A widespread phishing operation is targeting the hospitality sector, tricking hotel staff and guests into revealing sensitive credentials and payment data. The campaign uses compromised email accounts to impersonate legitimate booking platforms, then redirects victims to ClickFix-style pages that ultimately deliver PureRAT, a modular remote access trojan. Security firms link the activity to attacks active since at least April 2025, and ongoing through early October 2025.
How the scheme works
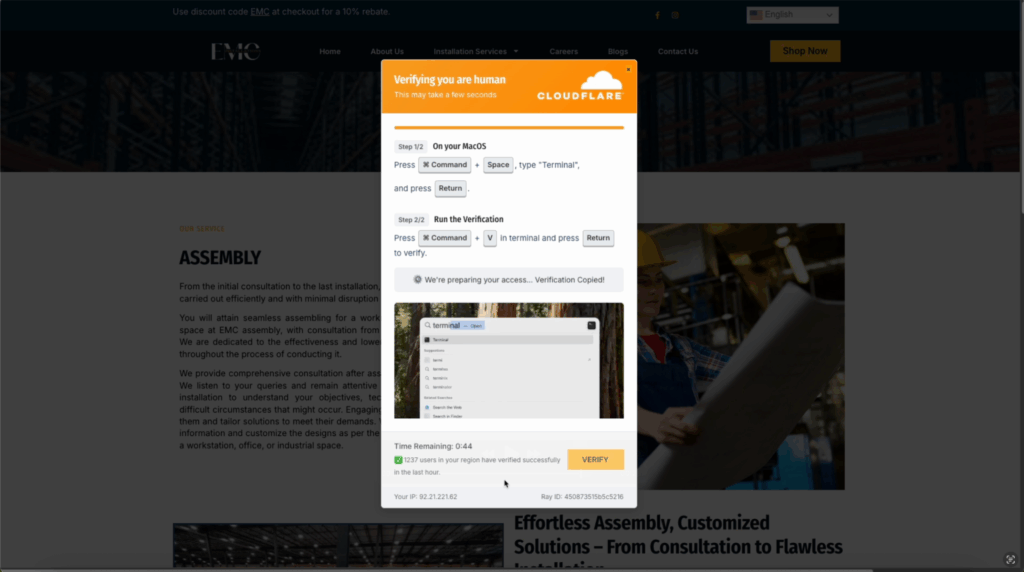
Threat actors begin by compromising an email account, which they use to send tailored phishing messages to multiple hotels. These messages spoof familiar services like Booking.com, and include links that lead to a redirection chain ending on a ClickFix-like landing page. The page presents a fake reCAPTCHA or verification prompt to convince the user that a short, manual step is required to secure their session.
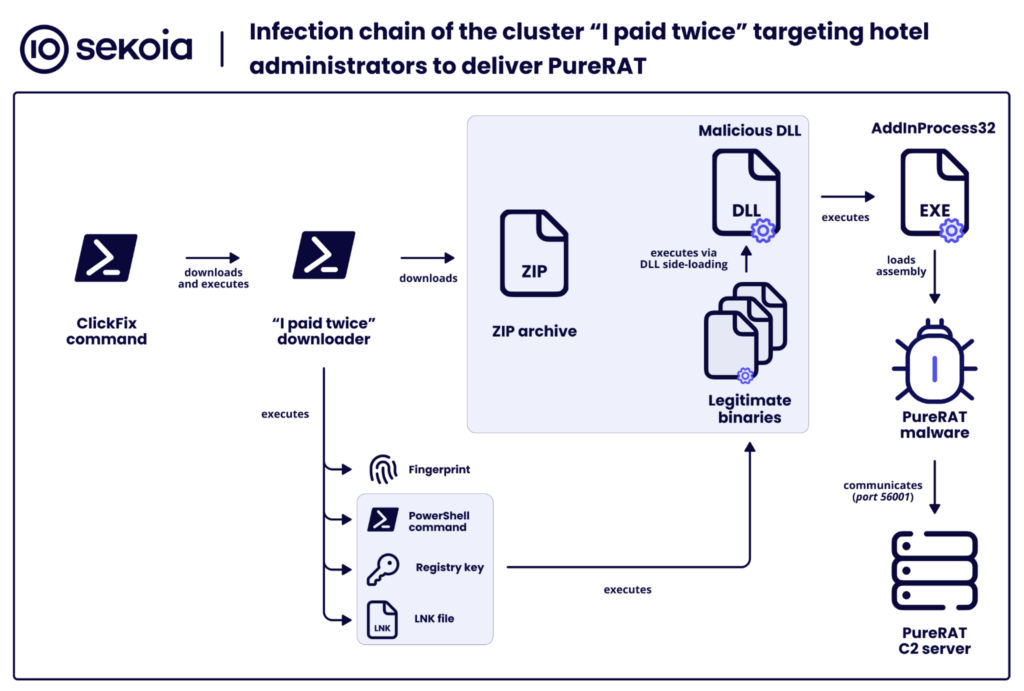
Upon landing, the page runs JavaScript that, after a delay, checks whether it is embedded in an iframe, then forces a redirection to the same address over HTTP. That change is used to prompt the victim to copy and run a PowerShell command, which collects system details and downloads a ZIP archive. The archive contains a binary that achieves persistence and side-loads PureRAT via a vulnerable DLL.
The attackers use this access to harvest Booking.com, Expedia and other booking platform credentials, then monetize them, either by selling account details on underground markets, or by sending fraudulent messages to hotel guests to carry out payment or refund scams.
Capabilities of PureRAT and persistence techniques
PureRAT, also known as zgRAT, is a feature rich backdoor. It can capture webcam and microphone streams, log keystrokes, control mouse and keyboard, upload and download files, proxy traffic, exfiltrate data, and run commands or additional payloads. The malware is protected with .NET Reactor to hinder analysis, and uses Windows Run registry keys for persistence. Attackers often deploy it through DLL side-loading to evade straightforward detection.
Social engineering against guests and staff
Beyond compromising hotel administrators, operators of this campaign have also reached customers directly via WhatsApp and email. Messages contain legitimate looking reservation details and ask recipients to follow a verification link to confirm their card information, supposedly to avoid cancellation. Those who follow the instructions land on counterfeit Booking.com or Expedia pages that capture payment credentials.
The attackers are understood to acquire lists of hotel administrators from criminal marketplaces, including forums like LolzTeam, sometimes offering affiliates a share of the illicit profits. Malware distribution is often outsourced to specialist traffers who specialize in delivery and infection.
The underground ecosystem supporting the fraud
Researchers observed a mature cybercrime ecosystem supporting each phase of the attack chain, including Telegram bots and accounts advertising bulk Booking logs, as well as inexpensive log checker tools that confirm account validity through proxy-based authentication. These services follow an as-a-service model, lowering the barrier to entry and streamlining monetization for criminals.
Evolving ClickFix tactics and new tricks
Security teams note ClickFix pages are becoming more convincing. Recent updates add embedded videos, countdown timers, and counters that display “users verified in the last hour” to increase legitimacy. The pages can tailor instructions to the visitor’s operating system, guiding Windows users to the Run dialog and macOS users to Terminal. Clipboard hijacking is also used to automatically place malicious commands on the victim’s clipboard, simplifying execution.


