GootLoader has reemerged, showing fresh innovations in evasion and delivery. Recent investigations by Huntress found multiple infections since October 27, 2025, including rapid hands-on-keyboard intrusions that led to domain controller compromise within 17 hours in two cases. The loader now uses custom web fonts and other subtle tricks to hide malicious payloads on compromised WordPress sites, while continuing to serve as a gateway for backdoors and ransomware.
Attack overview and distribution methods
Operators tied to GootLoader, associated with a group tracked as Hive0127 [aka UNC2565], rely on search engine abuse to steer victims toward compromised WordPress pages. Earlier campaigns used Google Ads to push users searching for legal templates to infected sites, and the latest Huntress findings show similar SEO poisoning on Bing, for queries like “missouri cover utility easement roadway,” that resolve to pages hosting XOR encrypted ZIP payloads.
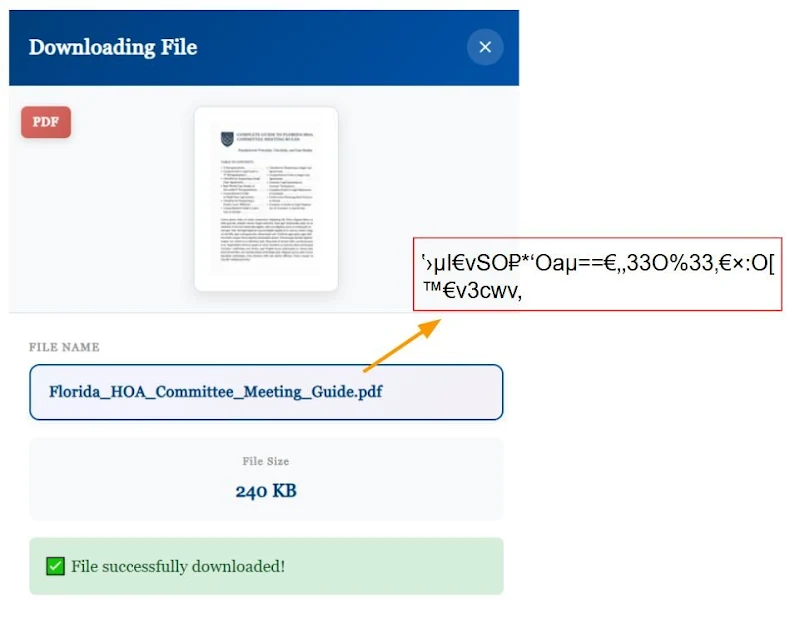
Unlike simple obfuscation, the current campaign embeds a custom WOFF2 font inside the page JavaScript, encoded with Z85 to keep the font compact. Filenames are displayed as unreadable characters in the HTML or when copied from source, but the victim’s browser renders them as legitimate document names, for example Florida_HOA_Committee_Meeting_Guide.pdf. This glyph substitution defeats basic static inspection and slows automated analysis.
Novel evasion techniques, archive tricks, and payload unpacking
Two key evasions are notable, first glyph substitution via a custom WOFF2 font, second a ZIP modification that yields different file types depending on the analysis tool. When the archive is inspected by services like VirusTotal, or unpacked with Python libraries or 7 Zip, it may produce a benign .TXT file. When opened in Windows File Explorer it extracts a valid JavaScript payload, which is the real installer for follow up malware. These layered tricks buy attackers time by masking the payload from automated scanners.
Inside the XOR encrypted archive sits a JavaScript payload designed to deliver Supper, a backdoor that provides SOCKS5 proxying and remote shell capabilities. Supper has been observed handed off to other actors, and in prior chains GootLoader infections led to downstream activity by groups that deploy backdoors such as Supper [aka SocksShell, ZAPCAT], AnyDesk remote access, and ultimately INC ransomware.
Post compromise activity and lateral movement
Huntress recorded cases where initial compromise quickly escalated to hands-on-keyboard activity. Attackers used Supper and legitimate remote management tools to move laterally, including use of Windows Remote Management [WinRM], to reach and compromise Domain Controllers, then create high privilege accounts. The backdoor itself focuses on practical core functions, but its obfuscation and chaining with administrative tools enable broad access and persistence.
Ecosystem links and broader threat context
GootLoader is one component in a larger criminal ecosystem. Microsoft earlier linked GootLoader infections to other operators such as Storm 0494 and Vanilla Tempest, who have used access to deploy Supper and other tools. Supper has been associated in reporting with Interlock RAT and with clusters of ransomware activity, showing how loader infections can feed higher tier operations. This modular, handoff driven model lets multiple groups profit from a single compromise.
Defensive recommendations
To reduce risk from GootLoader and similar loader-based campaigns organizations and site owners should, at minimum:
• Harden WordPress instances, apply plugins and core updates promptly, and remove unused extensions and themes.
• Monitor search and ad traffic referrals, and scan landing pages for unexpected scripts or embedded fonts.
• Block or inspect suspicious ZIP archives at email and web gateways, and use behavioral sandboxing rather than relying solely on static signatures.
• Enforce least privilege on administrative accounts, enable multi factor authentication, and monitor for unusual WinRM or domain controller activity.
• Use endpoint detection that looks for post-exploitation behaviors, like SOCKS proxy creation, lateral movement tools, and rapid account creation.


