A critical security vulnerability in Samsung Galaxy Android devices was exploited as a zero-day to deploy a sophisticated commercial-grade spyware known as LANDFALL. The targeted attacks, focused in the Middle East, used a specially crafted image file sent through WhatsApp to compromise devices without any user interaction.
The Exploited Vulnerability and Its Patch
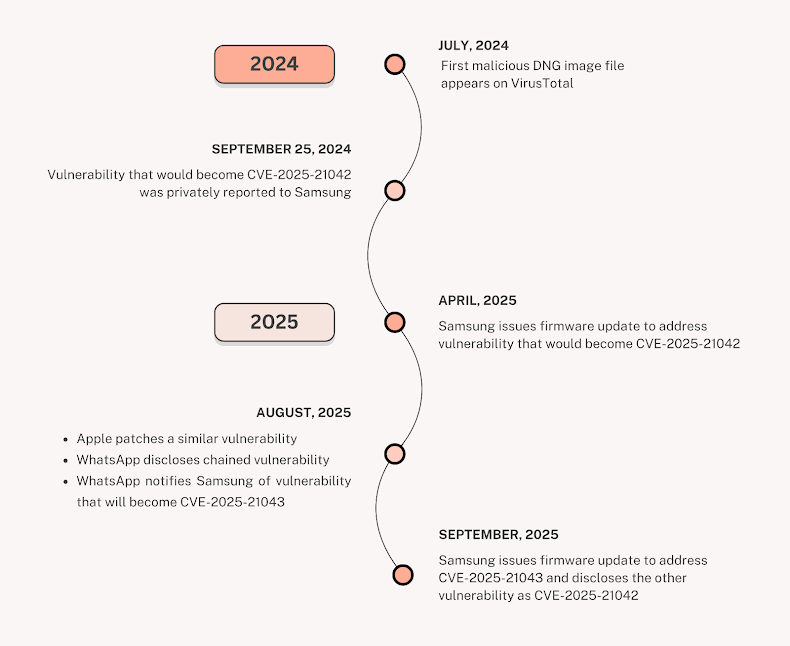
The flaw, identified as CVE-2025-21042 (CVSS score: 8.8), is an out-of-bounds write issue within a Samsung library (libimagecodec.quram.so). This vulnerability allowed remote attackers to execute arbitrary code on the target device. Samsung patched this critical flaw in April 2025 after receiving reports of active exploitation in the wild.
According to Palo Alto Networks Unit 42, which tracks this activity as CL-UNK-1054, the primary targets were located in Iraq, Iran, Turkey, and Morocco. This incident follows Samsung’s September 2025 disclosure that a separate flaw in the same library (CVE-2025-21043) was also exploited as a zero-day, though it was not part of the LANDFALL campaign.
The Zero-Click WhatsApp Delivery Mechanism
The attacks leveraged a zero-click approach, meaning the exploit required no interaction from the victim—not even opening the image. The malicious payload was hidden within DNG (Digital Negative) image files transmitted via WhatsApp.
Evidence from analyzed samples points to the campaign’s longevity, with artifacts dating back to July 23, 2024. File names such as “WhatsApp Image 2025-02-10 at 4.54.17 PM.jpeg” were used to appear legitimate and avoid suspicion.
LANDFALL Spyware: Capabilities and Persistence
Once the exploit was triggered, the LANDFALL spyware was installed, transforming the device into a powerful surveillance tool. Its capabilities are extensive and include:
- Recording audio from the microphone
- Tracking real-time location
- Stealing photos, contacts, SMS messages, and call logs
- Exfiltrating files from the device
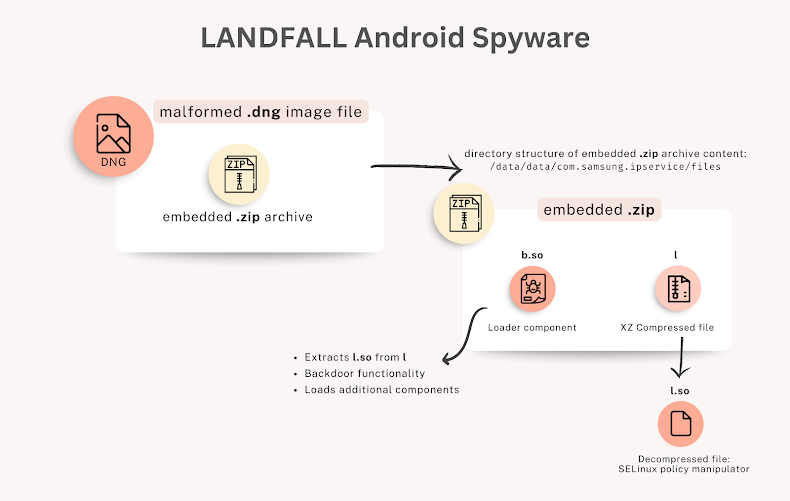
Unit 42’s technical analysis revealed that the malicious DNG files contained an embedded ZIP archive. The exploit code extracts a shared object library from this archive to run the spyware. A second shared object library is also deployed to manipulate the device’s SELinux policy, granting LANDFALL elevated permissions and ensuring it persists on the device even after a reboot.
Command-and-Control and Attribution
The spyware establishes communication with a remote command-and-control (C2) server over HTTPS. It enters a beaconing loop, periodically checking in with the server to receive commands and potentially download additional, more powerful payloads.
While the exact actor behind the campaign remains unknown, Unit 42 noted that the C2 infrastructure and domain registration patterns show similarities with those used by the Stealth Falcon (FruityArmor) threat group. However, as of October 2025, no direct technical overlaps have been confirmed to establish a definitive link.


