A major ongoing smishing campaign has been traced to over 194,000 malicious domains since January 1, 2024, targeting a wide variety of services around the world, according to recent research from Palo Alto Networks Unit 42.
Although many of these domains are registered through a Hong Kong-based registrar and utilize Chinese nameservers, the bulk of the attack infrastructure is hosted on popular U.S. cloud platforms, noted security researchers Reethika Ramesh, Zhanhao Chen, Daiping Liu, Chi-Wei Liu, Shehroze Farooqi, and Moe Ghasemisharif said.
The group behind this activity, known as the China-linked Smishing Triad, primarily floods mobile devices with fake toll violation notices and package misdelivery alerts to trick users into divulging sensitive information quickly.
This illicit operation has proven extremely profitable, reportedly generating over $1 billion in revenue over the past three years, according to The Wall Street Journal.
Recent findings from Fortra indicate that the Smishing Triad’s phishing kits are increasingly used to target brokerage accounts, stealing banking credentials and authentication codes. Attacks on these accounts surged fivefold in Q2 2025 compared to the same period last year.
“Once compromised, attackers can manipulate stock prices using ramp-and-dump schemes,” explained security expert Alexis Ober. “These tactics leave almost no paper trail, increasing financial risks significantly.”
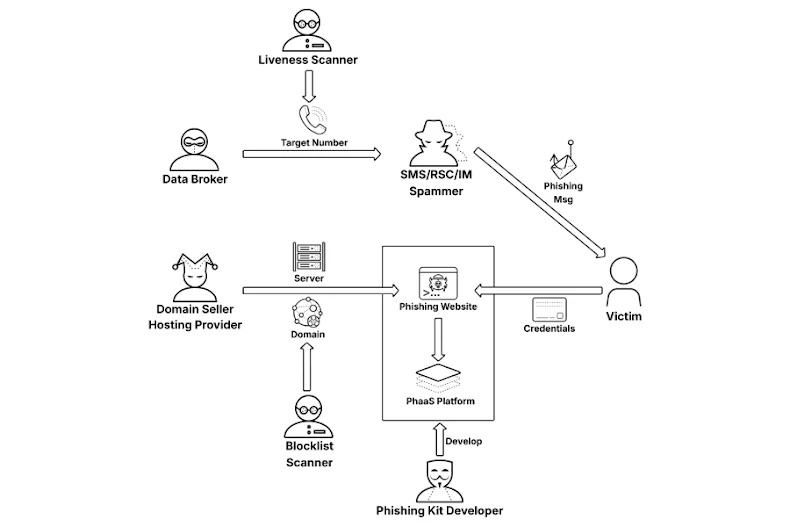
The Smishing Triad has evolved from a simple phishing kit provider into a highly active network, connecting multiple threat actors in the phishing-as-a-service (PhaaS) ecosystem. This ecosystem involves phishing kit developers, data brokers selling phone numbers, domain sellers registering disposable domains, hosting providers, spammers, liveness scanners, and blocklist scanners.
Unit 42’s research shows that nearly 93,200 of the 136,933 root domains (68.06%) are registered under Dominet (HK) Limited, based in Hong Kong. Most domains use the “com” extension, but registrations of “gov” domains have risen in the last three months.
Short-lived domains dominate this campaign: 39,964 (29.19%) were active for just two days or less, 71.3% for less than a week, 82.6% for under two weeks, and under 6% lasted beyond three months.
“This high domain turnover illustrates the campaign’s strategy of using continuously new domains to evade detection,” the researchers noted. Overall, 194,345 fully qualified domain names (FQDNs) resolve to 43,494 unique IP addresses, most of which are located in the U.S. and hosted on Cloudflare (AS13335).
Key infrastructure highlights include:
- USPS is the most impersonated service with 28,045 FQDNs.
- Toll service phishing campaigns account for roughly 90,000 FQDNs.
- The highest-traffic domains are hosted mainly in the U.S., followed by China and Singapore.
- Other targeted services include banks, cryptocurrency exchanges, delivery companies, law enforcement, state-owned enterprises, electronic toll systems, carpooling apps, hospitality services, social media, and e-commerce platforms across Russia, Poland, and Lithuania.
- Government impersonation campaigns often redirect users to pages claiming unpaid tolls or service fees, sometimes using ClickFix lures to trick them into running malicious code under the guise of CAPTCHA completion.
“Smishing campaigns impersonating U.S. toll services are part of a global, decentralized effort targeting multiple sectors,” Unit 42 concluded. “Threat actors register and rotate thousands of domains daily to stay ahead of detection.”


