In a significant demonstration of its proactive security measures, Google has announced that its built-in scam defenses on the Android platform are now protecting users from over 10 billion suspected malicious calls and messages every single month. This massive filtering effort is powered by on-device artificial intelligence, creating a formidable barrier against modern digital fraud.
Proactive Blocks and Smarter Filtering
The tech giant revealed that it has preemptively blocked more than 100 million suspicious phone numbers from using Rich Communication Services (RCS), the next-generation SMS protocol. This action stops potential scams at the source before they can even reach a user’s inbox.
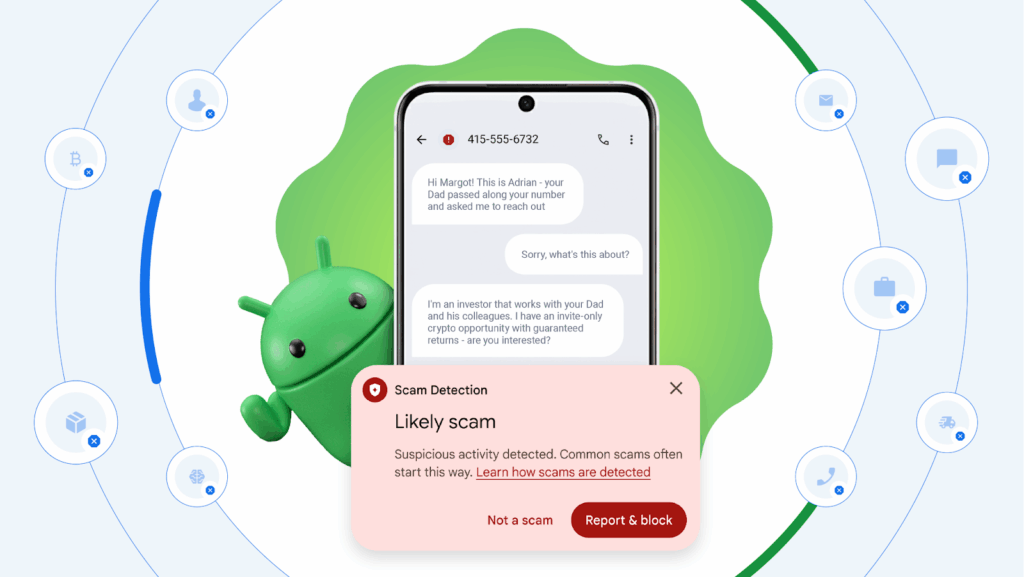
For years, Google has integrated sophisticated safeguards into Android to automatically identify and filter known spam. Using on-device AI, the system analyzes calls and messages, seamlessly moving those flagged as spam into a dedicated “spam & blocked” folder within the Google Messages app.
Adding another layer of protection, Google recently rolled out a global “safer links” feature. This service proactively warns users if they attempt to click on a URL within a message that has been flagged as spam, effectively preventing visits to potentially harmful websites unless the user manually marks the message as “not spam.”
The Anatomy of Modern Scams: From Employment Fraud to Group Chats
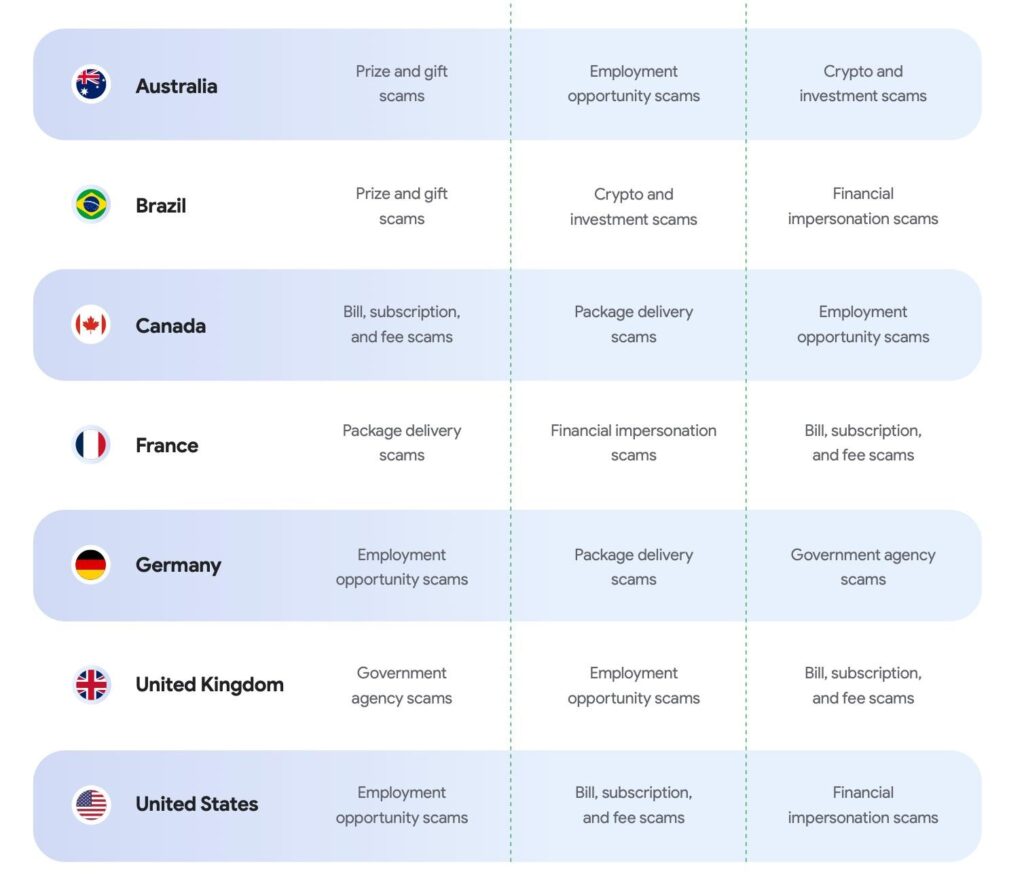
Google’s analysis of user-submitted reports from August 2025 pinpointed the most common scam categories:
- Employment Fraud: The most prevalent tactic, luring job seekers with fake opportunities to steal their personal and financial information.
- Financial Scams: These include bogus alerts about unpaid bills, subscriptions, fees, and fraudulent investment schemes.
- Other Prevalent Scams: Package delivery scams, government agency impersonation, romance scams, and fake technical support also feature prominently.
An emerging and interesting trend is the shift from direct messages to group chats. Scammers are now initiating conversations with multiple potential victims in a single group.
“This shift may have happened because group messages can feel less suspicious to recipients,” Google explained. “This is especially true when a scammer includes a fellow accomplice in the group to validate the initial message, making the entire exchange appear to be a legitimate conversation.”
