A new Browser Security Report 2025 reveals a fundamental shift in the corporate threat landscape. The user’s browser has become the central hub where identity, SaaS, and AI-related risks converge. Traditional security tools, operating at a lower level, are failing to protect this new, parallel attack surface where unmanaged extensions, personal AI accounts, and stolen sessions create unprecedented vulnerabilities.
GenAI Emerges as the Top Data Exfiltration Channel
The widespread adoption of Generative AI has opened a massive governance gap. With nearly half of all employees using AI tools, most do so through personal accounts, completely outside the visibility of IT departments.
Key statistics from the report paint a stark picture:
- 82% of these actions originate from personal, unmanaged accounts.
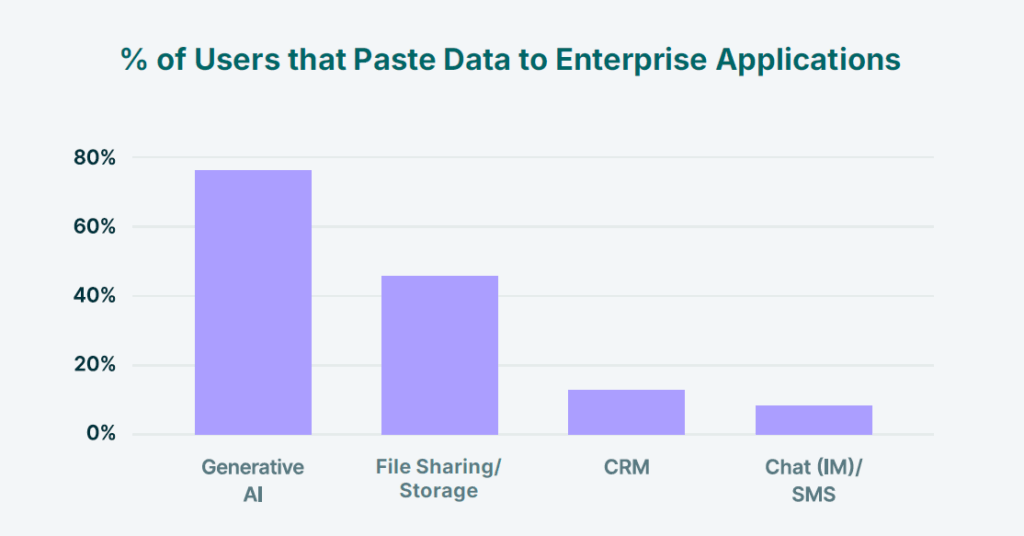
- 77% of employees paste corporate data directly into GenAI prompts.
- 40% of files uploaded to AI tools contain sensitive PII or PCI data.
- GenAI now accounts for nearly one-third of all corporate-to-personal data movement.
Legacy Data Loss Prevention (DLP) tools are ineffective here, as the browser has become the dominant, unmonitored channel for this new form of copy/paste exfiltration.
AI Browsers: The New Unmanaged Attack Surface
The rise of ‘agentic’ AI browsers like OpenAI’s Atlas and Arc Search is creating a novel threat vector. These tools merge search, chat, and browsing, using integrated LLMs to read and process everything in a user’s tabs in real-time.

While boosting productivity, they act as an “always-on co-pilot” with no enterprise guardrails. The risks are significant:
- Session Memory Leakage: AI personalization can expose sensitive data.
- Invisible Auto-Prompting: Page content is silently sent to third-party AI models.
- Blurred Identity Boundaries: Shared cookies can lead to session hijacking.
This new surface effectively bypasses traditional DLP, SSE, and browser security tools, creating an invisible path for data loss.
