A sophisticated new Android Remote Access Trojan (RAT) named “Fantasy Hub” is being marketed as Malware-as-a-Service (MaaS) on Russian-speaking Telegram channels. This malware provides attackers with comprehensive control over infected devices, posing a direct threat to both individual mobile banking users and enterprises with Bring Your Own Device (BYOD) policies.
A Professionalized Cybercrime Service
Fantasy Hub is not just malware; it’s a full-fledged commercial service. Its sellers provide detailed documentation, instructional videos, and a bot-driven subscription model, significantly lowering the barrier to entry for aspiring cybercriminals.
The service is offered through a Telegram bot that manages paid subscriptions. Attackers can pay $200 per week, $500 per month, or $4,500 for an annual subscription. The bot also includes a “builder” feature, allowing customers to upload any clean APK file and receive a trojanized version with the Fantasy Hub payload embedded inside, enabling them to create fake versions of any app.
Advanced Espionage and Fraud Capabilities
Once installed, Fantasy Hub acts as a powerful spying tool. It can harvest SMS messages, contacts, call logs, images, and videos. A key feature is its ability to intercept, reply to, and delete incoming notifications, which is particularly dangerous for bypassing two-factor authentication (2FA) codes sent via SMS.
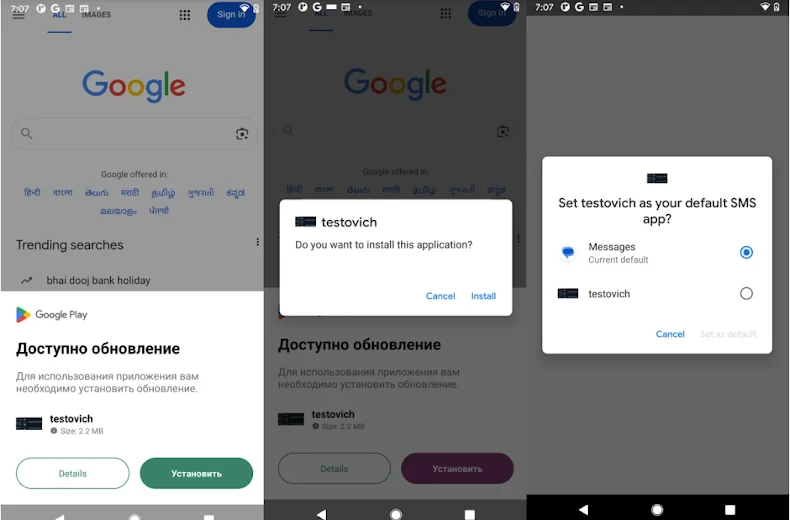
The malware uses sophisticated social engineering to gain extensive permissions. Dropper apps often pose as Google Play updates, tricking users into granting them access. By convincing the user to set it as the default SMS app, it gains multiple powerful permissions at once without needing to request them individually later.
The RAT also uses fake overlays to steal credentials from Russian banking apps like Sberbank and Alfa Bank. Furthermore, it leverages an open-source project to stream live camera and microphone footage from the infected device in real-time using WebRTC technology.
The Growing Menace of Mobile Malware
The discovery of Fantasy Hub coincides with a reported 67% year-over-year increase in Android malware transactions. Zscaler ThreatLabz identified 239 malicious apps on the Google Play Store that were collectively downloaded 42 million times between June 2024 and May 2025.
Other notable malware families like Anatsa, Void, and a new RAT called Xnotice are also actively targeting users. These trojans often masquerade as legitimate utility or job search apps to steal banking credentials and 2FA codes.
In a separate campaign, a malware called NGate is targeting Polish bank users through NFC relay attacks. Victims are tricked into tapping their payment card on the back of their infected Android phone, which stealthily captures the card’s NFC data. This data is then relayed to an attacker at an ATM, enabling them to make unauthorized cash withdrawals without physically possessing the victim’s card.