Cybersecurity experts have identified a high-severity security flaw in the async-tar Rust library and its related forks, including tokio-tar, which could enable remote code execution (RCE) in certain conditions.
Tracked as CVE-2025-62518 with a CVSS score of 8.1, the flaw, codenamed “TARmageddon” by Edera, was discovered in August 2025. It affects several widely used Rust-based projects such as testcontainers and wasmCloud.
According to Edera, “In the worst-case scenario, this bug could allow remote code execution through file overwriting attacks, including replacing configuration files or hijacking build backends.”
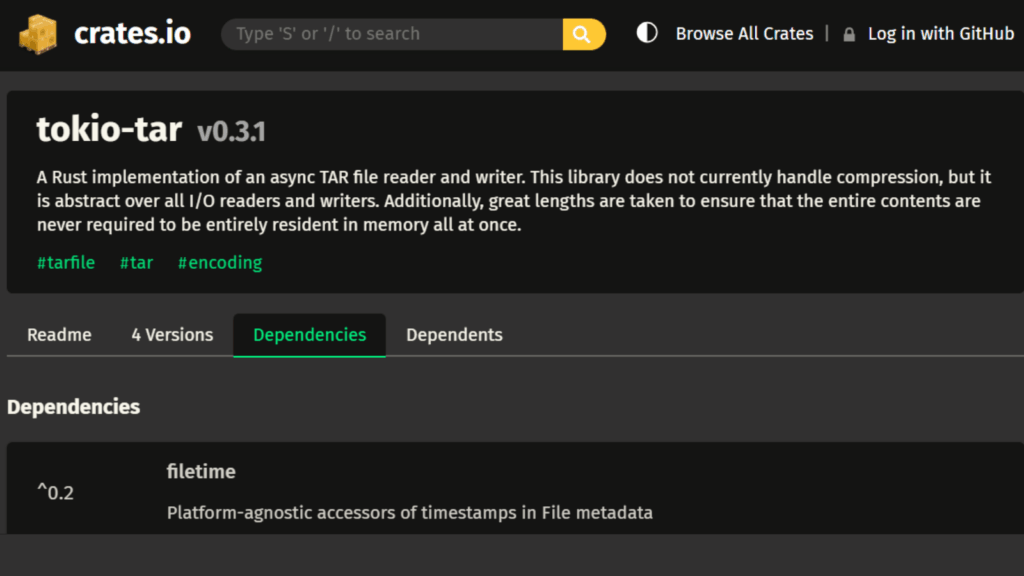
The risk increases because tokio-tar is considered abandonware, despite its popularity and thousands of downloads from crates.io. This Rust library enables asynchronous reading and writing of TAR archives using the Tokio runtime. It has not received any updates since July 15, 2023.
Due to the lack of patches for tokio-tar, users are urged to migrate to astral-tokio-tar, which released version 0.5.6 to fix the issue.
Astral developer William Woodruff explained, “Versions prior to 0.5.6 contain a boundary parsing flaw that lets attackers smuggle additional archive entries by exploiting inconsistent handling of PAX and USTAR headers.”
When archives contain PAX-extended headers with size overrides, the parser incorrectly moves the data stream based on the USTAR header size (often zero) instead of the PAX-specified size. This misstep makes the parser treat file content as legitimate TAR headers.
In simpler terms, this happens because of inconsistent handling of PAX and USTAR headers when calculating file data boundaries. PAX (Portable Archive Interchange) is an extended version of the USTAR format used to define extra file properties inside TAR archives.
When a PAX header correctly specifies file size but a USTAR header incorrectly marks it as zero, the parser becomes confused and processes inner TAR content as outer TAR entries.
Edera noted, “Because the parser advances by zero bytes, it fails to skip over the actual file data (a nested TAR archive) and encounters the next TAR header at the start of the nested archive, treating it as a valid entry.”
This flaw allows attackers to “smuggle” malicious TAR files within another TAR archive, potentially overwriting files in extraction directories and leading to arbitrary code execution.
In a practical attack, a threat actor could upload a malicious PyPI package where the outer TAR contains a legitimate pyproject.toml file, while a hidden inner TAR includes a malicious one. When installed, it could replace the genuine file and hijack the build backend.
Edera emphasized, “Although Rust prevents memory corruption issues like buffer overflows or use-after-free bugs, logic flaws such as this parsing error still pose a serious threat. Developers must remain cautious of every class of vulnerability, regardless of programming language.”