Browser Extensions: An Unmanaged Supply Chain Inside Your Endpoints
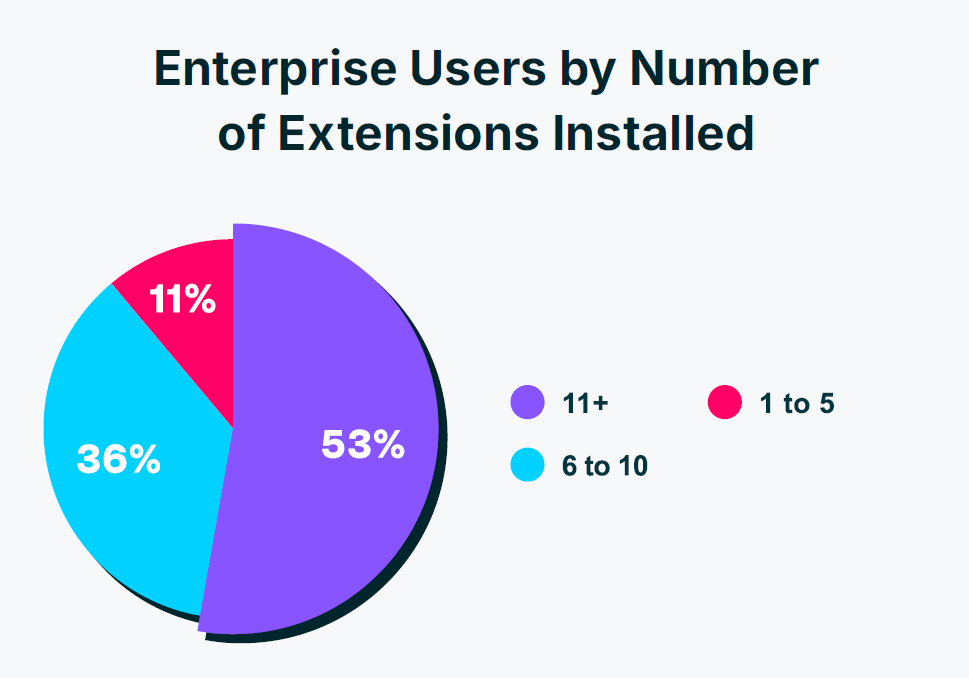
Browser extensions represent the most widespread and least governed software supply chain in the enterprise. A staggering 99% of users have at least one installed, often with high-level permissions and no oversight.
Report telemetry reveals critical issues:
- 54% are published by unverified Gmail accounts.
- 51% have not received a security update in over a year.
- 26% of extensions are sideloaded, bypassing official stores.
- 6% of GenAI-related extensions are outright malicious.
This is no longer just about productivity; it is an unmanaged software supply chain embedded directly into every corporate endpoint.
Identity Governance That Ends Where the Risk Begins
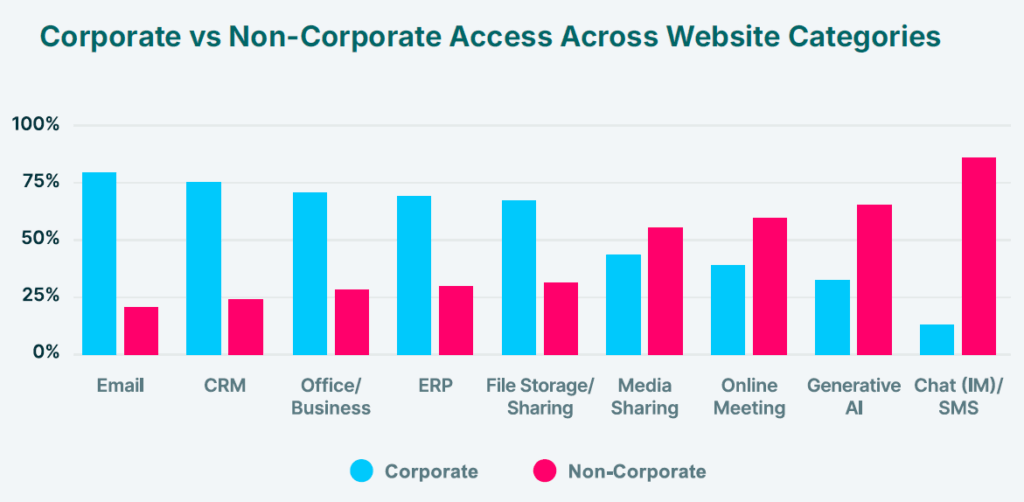
The report finds that identity governance often stops at the Identity Provider (IdP), but the real risk starts in the browser. Over two-thirds of corporate logins occur outside of Single Sign-On (SSO), creating a massive visibility gap.
The breakdown is alarming:
- 68% of corporate logins do not use SSO.
- 43% of SaaS application logins use personal credentials.
- 26% of users reuse passwords across multiple accounts.
- 8% of browser extensions have access to user identities and cookies.
As attacks like Scattered Spider have shown, browser session tokens are now the primary target for attackers, not passwords.
The Inadequacy of Traditional Security Tools
Endpoint Detection and Response (EDR), Secure Service Edge (SSE), and legacy DLP operate at the wrong layer. They see processes, network traffic, and files, but they are blind to the critical session-level activity inside the browser.
Security teams lack visibility into:
- Shadow AI usage and prompt inputs.
- Malicious extension activity and code injections.
- Data crossover between personal and corporate accounts.
- Real-time session hijacking and cookie theft.
This fundamental gap is why a new approach is urgently needed.
Download the full report to see what traditional controls are missing, and what top CISOs are doing next.


