North Korean hackers linked to the Contagious Interview campaign are enhancing their malicious tools by merging two major malware families, BeaverTail and OtterCookie. This evolution, observed by Cisco Talos, shows that the group is actively upgrading its capabilities and refining its JavaScript-based attack methods.
Ongoing Campaign and New Findings
According to Cisco Talos, the recent activity by this North Korean threat cluster demonstrates how BeaverTail and OtterCookie are becoming more intertwined. The new version of OtterCookie includes a keylogging and screenshot module, marking a significant step forward in its surveillance features.
Cybersecurity analysts track this group under several aliases, including CL-STA-0240, DeceptiveDevelopment, DEV#POPPER, Famous Chollima, Gwisin Gang, PurpleBravo, Tenacious Pungsan, UNC5342, and Void Dokkaebi.
Meanwhile, Google Threat Intelligence Group (GTIG) and Mandiant have confirmed that the same actor is leveraging a stealthy approach called EtherHiding, which uses BNB Smart Chain (BSC) and Ethereum blockchains to host and deliver payloads. This technique transforms blockchain infrastructure into a resilient Command and Control (C2) network, making this the first known case of a nation-state actor adopting such a method previously seen in cybercrime operations.
The Contagious Interview Scheme
The Contagious Interview campaign began in late 2022 as a sophisticated fake job recruitment scam. Attackers posed as legitimate companies, targeting job seekers and tricking them into downloading information-stealing malware disguised as coding tests or technical assessments. The campaign led to widespread data and cryptocurrency theft.
Over time, the attackers have adapted their delivery tactics, recently using ClickFix-style social engineering to distribute new malware strains such as GolangGhost, PylangGhost, TsunamiKit, Tropidoor, and AkdoorTea. However, the central tools in these attacks remain BeaverTail, OtterCookie, and InvisibleFerret.
How BeaverTail and OtterCookie Work Together
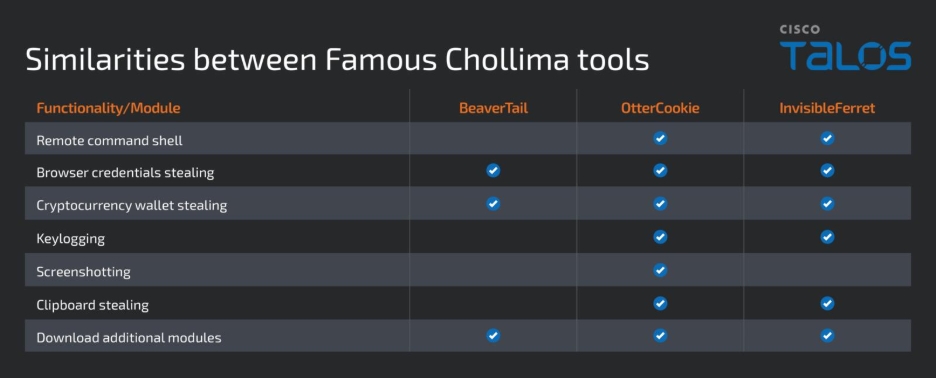
BeaverTail and OtterCookie are complementary malware families with distinct but overlapping roles. BeaverTail mainly functions as an information stealer and downloader, while earlier versions of OtterCookie acted as a command receiver that fetched and executed remote instructions.
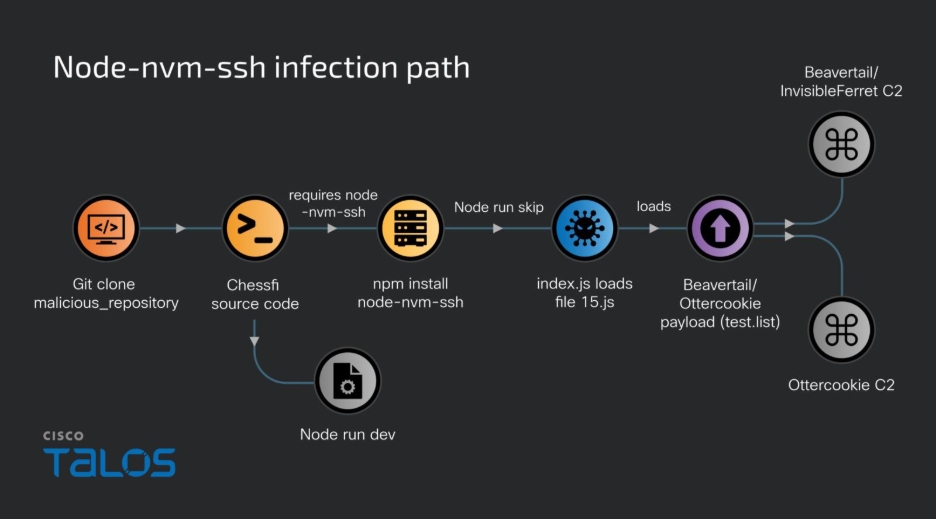
Cisco Talos identified the latest infection at a Sri Lankan organization, which was likely an unintentional target. The compromise occurred after a user installed a trojanized Node.js application named Chessfi from Bitbucket, believing it was part of a legitimate interview process.
Malicious npm Packages and Infection Chain
The malicious Chessfi package contained a dependency called node-nvm-ssh, published on August 20, 2025, by a user named “trailer” on the official npm repository. It recorded around 306 downloads before removal six days later.
This package was also among 338 malicious Node libraries identified by Socket as part of the Contagious Interview campaign. Once installed, it executed a postinstall hook that launched the main payload (index.js), which then triggered file15.js to deploy the final-stage malware.
Merged Features and New Modules
Cisco Talos researchers Vanja Svajcer and Michael Kelley discovered that the malicious code exhibited traits of both BeaverTail and OtterCookie, blurring their functional boundaries.
The updated version integrates a keylogger and screenshot module that uses legitimate npm packages like node-global-key-listener and screenshot-desktop to record keystrokes and capture screenshots. It can also monitor clipboard data and transmit the stolen information to its C2 server.
This version, known as OtterCookie v5, has evolved into a modular toolkit for data theft, remote command execution, and persistence. It includes BeaverTail-like features such as browser data extraction, cryptocurrency wallet theft, AnyDesk installation for remote access, and downloading of a Python backdoor called InvisibleFerret.
Additional Modules Identified
Some of the other modules embedded within OtterCookie v5 include:
- Remote Shell Module: Sends system and clipboard data to the C2 server, installs socket.io-client for two-way communication, and executes attacker commands.
- File Uploading Module: Scans all drives for specific file names (such as metamask, bitcoin, backup, and phrase) and uploads them to the C2 server.
- Crypto Extension Stealer Module: Extracts data from cryptocurrency wallet extensions on Google Chrome and Brave, overlapping with BeaverTail’s target list.
Experimentation and New Delivery Vectors
Cisco Talos also reported discovering a Qt-based BeaverTail artifact and a malicious Visual Studio Code extension that contained both BeaverTail and OtterCookie code. This finding suggests the hackers might be testing new delivery techniques for broader infections.
Researchers added that the Visual Studio Code extension could also be an experimental creation by another actor or researcher, as it does not fully align with the known behavior patterns of Famous Chollima.


