A threat actor known as Dragon Breath has launched a sophisticated operation using a multi layered tool called RONINGLOADER. This loader is designed to disable major endpoint security products, evade modern defenses, and ultimately deploy a modified version of Gh0st RAT. The campaign mainly targets Chinese speaking victims and relies on trojanized installers that appear to be trusted applications.

How the Attack Begins
According to Elastic Security Labs, the attackers distribute malicious NSIS installers that pretend to be legitimate programs such as Google Chrome or Microsoft Teams. These installers contain two internal components. The first is a harmless installer that sets up the real software, while the second component silently activates the malicious chain.
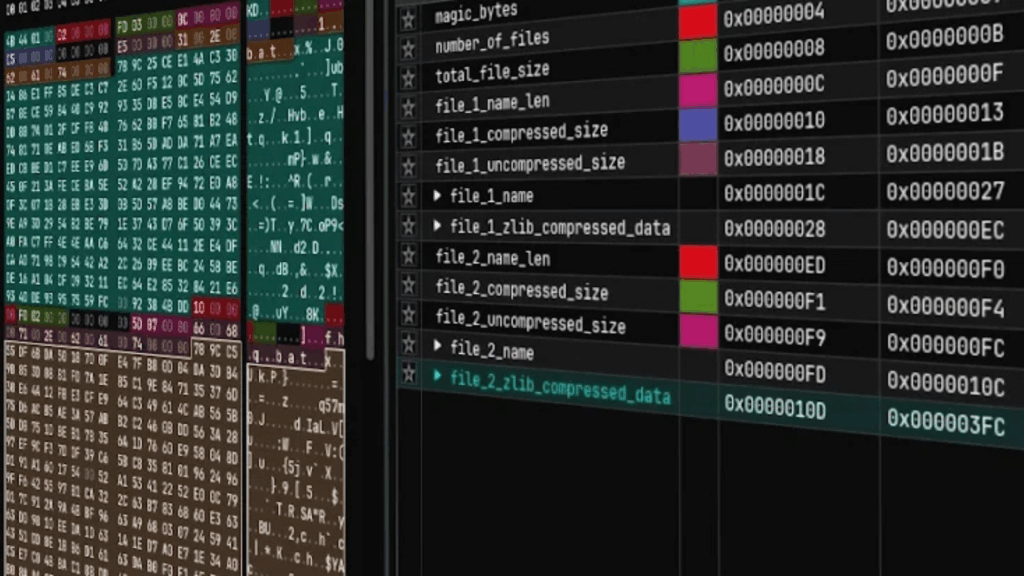
This chain loads a DLL and an encrypted PNG file named tp.png. The DLL extracts hidden shellcode from the PNG and executes it in memory, starting the RONINGLOADER process.
Evasion and Privilege Escalation
RONINGLOADER includes several steps to remain undetected. It loads a clean version of ntdll.dll to bypass userland hooks, attempts to elevate privileges using the runas command, and scans running processes for security software found commonly in the Chinese market such as Microsoft Defender Antivirus, Tencent PC Manager, Kingsoft Internet Security, and Qihoo 360 Total Security.
When these security tools are found, the malware attempts to terminate them. When the target is Qihoo 360 Total Security, the loader performs additional actions. These include changing firewall rules to block all communication, injecting shellcode into the Volume Shadow Copy service, restarting the VSS service, and using a signed driver named ollama.sys to kill three Qihoo 360 related processes through a temporary service named xererre1. After this, firewall rules are restored.
For other security tools, the malware writes the driver to disk, loads it through a temporary service named ollama, terminates the target processes, then deletes the temporary service to hide its activity.
Bypassing Microsoft Defender and WDAC
Once security defenses are disabled, RONINGLOADER executes batch scripts to bypass User Account Control and add firewall rules that block Qihoo 360 connections. Researchers also observed the use of techniques involving Protected Process Light and WerFaultSecure.exe to freeze or disable Microsoft Defender. The loader further manipulates Windows Defender Application Control by introducing a malicious policy that blocks tools from Chinese vendors like Qihoo 360 and Huorong Security.
Final Payload Delivery
The last step involves injecting a rogue DLL into the legitimate Windows tool regsvr32.exe. This helps hide malicious activity while loading a final payload into a privileged system process such as TrustedInstaller.exe or elevation_service.exe. The final malware is a customized version of Gh0st RAT.
Once active, Gh0st RAT connects to a remote server to receive instructions. It can modify registry keys, clear event logs, download files, execute commands through cmd.exe, inject shellcode into svchost.exe, and execute payloads stored on disk. It also captures keystrokes, clipboard content, and window titles, making it a powerful spying tool.
Brand Imitation Campaigns Target Chinese Users
Palo Alto Networks Unit 42 has separately identified two related campaigns distributing Gh0st RAT through large scale brand impersonation. The first operation, called Campaign Trio, ran from February to March 2025 and impersonated i4tools, Youdao, and DeepSeek across more than 2,000 domains.
The second campaign, named Campaign Chorus and active since May 2025, used an even larger set of impersonated brands. More than 40 apps were mimicked, including Sogou browser and QQ Music. Attackers used layered infrastructure with redirection domains that fetch ZIP files from cloud storage, which helps bypass network filtering systems.

The installers in these campaigns include embedded Visual Basic Scripts that decrypt and execute the final payload using DLL side loading. Researchers believe the attackers may be running multiple parallel infrastructures, testing different techniques and targeting various victim groups.