The Scammer’s Playbook: Timing and Psychological Tactics
The research uncovered a distinct pattern in the timing of these malicious messages. Activity typically begins around 5 a.m. PT in the U.S., peaking between 8 a.m. and 10 a.m. PT. The highest volume of fraudulent messages is sent on Mondays, strategically coinciding with the start of the workweek when people are busiest and potentially less vigilant about incoming messages.
Scammers primarily employ two psychological frameworks:
1. Spray and Pray
This is a high-volume, low-effort approach. Scammers cast a wide net, hoping to ensnare a small fraction of victims. They create a false sense of urgency using lures related to topical events, package deliveries, or toll charges. The goal is to rush targets into clicking malicious links—often shortened to mask the dangerous destination—without thinking.
2. Bait and Wait
This is a more calculated and patient method involving personalized targeting. The threat actor invests time in building rapport with a target before executing the scam. Romance baiting (also known as “pig butchering”) is a classic example of this category.
“The scammer engages you in a longer conversation, pretending to be a recruiter or an old friend,” Google stated. “They may even use personal details gathered from public websites, like your name or job title, all designed to build trust. The tactics are more patient, aiming to maximize financial loss over time.”
The Vast Criminal Ecosystem Supporting Scams
Behind these messages lies a sophisticated criminal infrastructure. The operation is supported by:
- Hardware Suppliers: Providers of phone and SIM farms used to send smishing messages at scale.
- Phishing-as-a-Service (PhaaS) Kits: Turnkey solutions that offer credential-harvesting websites and campaign management tools.
- Bulk Messaging Services: The distribution engine that delivers malicious links to end victims.
Google described the scam landscape as highly volatile, with fraudsters constantly pivoting to regions with the least enforcement. “While it may appear that waves of scams are moving between countries, this constant churn doesn’t mean scammers are physically relocating,” the company added. “Once enforcement tightens in one area, they simply pivot to another, creating a perpetual cycle of shifting hotspots.”


