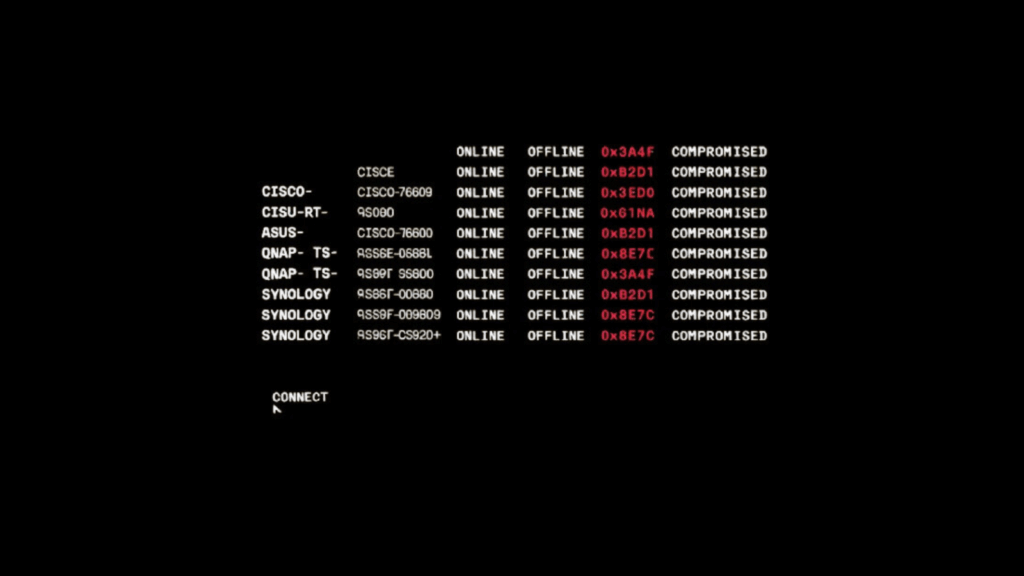
Cybersecurity researchers have uncovered the inner workings of a router-focused botnet called PolarEdge, which targets devices from Cisco, ASUS, QNAP, and Synology. First reported by Sekoia in February 2025, PolarEdge uses a TLS-based ELF implant to take control of vulnerable routers and expose them to remote commands, creating a network of compromised devices for purposes that remain unclear.

How PolarEdge Infects Devices
In attacks observed in February 2025, threat actors exploited a known Cisco vulnerability, CVE-2023-20118, to fetch a shell script named “q” via FTP. That script then downloads and launches the PolarEdge backdoor on the compromised router. The implant, implemented as an ELF binary, embeds its configuration in the final 512 bytes of the image, obfuscated by a single-byte XOR using key 0x11, which allows operators to hide settings inside the binary image.
Architecture and Operation Modes
PolarEdge uses TLS for communication and implements its TLS routines with mbedTLS v2.8.0. The backdoor supports two modes, connect-back and debug. In connect-back mode, it acts as a TLS client to retrieve files from a remote host. In debug mode, it offers an interactive interface to modify configuration values, such as server addresses. By default, the implant runs as a TLS server, sending a host fingerprint to its command-and-control server and then waiting for commands over a custom binary protocol. One protocol parameter, named HasCommand, controls whether a received packet contains an executable instruction. If HasCommand equals ASCII 1, the backdoor extracts the Command field, runs the command, and returns raw output to the C2 server.
Anti-analysis and Evasion Techniques
The malware includes several anti-analysis measures to hinder detection and reverse engineering. It obfuscates TLS setup and fingerprinting logic, and it uses process masquerading during startup by randomly selecting a name from a predefined list, including igmpproxy, wscd, /sbin/dhcpd, httpd, upnpd, and iapp. PolarEdge does not fully persist across reboots, however it uses a parent-child watchdog mechanism, where a spawned child process checks every 30 seconds whether the parent is still running, and if not, the child relaunches the backdoor.
Post-infection Behavior
Once running, PolarEdge removes or moves certain system utilities such as /usr/bin/wget and /sbin/curl, and it deletes specific files on infected devices, for example /share/CACHEDEV1_DATA/.qpkg/CMS-WS/cgi-bin/library.cgi.bak. The exact reasoning for these file operations is not fully explained by researchers, but they may be intended to hide traces or to disrupt other services on the device.
Infrastructure and Historical Context
Censys, in an August 2025 analysis, linked much of PolarEdge’s infrastructure to patterns typical of Operational Relay Box, ORB, networks, suggesting a structured relay system behind the botnet. There is also evidence indicating activity tied to this campaign may date back to June 2023, implying a long-running, evolving operation.
Related Threats, Monetization and Ecosystem
Researchers have noted a related trend in which compromised devices are monetized as residential SOCKS5 proxies. Synthient recently profiled GhostSocks, a service-first advertised in October 2023, which converts infected endpoints into SOCKS5 proxies, and which was integrated into Lumma Stealer in early 2024. GhostSocks provisions clients with configuration files, or falls back to hard-coded configs, to spawn proxy sessions using go-socks5 and yamux libraries. This model shows how device compromise can be turned into revenue for threat actors, and it illustrates the broader ecosystem into which PolarEdge could feed.