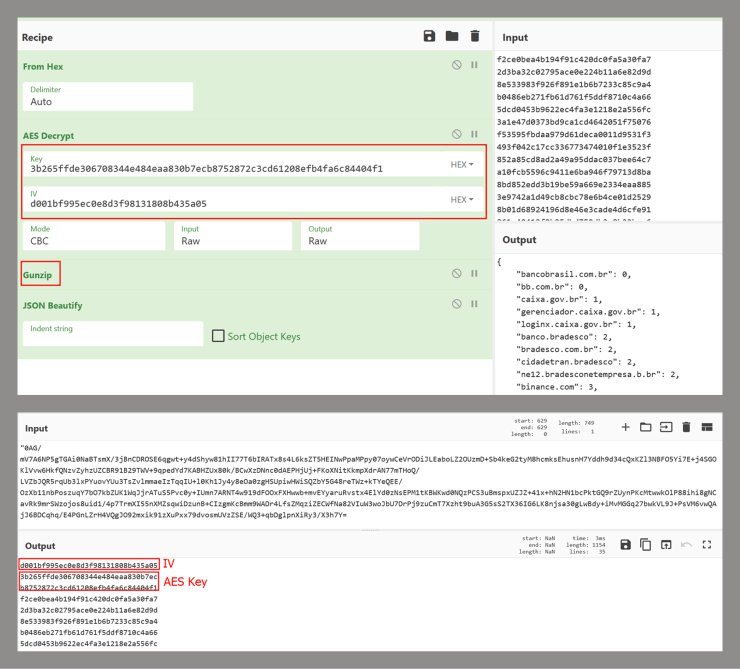
Once active, Maverick monitors victims’ activity on 26 Brazilian banking sites, six cryptocurrency exchanges, and one payment platform. It supports popular browsers including Google Chrome, Mozilla Firefox, Microsoft Edge, Brave, and Internet Explorer.
Its capabilities include:
- Capturing screenshots and keystrokes
- Controlling the mouse remotely
- Monitoring browsing activity
- Terminating processes
- Displaying overlay phishing pages when users visit online banking portals
Through these features, attackers can steal banking credentials, perform fraudulent transactions, and maintain full remote control of infected systems.
Connection to Previous Threats
Researchers have identified significant similarities between Maverick and an earlier Brazilian banking Trojan known as Coyote, first observed in early 2024.
Both Trojans use AES-256 encryption and share nearly identical communication protocols. However, structural differences in the code suggest Maverick could either be a heavily reworked version of Coyote or a new strain built with shared components.
Protection and Prevention Tips
This campaign marks a worrying milestone in cybercrime evolution, highlighting how AI is now being used to build more evasive and intelligent malware.
To stay protected:
- Do not open ZIP or LNK files received through WhatsApp or other messaging apps, even from known contacts.
- Use reliable antivirus software and keep it updated.
- Deploy security tools that can scan attachments in messaging and email platforms.
- Educate employees and users about phishing and file-based attacks.
- Brazilian banking users should verify any suspicious messages through official bank channels before taking any action.


