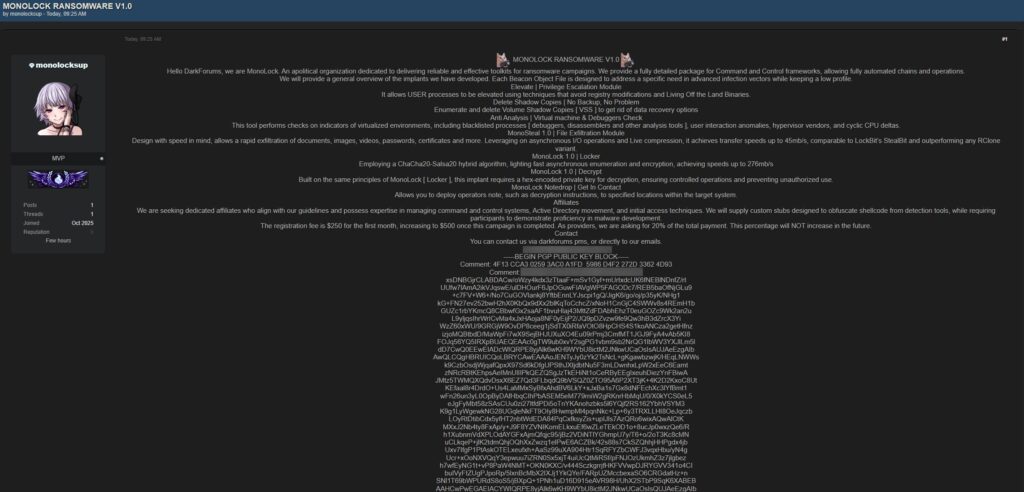
Monolock ransomware has appeared for sale on underground forums, with operators advertising version 1.0 and offering stolen corporate credentials alongside the malware. First observed in late September, the campaign spreads through phishing messages that deliver malicious Microsoft Word documents, which, when opened, trigger an embedded macro to download the ransomware binary from a compromised host.
Threat overview
Researchers and victims report that Monolock encrypts files using AES-256 for file payloads, while using RSA-2048 for key exchange, making recovery impossible without the private key. Early deployments targeted small to mid-sized organizations in healthcare and manufacturing, according to Dark Web Informer analysts. The operators demand payment in cryptocurrency, directing victims to a Tor-hosted payment portal that automatically verifies payment and provides the decryption key. The ransom note included with early samples offers a 10 percent discount if payment is made within 48 hours.
Infection chain and behavior
The infection begins with a phishing Word document, the embedded macro downloads the ransomware executable from a compromised server, and execution follows. In sandboxed analyses, Monolock was observed terminating processes tied to backup and security software before starting encryption, to prevent snapshot or backup-based recovery. The malware scans running services and processes for strings that match terms like “backup”, “sql”, and “vss”, then kills matching processes.
Once encryption completes, Monolock appends the extension “.monolock” to affected files, and places a ransom note named “README_RECOVER.txt” in each folder.
Persistence and evasion techniques
For persistence, Monolock adds an entry under the Windows Run registry key so the malware executes at boot. The binary masquerades as a legitimate DLL, and performs code injection into explorer.exe to reduce the chance of detection. The sample also uses API hashing to look up Windows functions at runtime, avoiding explicit imports by name and complicating static signature detection.
A representative snippet of the API-hashing routine is shown below, demonstrating the rotate-xor style used to compute function hashes, (note commas used in place of other punctuation):
DWORD hash = 0xA1B2C3D4;
for (char* p = moduleName; *p; ++p) {
hash = ((hash << 7) | (hash >> (32 - 7))) ^ *p;
}By resolving functions from hashes, Monolock reduces readable import table artifacts, which hinders many endpoint detection tools. These techniques emphasize the need for behavior-based and telemetry-driven detection.
Impact and sectors targeted
Initial activity disproportionately affected healthcare and manufacturing small to mid-sized organizations, where downtime and disrupted operations can produce urgent pressure to pay. The combination of backup termination, process killing, and strong cryptography increases the operational impact and recovery complexity for victims.
Recommendations for defenders
1, Maintain offline, immutable backups, and verify backups regularly, so snapshot or backup deletion does not prevent recovery.
2, Enforce email security controls, including macro blocking for incoming Office documents, attachment sandboxing, and user training against phishing, to reduce initial infection rates.
3, Deploy behavior-based EDR and endpoint telemetry collection, to detect suspicious process injection, API hashing patterns, and mass file encryption activities.
4, Monitor for registry Run key changes and suspicious DLLs that claim to be legitimate, as these are common persistence techniques.
5, Implement network segmentation and least privilege for services such as SQL and backup systems, to reduce lateral movement and process discovery.
6, If infected, preserve memory and disk images for incident response, do not immediately reboot or power off systems unless instructed by responders, and consult experienced incident response teams.